Executive Summary
On May 11, 2026, a new wave of Shai-Hulud activity was discovered, impacting the npm and PyPI ecosystems through a sophisticated supply chain worm with JavaScript and Python execution paths. The campaign represents a significant compromise of software development and release processes, with reported impact across more than 170 packages, according to public reporting. Impacted packages include backdoored TanStack components and packages associated with OpenSearch, Mistral AI, Guardrails AI, UiPath, Squawk, and others.
The core objective remains consistent with previous Shai-Hulud activity: stealing credentials from developer machines and CI/CD runners, then using those credentials to compromise additional packages, repositories, and environments. What changed in this wave is the scale, the release path, and the execution model. The malware is designed to execute inside build systems, abuse npm lifecycle scripts, install or invoke the Bun runtime, steal npm, GitHub, cloud, Kubernetes, Vault, and CI/CD credentials, and use authorized publishing paths to push new compromised packages.
One of the most concerning aspects of this wave is the abuse of legitimate release pipelines. Malicious packages could be published through normal automation, making them harder for developers, security tools, and automated workflows to identify as suspicious.
Cynet helps organizations reduce risk from Mini Shai-Hulud and related supply chain attacks on endpoints where Cynet is installed, providing layered visibility, detection, prevention, and response for suspicious activity associated with compromised dependencies and software supply chain threats.
Cynet Research and CyOps teams are actively monitoring and investigating Mini Shai-Hulud activity, researching emerging indicators and attack behaviors, and hunting for suspicious activity across customer environments.
New Significant Risk: AI-Driven and Automated Development Workflows
Mini Shai-Hulud highlights a growing risk in AI-driven and automated development workflows. Coding agents, build systems, and automated dependency tools can install, update, or recommend packages with limited human review. In these environments, a compromised dependency may be pulled into a project, executed automatically, and granted access to sensitive tokens, configuration files, or CI/CD credentials.
The concern is not only the malware itself, but the speed at which modern development workflows can introduce it. AI coding agents and automated build systems may install or update packages before a human review the risk. In that scenario, a compromised dependency can execute quickly, access sensitive credentials, and potentially spread through established development and release workflows.
Cynet Detection: AI-Assisted Dependency Installation
During one of the Shai-Hulud supply chain attack waves, Cynet observed activity showing how AI-assisted development environments can become part of the exposure path. The observed process chain involved a Cursor helper plugin launching Node.js and npm to install a GitHub-hosted package dependency flagged in the context of Shai-Hulud-related activity:
Cursor Helper (Plugin) → /usr/bin/env node → npm install github:asyncapi/cli#2efa4dff59bc3d3cecdf897ccf178f99b115d63d
- Parent process: Cursor Helper (Plugin)
- Runtime launched: /usr/bin/env node
- Package manager action: npm install
- GitHub dependency: github:asyncapi/cli
- Pinned commit: 2efa4dff59bc3d3cecdf897ccf178f99b115d63d
This activity is significant because it shows how modern developer tools can initiate dependency installation directly from GitHub, including pinned commits, with limited user visibility or review. In the context of a supply chain attack, this type of workflow can allow a compromised or suspicious dependency to be introduced and executed quickly inside a developer environment.
This activity should be treated as high-signal suspicious behavior and investigated in context, especially for follow-on script execution, Bun activity, credential access, or package installation artifacts
Technical Details
The supply chain infection starts when a compromised npm or PyPI package is installed or loaded by a developer machine, build system, or CI/CD runner. In npm projects, malicious code can run automatically during dependency installation through package lifecycle scripts or malicious package content. In PyPI projects, malicious Python code may be executed when the package is imported or loaded.
The campaign includes two main technical paths: a JavaScript/npm path and a Python/PyPI path. Both paths focus on credential theft and exfiltration, but they differ in execution method, platform support, payload structure, and follow-on capabilities.
