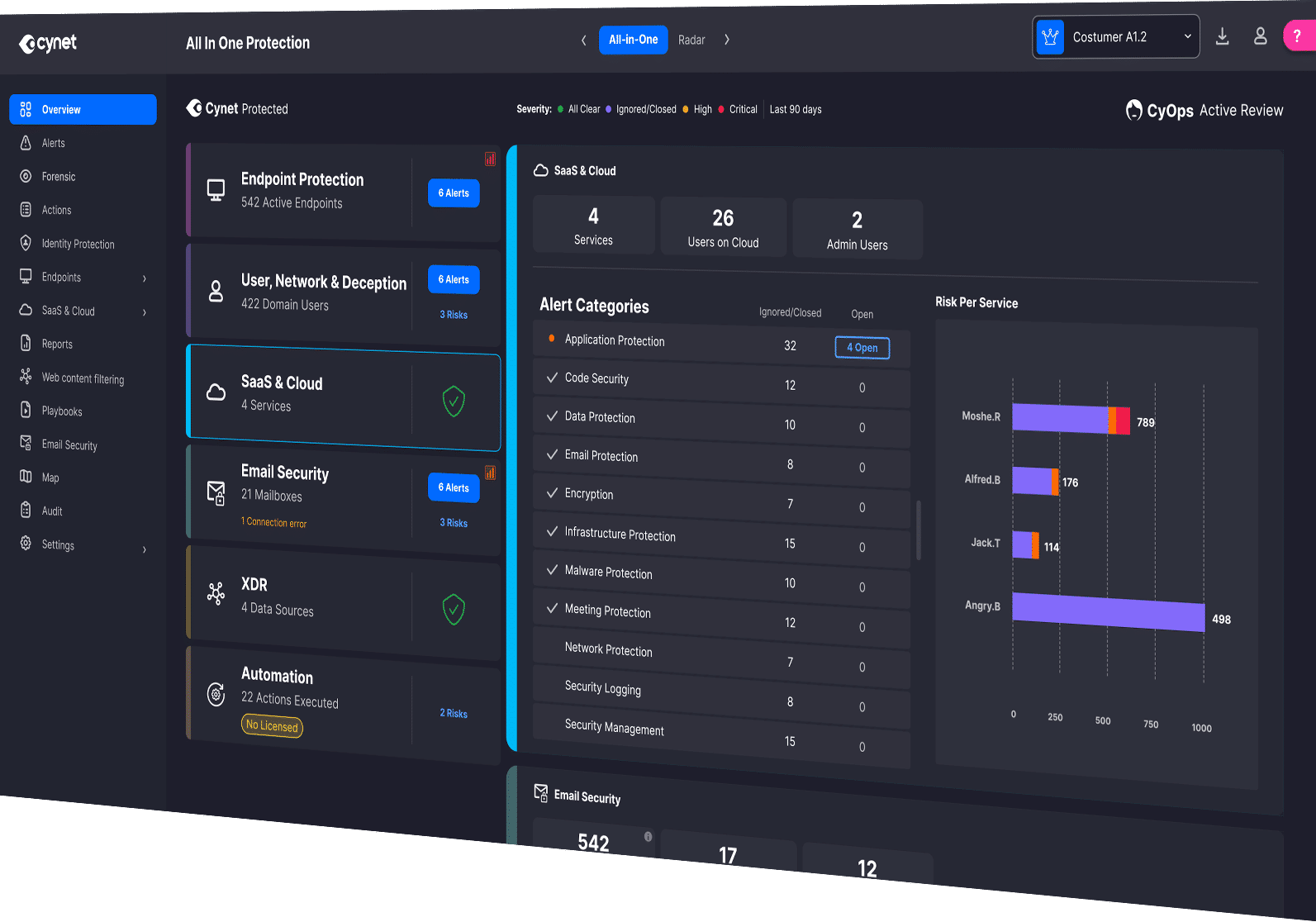
Unified Protection for Every Cloud and SaaS Environment
SaaS & Cloud Security
Cynet’s SaaS and Cloud Security Posture Management (SSPM & CSPM) delivers complete visibility, proactive risk management, and automated remediation across the cloud and SaaS ecosystem. It’s built directly into the Cynet platform, working seamlessly with endpoint, user, identity, and network protection, all powered by CyAI and backed 24x7 by CyOps experts.












