As we look back at 2025, one conclusion is unavoidable: the traditional “castle and moat” security model is officially obsolete. Firewalls, VPNs, and static perimeter controls failed to keep pace with a threat landscape that moved faster, collaborated more efficiently, and increasingly targeted the connective tissue of modern business: identity, access, and the SaaS supply chain.
Attackers no longer needed to break in. Instead, they logged in, inherited trust relationships, or hijacked sessions already deemed legitimate. Identity became the new control plane, and SaaS platforms became the new attack surface.
At the same time, the year was not a one-sided victory for cybercriminals. Global law enforcement demonstrated that coordinated, intelligence-led operations can meaningfully disrupt even the most entrenched cybercrime ecosystems. High-profile arrests, infrastructure seizures, and takedowns proved that cybercrime is not untouchable. Yet despite these wins, the overall volume and velocity of attacks continued to accelerate fueled by AI-assisted tooling and historically low barriers to entry.
Throughout the year, Cynet’s CyOps Cyber Threat Intelligence team tracked these shifts in real time—detecting emerging techniques, developing new detections, and deploying automations across the Cynet platform to blunt attacker momentum. As we close the books on 2025, this roundup highlights the most impactful campaigns, breaches, and operations that defined the year, and set the stage for an era of AI-enabled, professionalized cybercrime in 2026.
Q1: The Erosion of the Perimeter
The first quarter of 2025 made one thing painfully clear: perimeter controls fail quietly until they fail catastrophically.
January | The FortiGate VPN Exposure
The year opened with a stark reminder that legacy infrastructure remains one of the most dangerous forms of technical debt. A massive leak of FortiGate VPN credentials exposed millions of usernames and plain-text passwords, many tied to organizations that believed their remote access was adequately secured.
What Happened: Attackers exploited long-unpatched FortiGate instances and aggregated credentials into searchable databases, indexed by geography and organization. Access was monetized through underground marketplaces, enabling rapid, opportunistic compromise at scale.
Why It Mattered: This incident reinforced a hard truth: VPNs are no longer a security boundary. MFA is not a best practice, it is the bare minimum. Even then, identity-centric attacks increasingly bypass MFA entirely, rendering perimeter-based trust assumptions obsolete.
February | AI-Powered Phishing Scales Up
Social engineering crossed a new threshold with the expansion of ClickFix-style campaigns.
What Changed: Attackers used generative AI to create pixel-perfect fake CAPTCHAs, browser update prompts, and system alerts. These lures bypassed traditional email security by avoiding malicious attachments or links and instead relied on user-initiated actions.
Why It Mattered: AI eliminated the friction that once limited phishing scale. Language localization, tone matching, and brand mimicry became instantaneous. Human judgment—already under strain—became the primary control being exploited.
March | The Ghost of Shadow IT
March highlighted a quieter, more systemic risk: forgotten infrastructure.
What Happened: Attackers targeted Oracle Cloud environments by exploiting CVE-2021-35587—not because it was new, but because it was still present. The affected systems were “zombie” instances: legacy servers spun up years earlier and left unmanaged.
Why It Mattered: This was not a vulnerability management failure—it was an asset visibility failure. Organizations cannot defend systems they do not know exist. In 2025, continuous asset discovery emerged as a foundational security requirement.
Q2: Disruption and Personal Data at Scale
The second quarter underscored two parallel realities: law enforcement can disrupt cybercrime ecosystems, but data theft remains brutally efficient.
April | Law Enforcement Strikes BreachForums
In a significant win, a multinational law enforcement coalition arrested key moderators and operators of BreachForums—the internet’s most notorious marketplace for stolen data.
The Impact: Beyond the headline arrests, authorities seized backend infrastructure and metadata, enabling follow-on investigations. Throughout the spring, dozens of Initial Access Brokers were identified and arrested, disrupting supply chains that fuel ransomware operations.
Why It Mattered: While new forums inevitably emerged, the operation demonstrated that cybercrime platforms are not as anonymous—or resilient—as they appear.

June | The Aflac Data Theft
The healthcare sector suffered one of the largest breaches of the year when Aflac disclosed a data theft impacting 22.65 million individuals.
The Tactics: The Scattered Spider group used targeted SMS phishing to compromise a privileged administrator, bypassing traditional perimeter defenses entirely.
The Cost: This breach exemplified the modern double-extortion model. Attackers weaponized both system access and public exposure, maximizing leverage and reputational damage. Sensitive data—not downtime—became the primary pressure point.
Q3: The Rise of the SaaS Supply Chain
By mid-year, attackers had fully shifted focus from endpoints to platforms.
July | Operation Eastwood: Hitting the Wallet
International law enforcement targeted the NoName057(16) DDoS collective in a novel way.