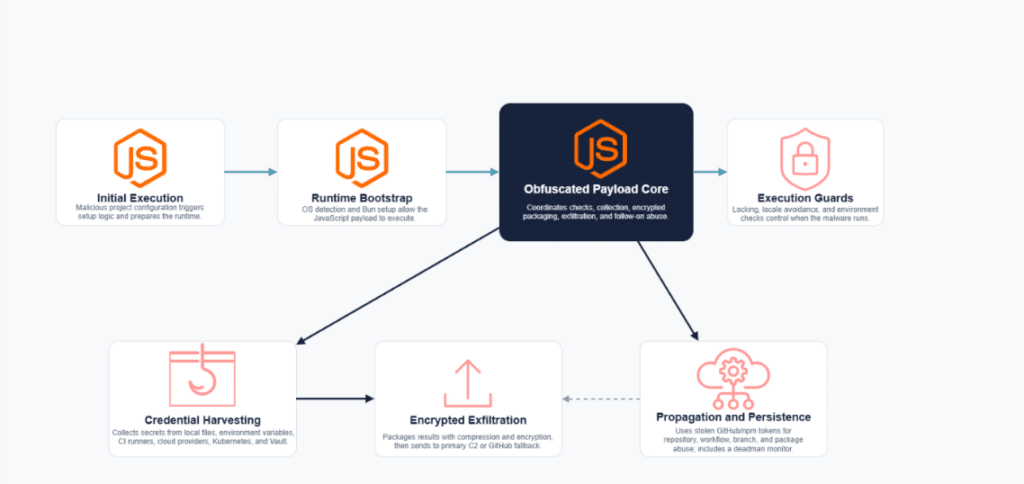
JavaScript/npm Execution Path
The JavaScript payload is designed to work on Windows, Linux, and macOS systems. It includes a malicious JSON configuration file that executes setup.mjs. The setup script detects the operating system and installs or invokes the Bun runtime, which is required for later-stage execution. Once Bun is available, the loader runs router_init.js, which contains the main obfuscated malware payload. Before executing its core functionality, the malware performs several sanity checks. It creates an operating-system-dependent lock file in a temporary directory to prevent repeated execution, checks locale and time zone settings to avoid Russian-language environments, and determines whether it is running inside a CI pipeline or on a personal machine.
The payload is designed to steal secrets using regular-expression matching and direct collection from local and cloud sources. It searches for NPM tokens, GitHub access tokens, GitHub Actions and session tokens, Kubernetes JWTs, AWS access keys and secret keys, AWS session tokens, Azure keys and secrets, Slack tokens, Vault tokens, and generic secrets identified by keywords such as password, pass, token, and key.
Beyond pattern matching, the malware targets secret stores and cloud sources directly. It attempts to collect GitHub Actions repository secrets, GitHub runner in-memory secrets from Runner.Worker, AWS Secrets Manager values, AWS SSM Parameter Store parameters, AWS STS identity and account metadata, Kubernetes Secrets across accessible namespaces, and HashiCorp Vault KV secrets from mounted and common paths such as secret, kv, cubbyhole, and secret-v2.
The malware also searches local files for credentials and sensitive configuration data. Targeted files and sources include AWS, Azure, GCP, Kubernetes, and Terraform credentials; .npmrc, .pypirc, Git credentials, .netrc, Docker configs, SSH keys and configs, environment files, database configuration files, AI and developer-tool configurations such as Claude and MCP settings, VPN client configurations, application session stores, shell history, database history, container secrets, and cryptocurrency wallet files.
The JavaScript variant also includes broader supply chain functionality. It targets NPM package tokens that can be used to mutate and republish packages, as well as GitHub tokens that can be used for repository creation, workflow abuse, and branch mutation. This gives the JavaScript path stronger worm-like behavior and enables the compromise to spread beyond the initially infected machine.
Finally, some reported JavaScript activity includes persistence through a deadman-switch mechanism. It installs a monitor that checks whether a stolen GitHub token remains valid and commits data with the prefix IfYouRevokeThisTokenItWillWipeTheComputerOfTheOwner. If the token later becomes invalid, the monitor executes a destructive command intended to delete the infected user’s home directory.
