Unified. AI-Powered. Expert-Backed.
Cynet unifies every critical layer of cybersecurity into one AI-powered platform that detects, investigates, and responds automatically—backed 24x7 by real security experts.
Modern Security Demands a Unified Platform
Today’s threats move faster than most teams can react. Disconnected tools create blind spots, slow response, and higher costs. Cynet fixes that.
By unifying protection, detection, and response in a single platform, Cynet helps you stay ahead of every threat while simplifying security. With Cynet, you will:
-
Detect and stop advanced threats automatically
-
Eliminate tool sprawl and integration headaches
-
Respond in seconds, not hours.
-
Protect every part of the environment with one solution
-
Gain 24x7 expert protection from CyOps MDR
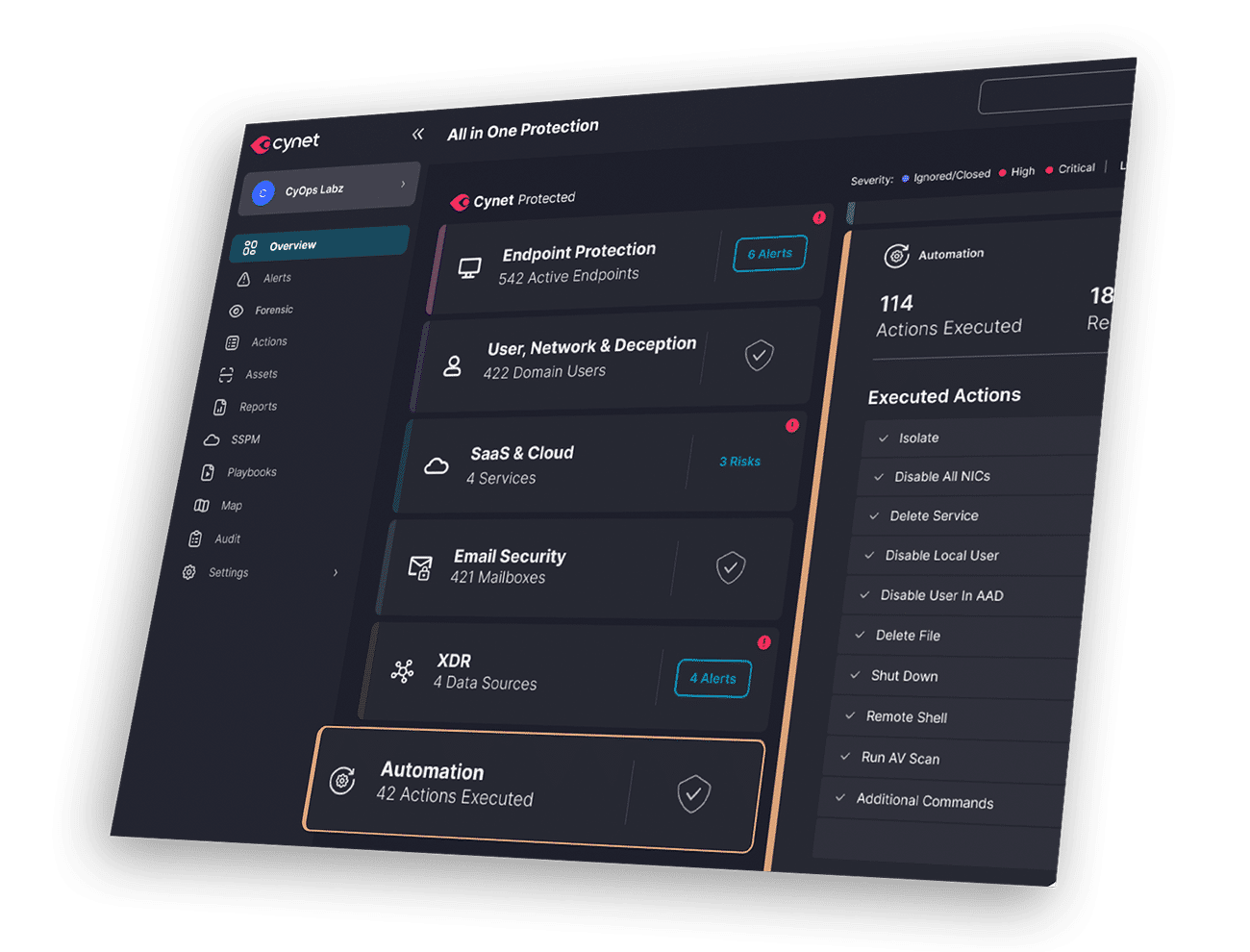
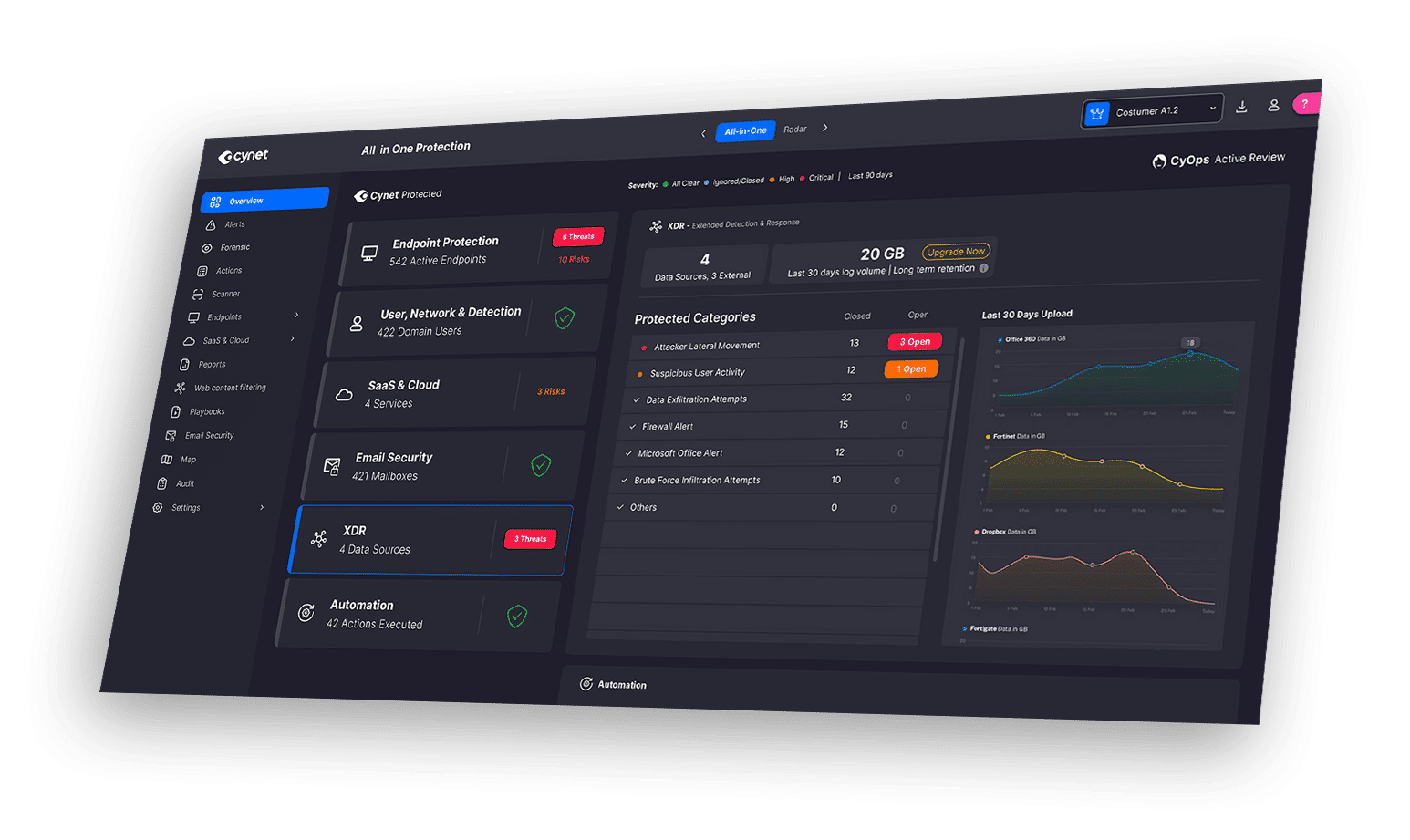
Complete Protection in One Unified Platform
Cynet replaces the complexity of managing separate point products with a single, unified platform that protects everything from endpoint to cloud.