The Innovation: Rather than simply mitigating attacks, authorities dismantled the group’s “DDoSia” payment infrastructure, severing cryptocurrency incentives that powered its volunteer workforce.
Why It Mattered: This marked a strategic evolution in cybercrime disruption, attacking monetization, not just operations.
August | The Salesforce–Salesloft–Drift Mega-Breach
August delivered the most technically significant incident of 2025: a SaaS-to-SaaS supply chain compromise.
The Method: Attackers abused OAuth trust relationships between Salesforce, Salesloft, and Drift. By compromising a single integration, they inherited downstream access without ever stealing credentials.
The Impact: An estimated 1.5 billion CRM records across hundreds of organizations were exposed. The breach shattered the assumption that SaaS platforms are isolated and proved that trust relationships are now the highest-value targets.
Q4: The Era of Ransomware Cartels
The final quarter revealed what cybercrime looks like at scale: organized, modular, and ruthlessly efficient.
October | The DragonForce Alliance
Ransomware operations consolidated into cartel-like structures, accelerating the professionalization of the cybercrime industry.
What Changed: The DragonForce Alliance unified smaller ransomware groups under shared tooling, infrastructure, and negotiation playbooks.
The Scale: By month’s end, 105 confirmed victims had been claimed—demonstrating that criminal consolidation increases both resilience and impact.
November | Operation Endgame
Law enforcement delivered one of the most consequential blows of the year.
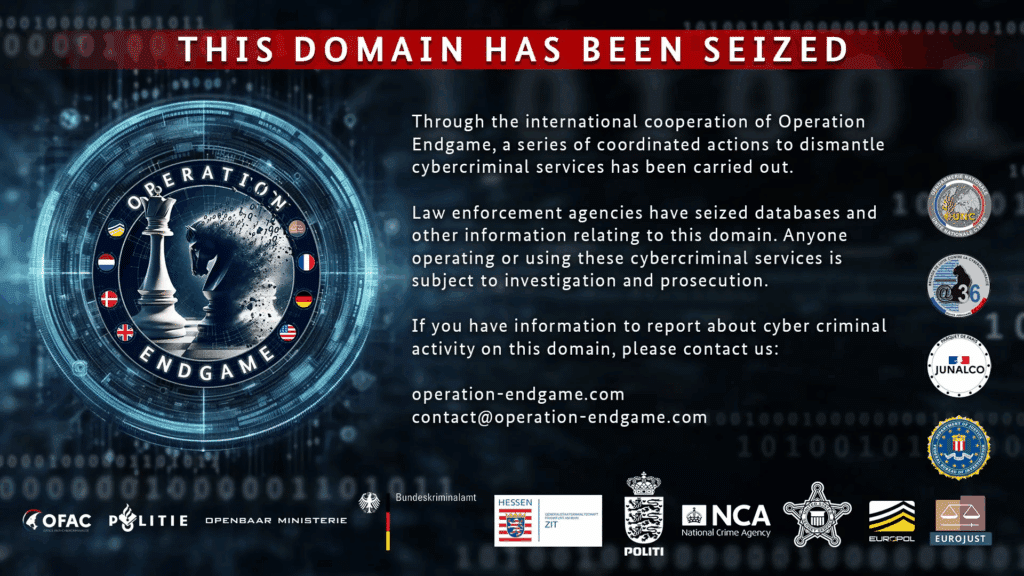
The Result: The takedown of Rhadamanthys infostealer infrastructure disrupted the primary source of credentials feeding ransomware and fraud ecosystems.
Why It Mattered: By starving downstream actors of stolen identities, authorities attacked the cybercrime economy at its root.
December | Identity Hijack Goes Mainstream
The year closed with a decisive shift away from passwords altogether.
ConsentFix: OAuth abuse techniques used to hijack active Azure sessions.
React2Shell: The weaponization of modern application frameworks at unprecedented speed.
The New Reality: Time-to-exploit collapsed. In late 2025, attackers routinely moved from disclosure to full compromise in under four hours.
What 2025 Means for Your 2026 Strategy
If 2025 taught us anything, it’s this: identity is the new perimeter. When attackers can hijack sessions, abuse OAuth trust, and bypass MFA, traditional defenses are no longer sufficient.
Key Takeaways for 2026
Shift to Token Security: Monitor OAuth tokens, sessions, and delegated access—not just credentials.
Enforce SaaS Governance: Audit and continuously review every third-party integration across cloud platforms.
Speed Is Security: If your remediation window for critical vulnerabilities exceeds four hours, you are already behind.
The threat landscape will continue to accelerate. But organizations that prioritize identity visibility, SaaS posture management, and rapid response will be far better positioned to withstand what 2026 brings.
Interested in ongoing cyber threat intelligence? Subscribe to our Threat Research Newsletter on LinkedIn for monthly insights drawn directly from our Cyber Threat Intelligence reporting.