December 2025 closed out the year with a clear message for defenders: quickly-evolving threats are challenging traditional defense strategies. Attackers are refining both their tooling and their tactics, from professionalized shared services models and AI’s influence on the development and deployment of malware, to critical vulnerabilities in widely used web frameworks and the continued evolution of ransomware-as-a-service. At the same time, coordinated law enforcement efforts showed that disruption at scale is possible, but only with sustained global cooperation and attention.
The December Monthly Cyber Threat Intelligence Report from Cynet’s CyOps Team captures this tension well. The report summarizes the most important developments in the cyber threat landscape and what they mean for organizations in the year ahead.
Ransomware Remains Relentless and Operationally Disruptive
Ransomware once again dominated the threat landscape in December, with 802 publicly reported victims worldwide. Manufacturing continued to bear the brunt of attacks, following a familiar pattern: attackers favor environments where downtime translates directly into financial and safety consequences. The United States remained the most frequently targeted country, reflecting both its large digital footprint and the perceived willingness of organizations to pay to restore operations quickly.
Several incidents from December illustrate how ransomware has moved beyond isolated IT outages into full-scale operational disruption:
- Romania’s National Waters Administration suffered a ransomware incident that impacted roughly 1,000 systems, including GIS servers and databases critical to national water management.
- Petróleos de Venezuela (PDVSA) experienced an attack that disrupted export operations and delayed oil cargo deliveries, demonstrating how ransomware can ripple through global supply chains.
- A large-scale social engineering campaign dubbed “ConsentFix” emerged, abusing Azure CLI access and fake CAPTCHA prompts to hijack Microsoft accounts. While not traditional ransomware, the campaign highlights how initial access vectors are becoming more subtle and cloud-native.
The takeaway is clear: ransomware is no longer just an endpoint problem. It is an enterprise-wide risk that spans identity, cloud tooling, and operational technology.
Custom Malware Is Becoming the Norm, Not the Exception
December also reinforced the trend of threat actors investing in bespoke malware, often built in modern languages designed to evade traditional defenses.
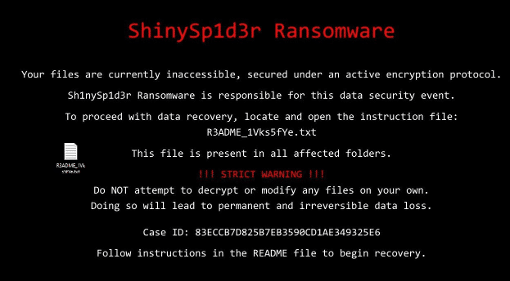
One of the most notable developments was ShinySp1d3r, a new Go-based ransomware-as-a-service platform attributed to the SLH group (Scattered Lapsus$ Hunters). The tooling blends techniques associated with ShinyHunters, Scattered Spider, and LAPSUS$, resulting in a platform with advanced anti-analysis features and effective lateral movement capabilities. This convergence of tactics suggests collaboration (or at least cross-pollination) between some of the most disruptive groups of the past few years.
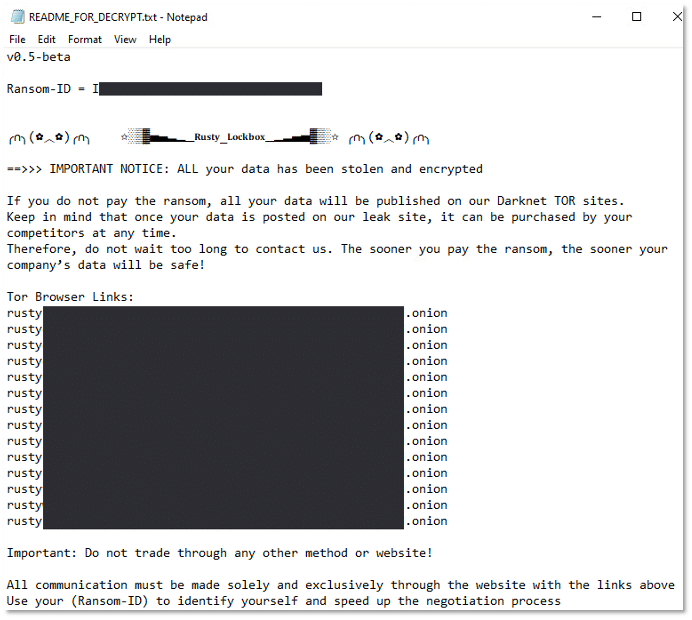
Another emerging threat, Rusty Lockbox, reflects the continued shift toward Rust-based malware. It employs a double-extortion model, exfiltrating sensitive data before encryption and deliberately deleting local backups to eliminate recovery options. This approach increases pressure on victims and shortens the decision window during incident response.
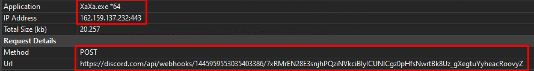
Meanwhile, XaXa Stealer highlights how even “supporting” malware is becoming more specialized. By targeting browser credentials and Discord authentication tokens and exfiltrating data via Discord webhooks, it blends into legitimate traffic patterns and complicates detection.