Python/PyPI Execution Path
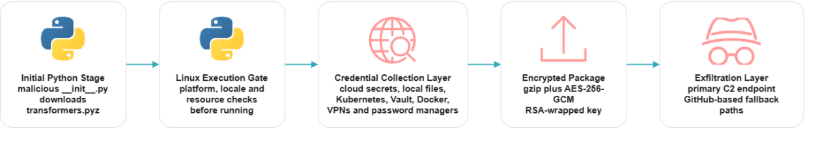
The Python path follows a different execution model. The compromised PyPI package contains a malicious __init__.py file that downloads the next stage, transformers.pyz. Unlike the JavaScript path, which can run on Windows, Linux, and macOS systems, this Python variant is gated to Linux systems.
Before continuing, the Python payload performs several pre-execution checks. It exits if the host is not Linux, if the system language appears to be Russian, or if the machine has two or fewer CPU cores. It also attempts to install the cryptography package if it is missing and suppresses standard output and error streams to reduce visible activity.
Once running, the Python payload acts as a credential aggregator. It dynamically loads collector modules and runs them in parallel, collecting data from local files, environment variables, cloud credentials, Kubernetes configurations, Vault instances, Docker containers, VPN tooling, and password managers such as 1Password, Bitwarden, pass, and gopass.
The cloud-focused collectors target AWS, Azure, and GCP. The AWS collector searches environment variables, local credential files, and EC2 instance metadata, then attempts to enumerate AWS Secrets Manager and SSM Parameter Store values. The Azure collector uses service principal credentials, client certificate authentication, Azure CLI token caches, or managed identity tokens to access subscriptions and Azure Key Vault secrets. The GCP collector uses service account files, application default credentials, refresh tokens, or metadata tokens to access Google Secret Manager.
The payload also targets Kubernetes and Vault environments. The Kubernetes collector reads local kubeconfig files and in-cluster service account tokens, then attempts to enumerate and decode secrets across accessible namespaces and contexts. The Vault collector uses tokens from environment variables, local token files, AppRole credentials, or the Vault CLI, then walks KV secret engines to retrieve stored secret values.
Collected data is compressed and encrypted before exfiltration. The payload uses AES-256-GCM for the collected data and RSA-OAEP with an embedded public key to wrap the AES key. It first attempts to send the encrypted package to a hardcoded command-and-control endpoint. If that fails, it can query GitHub commit search for signed FIRESCALE messages and use a verified alternate endpoint.
As a fallback exfiltration path, the Python payload searches the collected data for GitHub tokens. If it finds a usable token, it creates a public GitHub repository with a randomized name and uploads the encrypted results as results.json.
JavaScript vs. Python Behavior
The JavaScript and Python paths share the same objective: credential harvesting and follow-on compromise. However, their behavior differs.
The JavaScript variant has broader supply chain functionality. It supports cross-platform execution, uses Bun to run later-stage payloads, targets npm and GitHub publishing access, and includes capabilities for npm package mutation, GitHub Actions abuse, GitHub branch modification, and persistence.
The Python variant is narrower in platform support because it is gated to Linux, but it is highly focused on credential harvesting and encrypted exfiltration. It adds first-class collectors for Azure Key Vault and GCP Secret Manager, in addition to AWS, Kubernetes, Vault, local files, Docker environments, VPN configurations, and password managers.
This reinforces why dependency installation, and package import should be treated as security-sensitive events in automated development environments.
Mitigations and Remediations
- Ensure you pin the version of the malicious packages to one prior to the infection (e.g. my_package==1.0.0).
- Follow the announcements of the infected packages’ authors.
- Scan your repositories to ensure that you aren’t affected by the malware. If you are infected, correctly identify the variant.
- For the Python variant:
- Remove the persistency service.
- Remove the identified malicious files.
- Rotate the exposed tokens, secrets and passwords.
- For the JS variant:
- Remove the deadman switch service.
- Remove the identified malicious files.
- Rotate the exposed tokens, secrets and passwords.