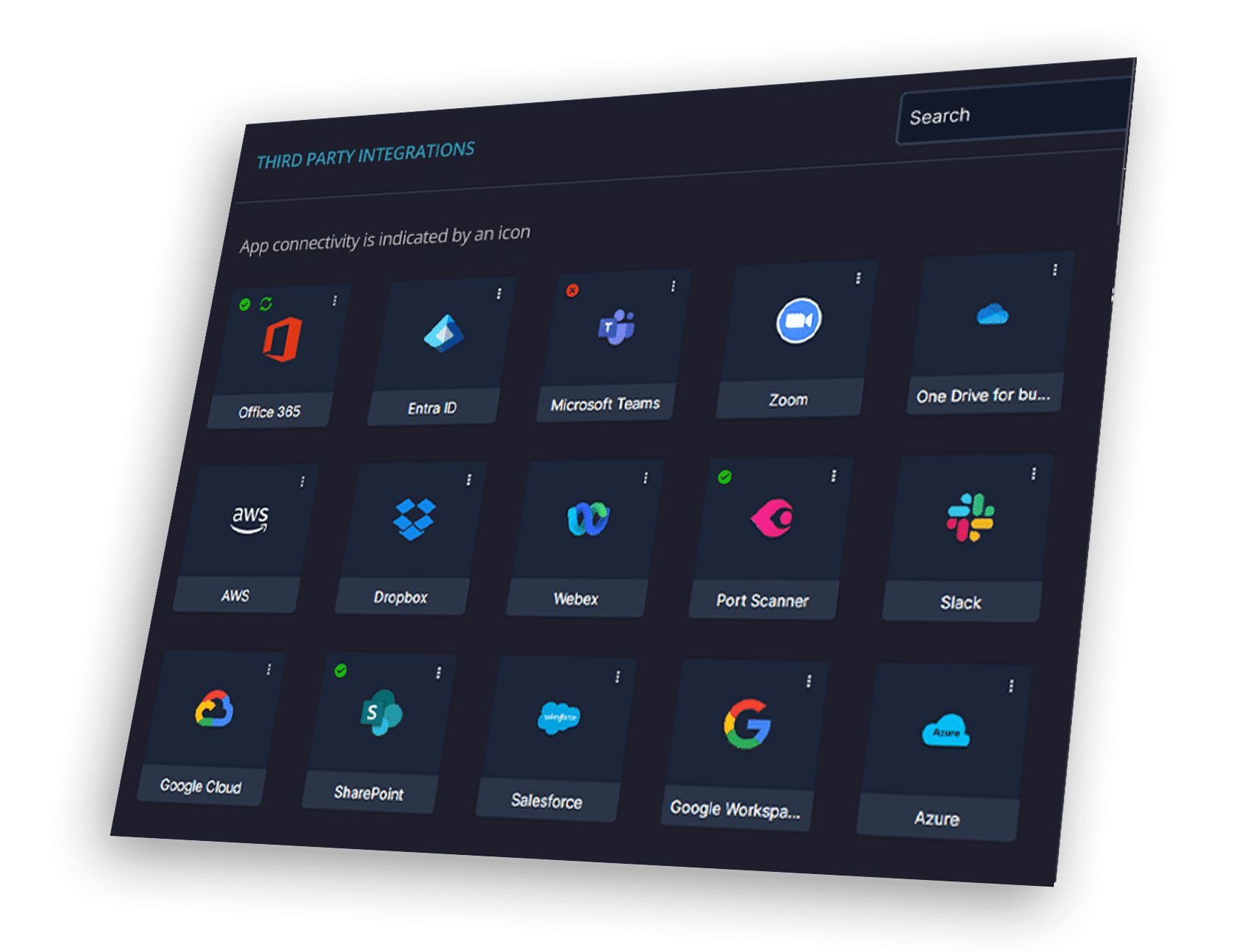
Integrations and APIs
Cynet connects with the tools IT and Security teams already use (RMM, PSA, Identity, SIEM, Cloud, SOAR and more) to deliver unified visibility and control without changing the tech stack.
Through hundreds of APIs and 80+ built-in integrations with more than 50+ data sources, Cynet ingests data and orchestrates response across the entire IT and security ecosystem.

CyAI
CyAI continuously learns from millions of real-world threats to predict and stop attacks before they begin. It connects the dots across every part of your environment, automating investigation and response, while eliminating noise so IT and security teams can focus on what matters most.
CyOps 24x7 MDR
Real people. Real protection. Real results.
CyOps is Cynet’s 24x7 Managed Detection and Response (MDR) team, operating as an extension of your own. These dedicated experts monitor the environment, investigate alerts, and act in real-time when threats are detected.
Security Orchestration, Automation, and Response (SOAR)
Cynet’s built-in automation and SOAR capabilities reduce response time from hours to seconds. With predefined playbooks, Cynet automatically isolates infected systems, blocks malicious traffic, and eliminates threats across the environment.


Security Solutions
Automate detection, response, and remediation with 24x7 expert-backed security that protects the entire environment including endpoints, users, networks, identities, email, mobile, cloud, and SaaS from a single unified platform.
-
Endpoint Security
-
Network Security
-
User & Identity Protection
-
Mobile Protection
-
Cloud Security
-
Email Security
-
SaaS Security
Simple Management
A single, intuitive, multi-tenant console provides full visibility and control across the organization.
Proven Speed and Results
Cynet combines AI, automation, and human expertise to deliver unmatched outcomes:
Customer satisfaction rating
Detection to containment
MITRE-Validated Detection, Visibility, and Technique Coverage with zero false positives
Resolve threats 50x faster with less manual incident handling
of advanced threats remediated automatically
Continuous Innovation
Threats don’t wait. Neither does Cynet. We continuously advance our AI models, expand integrations, and deliver new solutions and automation capabilities that help organizations stay protected as threats evolve.
One platform. One agent. One team. Complete protection.
Cynet delivers the power of an AI SOC Agent in a simple, unified platform that gives IT and security teams peace of mind and confidence in every decision.