React2Shell: A Reminder That Supply Chain Risk Is Still Front and Center
The most severe technical issue identified in December was React2Shell (CVE-2025-55182), a pre-authentication remote code execution vulnerability affecting React Server Components. With a CVSS score of 10.0, this flaw represents worst-case risk: unauthenticated attackers can achieve full server-side code execution.
The vulnerability stems from unsafe deserialization in the React Flight protocol, allowing crafted requests to trigger arbitrary code execution. Affected versions include React 19.0 through 19.2.0, and exploitation requires no prior access, making internet-facing applications especially vulnerable.
For organizations relying on modern JavaScript frameworks, React2Shell underscores an uncomfortable reality: application-layer vulnerabilities can now carry the same impact as traditional infrastructure exploits. Immediate patching to React 19.0.1, 19.1.2, or 19.2.1 is critical.
A Rare Bright Spot: Operation Sentinel
Amid the steady stream of bad news, December also delivered a meaningful win for defenders. Operation Sentinel, a coordinated effort involving Interpol and law enforcement agencies across 19 African countries, demonstrated what sustained collaboration can achieve.
Over the course of one month, the operation resulted in:
- More than 6,000 malicious links taken down
- Over $21 million in prevented financial losses, including a halted $7.9 million fraudulent wire transfer in Senegal
While such operations do not eliminate cybercrime, they raise costs for attackers and disrupt the infrastructure that many campaigns rely on.
What This Means for Security Teams Going Into 2026
December’s activity reinforces several hard truths. Attackers are moving faster, building their own tools, and exploiting high-impact vulnerabilities as soon as they appear. At the same time, initial access increasingly hinges on identity abuse, cloud tooling, and trusted frameworks rather than brute-force intrusion.
For defenders, this means prioritizing:
- Rapid patch management, especially for application and framework vulnerabilities
- Proactive threat monitoring across identity, endpoint, and cloud environments
- Preparedness for double-extortion and operational disruption, not just data loss
While prevention is always the first goal, how quickly organizations can detect, contain, and recover when trust is abused is equally important in 2026.
How Cynet Helps Security Teams Stay Ahead
Cynet’s unified cybersecurity platform is designed to detect and prevent emerging threats across the full attack lifecycle. By combining endpoint protection, network visibility, behavioral detection, and automated response, Cynet enables security teams to prevent emerging threats, respond to incidents instantly, and operate with confidence, even as the threat landscape evolves.
FAQ
What is React2Shell? React2Shell (CVE-2025-55182) is a critical pre-authentication remote code execution (RCE) vulnerability affecting React Server Components (RSC) in React versions 19.0 through 19.2.0. The flaw stems from unsafe server-side deserialization in the React Flight protocol, allowing attackers to craft malicious requests that abuse JavaScript prototype chaining to execute arbitrary code on the server. React2Shell has been actively exploited in the wild, with observed activity linked to advanced threat actor infrastructure, making it one of the most severe web application vulnerabilities of 2025. Immediate patching and version upgrades are required to mitigate risk.
What is Rusty Lockbox? Rusty Lockbox (also known as Rusty Locker) is a Rust-based double-extortion ransomware that combines aggressive encryption with pre-encryption data theft to pressure victims into paying ransom demands. The malware incorporates extensive anti-analysis and sandbox evasion techniques, deletes local backups to prevent recovery, and terminates services and applications that may interfere with file encryption. Rusty Lockbox demonstrates how modern ransomware increasingly prioritizes stealth, resilience, and operational reliability, while leveraging Rust for performance and cross-platform potential.
What is ShinySp1d3r? ShinySp1d3r is an emerging ransomware-as-a-service (RaaS) strain developed by the Scattered Lapsus$ Hunters (SLH) collective, a group formed from the convergence of ShinyHunters, Scattered Spider, and LAPSUS$. Unlike earlier campaigns that relied on outsourced encryptors, ShinySp1d3r is built in-house and introduces advanced capabilities including anti-analysis techniques, lateral movement, shadow copy deletion, process termination, and ChaCha20-based encryption. The ransomware is designed to maximize impact, evade detection, and inhibit recovery, signaling a shift toward more industrialized and technically mature ransomware operations.
What is XaXa Stealer? XaXa Stealer is a sophisticated information-stealing malware designed to harvest sensitive data from a wide range of web browsers, including stored credentials, cookies, browsing history, and credit card information. In addition to browser data, XaXa Stealer targets Discord authentication tokens and exfiltrates stolen information using Discord webhooks over HTTPS, helping it blend in with legitimate traffic. The malware employs debugger detection, delayed execution, and cleanup routines to evade sandbox analysis and hinder forensic investigation, making it a persistent threat in credential theft and account takeover campaigns.
What is Cyops? CyOps is the 24×7 human engine behind Cynet’s unified, AI-powered cybersecurity platform. Acting as an always-on extension of your team, CyOps threat analysts and MDR experts monitor, investigate, and respond to threats in real-time.