IOCs:
Artifacts:
| Artifact | Type | Value |
| router_init.js | SHA256 | ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c |
| setup.mjs | SHA256 | 2258284d65f63829bd67eaba01ef6f1ada2f593f9bbe41678b2df360bd90d3df |
| opensearch_init.js | SHA1 | 820fa07a7328b6cf2b417078e103721d4d8f2e79 |
| tanstack_runner.js | SHA256 | 2ec78d556d696e208927cc503d48e4b5eb56b31abc2870c2ed2e98d6be27fc96 |
| transformers.pyz | SHA256 | 5245eb032e336b85cff0dbb3450d591826bf2ef214fd30d7eba1a763664e151b |
| __init__.py | SHA256 | 6dbaa43bf2f3c0d3cddbca74967e952da563fb974c1ef9d4ecbb2e58e41fe81b |
Domains:
- git-tanstack[.]com
- api[.]masscan[.]cloud
- filev2[.]getsession[.]org
- seed1[.]getsession[.]org
- seed2[.]getsession[.]org
- seed3[.]getsession[.]org
Package Versions:
| Ecosystem | Name | Version |
| npm | @uipath/filesystem | 1.0.1 |
| npm | @uipath/solution-packager | 0.0.35 |
| npm | @uipath/apollo-react | 4.24.5 |
| npm | cross-stitch | 1.1.3, 1.1.4, 1.1.5, 1.1.6, 1.1.7 |
| npm | @tanstack/virtual-file-routes | 1.161.10, 1.161.13 |
| npm | @uipath/packager-tool-bpmn | 0.0.9 |
| npm | @tanstack/router-vite-plugin | 1.166.53, 1.166.56 |
| npm | @tanstack/router-generator | 1.166.45, 1.166.48 |
| npm | @uipath/codedagent-tool | 1.0.1 |
| npm | mbt | 1.2.48 |
| npm | @tanstack/react-start-client | 1.166.51, 1.166.54 |
| npm | @beproduct/nestjs-auth | 0.1.2, 0.1.3, 0.1.4, 0.1.5, 0.1.6, 0.1.7, 0.1.8, 0.1.9, 0.1.10, 0.1.11, 0.1.12, 0.1.13, 0.1.14, 0.1.15, 0.1.16, 0.1.17, 0.1.18, 0.1.19 |
| npm | @uipath/packager-tool-apiworkflow | 0.0.19 |
| npm | git-branch-selector | 1.3.3, 1.3.4, 1.3.5, 1.3.6, 1.3.7 |
| npm | @uipath/packager-tool-case | 0.0.9 |
| npm | @uipath/tasks-tool | 1.0.1 |
| npm | @draftlab/db | 0.16.1, 0.16.2 |
| npm | @uipath/insights-sdk | 1.0.1 |
| npm | @mesadev/saguaro | 0.4.22 |
| npm | @mesadev/sdk | 0.28.3 |
| npm | @cap-js/sqlite | 2.2.2 |
| npm | @uipath/platform-tool | 1.0.1 |
| npm | @uipath/apollo-core | 5.9.2 |
| npm | @draftauth/client | 0.2.1, 0.2.2 |
| npm | @uipath/gov-tool | 0.3.1 |
| npm | @uipath/vss | 0.1.6 |
| npm | @uipath/rpa-tool | 0.9.5 |
| npm | @uipath/solution-tool | 1.0.1 |
| npm | @uipath/maestro-tool | 1.0.1 |
| npm | @tallyui/pos | 0.1.1, 0.1.2, 0.1.3 |
| npm | @tanstack/eslint-plugin-router | 1.161.9, 1.161.12 |
| npm | @tanstack/react-start-rsc | 0.0.47, 0.0.50 |
| npm | @uipath/vertical-solutions-tool | 1.0.1 |
| npm | ts-dna | 3.0.1, 3.0.2, 3.0.3, 3.0.4, 3.0.5 |
| npm | @squawk/navaids | 0.4.2, 0.4.3, 0.4.4, 0.4.5, 0.4.6 |