Top MITRE ATT&CK Performance
For the first time, the 2025 ATT&CK Evaluations included an assessment of cloud capabilities, with AWS-focused testing. Cynet’s CSPM and SSPM solutions delivered exceptional results with 100% Detection Visibility, 100% Protection, and 100% Technique-Level Coverage, with zero false positives, and zero configuration changes in the Initial Run.
Not a single vendor performed better than Cynet.
Cynet automatically identifies, prioritizes, and remediates risks across all SaaS and cloud environments, giving you full visibility, control, and continuous protection, without the complexity of managing separate tools.

Full Visibility Across Cloud and SaaS Assets
See every connected user, workload, and service across Microsoft 365, AWS, Azure, Google Workspace, and more. Instantly identify exposed subdomains, IPs, and misconfigured assets.

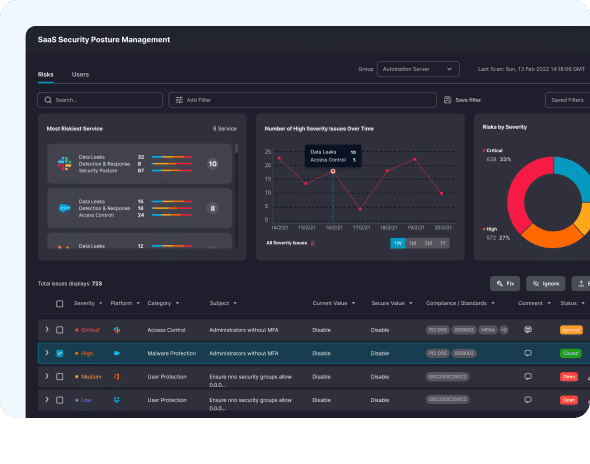
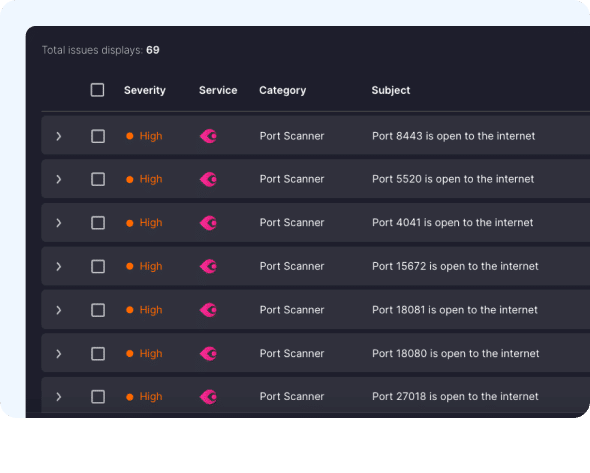
Automated Risk Detection and Prioritization
Continuously scan for risks like excessive permissions, public buckets, weak configurations, or third-party app vulnerabilities. Cynet prioritizes what matters most, based on impact and exploitability.

One-Click Remediation
Drill down to the root cause of every risk and remediate it directly from the Cynet console. Apply best-practice configurations automatically and close security gaps fast.

Compliance and Audit Readiness
Map configuration settings against major frameworks like NIST, PCI DSS, HIPAA, and ISO 27001 to maintain continuous compliance and simplify audits with pre-built reporting.

Continuous Monitoring and Alerts
Receive daily posture summaries and real-time notifications for any new risks or configuration changes that introduce vulnerabilities.

24x7 MDR Expert Coverage
CyOps, Cynet’s team of 24x7 MDR security experts continuously monitor the environment to detect and contain threats before they spread, covering endpoints, cloud, and SaaS in a single workflow.
01
Automatically Discover SaaS Risks
Gain comprehensive SaaS security risk detection and remediation capabilities directly in the Cynet dashboard. Continuously monitor configuration settings across all SaaS applications and hunt for security posture issues in one place without needing to access additional tools or systems.
02
Fix Issues with a Single Click
Cynet removes the guesswork by providing best practice configuration settings and auto-remediation capabilities that allow you to quickly take action to correct issues before they become security events.
03
Simplify Compliance
Ensure compliance by automatically aligning critical SaaS and cloud security settings to identify security risks that are in accordance with major compliance standards, including CIS, Cyber Essentials, FFIEC, GDPR, HIPAA, ISO27001, NIS2, NIST, PCI and more.
See What Complete Cloud Confidence Looks Like
Experience Cynet SaaS & Cloud Security in Action
Request a demo to see how Cynet gives you unified protection, automated remediation, and total peace of mind, across every SaaS app and Cloud environment.