| npm | @tallyui/theme | 0.2.1, 0.2.2, 0.2.3 |
| npm | @uipath/rpa-legacy-tool | 1.0.1 |
| npm | @tanstack/router-ssr-query-core | 1.168.3, 1.168.6 |
| pypi | guardrails-ai | 0.10.1 |
| npm | @squawk/procedures | 0.5.2, 0.5.3, 0.5.4, 0.5.5, 0.5.6 |
| npm | @tanstack/vue-start | 1.167.61, 1.167.64 |
| npm | @tanstack/react-router-devtools | 1.166.16, 1.166.19 |
| npm | @tanstack/zod-adapter | 1.166.12, 1.166.15 |
| npm | @uipath/insights-tool | 1.0.1 |
| npm | @tanstack/arktype-adapter | 1.166.12, 1.166.15 |
| pypi | mistralai | 2.4.6 |
| npm | @uipath/solutionpackager-sdk | 1.0.11 |
| npm | @tallyui/core | 0.2.1, 0.2.2, 0.2.3 |
| npm | @tanstack/solid-router-devtools | 1.166.16, 1.166.19 |
| npm | @tanstack/start-client-core | 1.168.5, 1.168.8 |
| npm | @uipath/integrationservice-tool | 1.0.2 |
| npm | intercom-client | 7.0.4 |
| npm | @tanstack/start-plugin-core | 1.169.23, 1.169.26 |
| npm | @squawk/navaid-data | 0.6.4, 0.6.5, 0.6.6, 0.6.7, 0.6.8 |
| npm | @squawk/airport-data | 0.7.4, 0.7.5, 0.7.6, 0.7.7, 0.7.8 |
| npm | @uipath/access-policy-sdk | 0.3.1 |
| npm | @tanstack/react-start-server | 1.166.55, 1.166.58 |
| npm | @squawk/units | 0.4.3, 0.4.4, 0.4.5, 0.4.6, 0.4.7 |
| npm | @tanstack/vue-start-server | 1.166.50, 1.166.53 |
| npm | @ml-toolkit-ts/xgboost | 1.0.3, 1.0.4 |
| npm | git-git-git | 1.0.8, 1.0.9, 1.0.10, 1.0.11, 1.0.12 |
| npm | cmux-agent-mcp | 0.1.3, 0.1.4, 0.1.5, 0.1.6, 0.1.7, 0.1.8 |
| npm | @taskflow-corp/cli | 0.1.24, 0.1.25, 0.1.26, 0.1.27, 0.1.28, 0.1.29 |
| npm | @uipath/packager-tool-webapp | 1.0.6 |
| npm | @uipath/ui-widgets-multi-file-upload | 1.0.1 |
| npm | @mistralai/mistralai-azure | 1.7.1, 1.7.2, 1.7.3 |
| npm | @squawk/icao-registry-data | 0.8.4, 0.8.5, 0.8.6, 0.8.7, 0.8.8 |
| npm | @tanstack/valibot-adapter | 1.166.12, 1.166.15 |
| npm | @tanstack/vue-start-client | 1.166.46, 1.166.49 |
| npm | @squawk/airway-data | 0.5.4, 0.5.5, 0.5.6, 0.5.7, 0.5.8 |
| npm | @mesadev/rest | 0.28.3 |
| npm | @uipath/auth | 1.0.1 |
| npm | @uipath/uipath-python-bridge | 1.0.1 |
| npm | @tanstack/solid-start-client | 1.166.50, 1.166.53 |
| npm | @tanstack/eslint-plugin-start | 0.0.4, 0.0.7 |
| npm | @supersurkhet/cli | 0.0.2, 0.0.3, 0.0.4, 0.0.5, 0.0.6, 0.0.7 |
| npm | @uipath/packager-tool-workflowcompiler | 0.0.16 |
| npm | @cap-js/postgres | 2.2.2 |
| npm | @uipath/agent.sdk | 0.0.18 |
| npm | @uipath/data-fabric-tool | 1.0.2 |
| npm | @squawk/icao-registry | 0.5.2, 0.5.3, 0.5.4, 0.5.5, 0.5.6 |
| npm | @uipath/common | 1.0.1 |
| npm | @tallyui/connector-vendure | 1.0.1, 1.0.2, 1.0.3 |
| npm | @uipath/packager-tool-workflowcompiler-browser | 0.0.34 |
| npm | @tanstack/nitro-v2-vite-plugin | 1.154.12, 1.154.15 |
| npm | @tallyui/connector-medusa | 1.0.1, 1.0.2, 1.0.3 |
| npm | safe-action | 0.8.3, 0.8.4 |
| npm | @tanstack/router-core | 1.169.5, 1.169.8 |
| npm | @uipath/codedagents-tool | 0.1.12 |
| npm | @cap-js/db-service | 2.10.1 |
| npm | @uipath/api-workflow-tool | 1.0.1 |
| npm | @tanstack/router-plugin | 1.167.38, 1.167.41 |
| npm | @tanstack/vue-router-devtools | 1.166.16, 1.166.19 |
| npm | @uipath/widget.sdk | 1.2.3 |
| npm | @tallyui/storage-sqlite | 0.2.1, 0.2.2, 0.2.3 |
| npm | @uipath/robot | 1.3.4 |
| npm | @uipath/context-grounding-tool | 0.1.1 |
| npm | @uipath/codedapp-tool | 1.0.1 |
| npm | @uipath/packager-tool-flow | 0.0.19 |
| pypi | lightning | 2.6.2, 2.6.3 |
| npm | @uipath/flow-tool | 1.0.2 |
| npm | @uipath/identity-tool | 0.1.1 |
| npm | @uipath/resource-tool | 1.0.1 |
| npm | @uipath/apollo-wind | 2.16.2 |
| npm | @tallyui/components | 1.0.1, 1.0.2, 1.0.3 |
| npm | @squawk/fixes | 0.3.2, 0.3.3, 0.3.4, 0.3.5, 0.3.6 |
| npm | @tallyui/database | 1.0.1, 1.0.2, 1.0.3 |
| npm | @squawk/airways | 0.4.2, 0.4.3, 0.4.4, 0.4.5, 0.4.6 |
| npm | @tanstack/solid-router | 1.169.5, 1.169.8 |
| npm | @tanstack/solid-start | 1.167.65, 1.167.68 |
| npm | @uipath/resources-tool | 0.1.11 |
| npm | @uipath/test-manager-tool | 1.0.2 |
| npm | @uipath/integrationservice-sdk | 1.0.2 |
| npm | @squawk/airspace-data | 0.5.3, 0.5.4, 0.5.5, 0.5.6, 0.5.7 |
| npm | @tanstack/vue-router-ssr-query | 1.166.15, 1.166.18 |
| npm | @uipath/llmgw-tool | 1.0.1 |
| npm | @tanstack/start-static-server-functions | 1.166.44, 1.166.47 |
| npm | @uipath/case-tool | 1.0.1 |
| npm | @squawk/airports | 0.6.2, 0.6.3, 0.6.4, 0.6.5, 0.6.6 |
| npm | @squawk/airspace | 0.8.1, 0.8.2, 0.8.3, 0.8.4, 0.8.5 |
| npm | @uipath/ap-chat | 1.5.7 |
| npm | @ml-toolkit-ts/preprocessing | 1.0.2, 1.0.3 |
| npm | @uipath/project-packager | 1.1.16 |
| npm | @tanstack/router-devtools-core | 1.167.6, 1.167.9 |
| npm | wot-api | 0.8.1, 0.8.2, 0.8.3, 0.8.4 |
| npm | @tanstack/start-storage-context | 1.166.38, 1.166.41 |
| npm | @uipath/packager-tool-connector | 0.0.19 |
| npm | @tanstack/solid-router-ssr-query | 1.166.15, 1.166.18 |
| npm | nextmove-mcp | 0.1.3, 0.1.4, 0.1.5, 0.1.6, 0.1.7 |
| npm | @uipath/telemetry | 0.0.7 |
| npm | @dirigible-ai/sdk | 0.6.2, 0.6.3 |
| npm | @squawk/fix-data | 0.6.4, 0.6.5, 0.6.6, 0.6.7, 0.6.8 |
| npm | @uipath/cli | 1.0.1 |
| npm | @uipath/tool-workflowcompiler | 0.0.12 |
| npm | @draftlab/auth-router | 0.5.1, 0.5.2 |
| npm | @tanstack/router-utils | 1.161.11, 1.161.14 |
| npm | @draftlab/auth | 0.24.1, 0.24.2 |
| npm | @tanstack/react-start | 1.167.68, 1.167.71 |
| npm | @uipath/docsai-tool | 1.0.1 |
| npm | @supersurkhet/sdk | 0.0.2, 0.0.3, 0.0.4, 0.0.5, 0.0.6, 0.0.7 |
| npm | @uipath/orchestrator-tool | 1.0.1 |
| npm | @squawk/types | 0.8.1, 0.8.2, 0.8.3, 0.8.4, 0.8.5 |
| npm | @tanstack/router-devtools | 1.166.16, 1.166.19 |
| npm | @tallyui/connector-woocommerce | 1.0.1, 1.0.2, 1.0.3 |
| npm | @squawk/mcp | 0.9.1, 0.9.2, 0.9.3, 0.9.4, 0.9.5 |
| npm | @squawk/procedure-data | 0.7.3, 0.7.4, 0.7.5, 0.7.6, 0.7.7 |
| npm | @uipath/packager-tool-functions | 0.1.1 |
| npm | @tanstack/vue-router | 1.169.5, 1.169.8 |
| npm | @opensearch-project/opensearch | 3.5.3, 3.6.2, 3.7.0, 3.8.0 |
| npm | @squawk/notams | 0.3.6, 0.3.7, 0.3.8, 0.3.9, 0.3.10 |
| npm | @tanstack/react-router-ssr-query | 1.166.15, 1.166.18 |
| npm | @uipath/aops-policy-tool | 0.3.1 |
| npm | @uipath/traces-tool | 1.0.1 |
| npm | @uipath/access-policy-tool | 0.3.1 |
| npm | @tanstack/history | 1.161.9, 1.161.12 |
| npm | @tanstack/router-cli | 1.166.46, 1.166.49 |
| npm | @tanstack/react-router | 1.169.5, 1.169.8 |
| npm | @tanstack/start-server-core | 1.167.33, 1.167.36 |
| npm | agentwork-cli | 0.1.4, 0.1.5 |
| npm | @draftauth/core | 0.13.1, 0.13.2 |
| npm | @tolka/cli | 1.0.2, 1.0.3, 1.0.4, 1.0.5, 1.0.6 |
| npm | @uipath/functions-tool | 1.0.1 |
| npm | @squawk/weather | 0.5.6, 0.5.7, 0.5.8, 0.5.9, 0.5.10 |
| npm | @squawk/flightplan | 0.5.2, 0.5.3, 0.5.4, 0.5.5, 0.5.6 |
| npm | @squawk/geo | 0.4.4, 0.4.5, 0.4.6, 0.4.7, 0.4.8 |
| npm | @tallyui/connector-shopify | 1.0.1, 1.0.2, 1.0.3 |
| npm | @mistralai/mistralai | 2.2.2, 2.2.3, 2.2.4 |
| npm | @uipath/maestro-sdk | 1.0.1 |
| npm | @mistralai/mistralai-gcp | 1.7.1, 1.7.2, 1.7.3 |
| npm | @squawk/flight-math | 0.5.4, 0.5.5, 0.5.6, 0.5.7, 0.5.8 |
| npm | @uipath/agent-tool | 1.0.1 |
| npm | @tanstack/start-fn-stubs | 1.161.9, 1.161.12 |
| npm | ml-toolkit-ts | 1.0.4, 1.0.5 |
| npm | @uipath/admin-tool | 0.1.1 |
| npm | @uipath/agent-sdk | 1.0.2 |
| npm | @uipath/resourcecatalog-tool | 0.1.1 |
| npm | @tanstack/solid-start-server | 1.166.54, 1.166.57 |
| npm | @uipath/solutionpackager-tool-core | 0.0.34 |

