Executive Summary
Identity-based attacks have become a primary entry point for modern breaches. In Microsoft 365 and Entra ID environments, threat actors increasingly rely on legitimate cloud functionality to establish persistence, reduce visibility, and operate without the attendant noise typically associated with endpoint malware. One of the most pervasive and effective examples of this tradecraft is inbox rule abuse.
Cynet Research and CyOps teams continuously monitor and investigate real-world identity-driven attacks across environments, with a strong focus on post-authentication abuse techniques.
While inbox rules are designed to improve productivity, Cynet investigations show that they are repeatedly abused following account compromise. After gaining access often via token theft, session hijacking, or AiTM phishing, threat actors establish control by creating rules that silently hide, redirect, or exfiltrate sensitive communications. This allows for long-term, low-noise access to business-critical data while remaining below the radar of traditional security controls.
This technique is uniquely effective because it:
- Operates entirely within trusted platform functionality, bypassing most signature-based detections.
- Requires no malware or endpoint footprint, making it invisible to standard EDR solutions.
- Generates minimal security telemetry, often blending in with legitimate user activity.
- Enables persistent control without the need for continuous threat actor presence or repeated logins.
In multiple investigations, including real-world Entra ID session-hijacking attacks, Cynet Research and CyOps teams have identified a consistent attack lifecycle:
Initial Access -> Token Abuse -> Inbox Rule Creation -> Persistent Communication Subversion.
See our previous report: Token to Takeover: Inside a Real-World Microsoft Entra ID ITDR Investigation
Cynet teams actively hunt for these patterns by analyzing identity and SaaS activity to detect subtle behavioral anomalies that indicate abuse. By continuously tracking evolving techniques and adapting detection logic, we maintain visibility into attacks that traditional security solutions often miss.
These stealthy, identity-based threats are identified, investigated, and remediated before they escalate into full-scale breaches.
Why Inbox Rules Matter: The Silent Persistence Mechanism
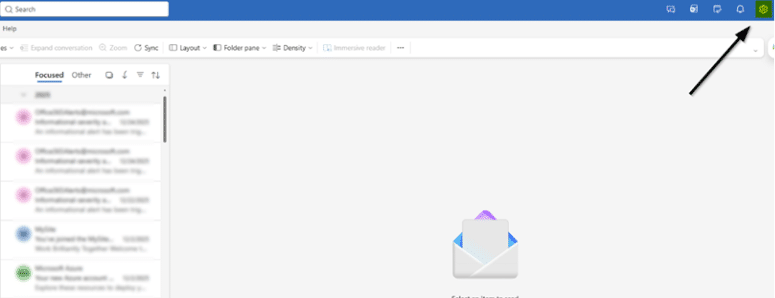
Inbox rules are a mailbox-native automation feature in Outlook and Exchange Online. They are intended to help users move, prioritize, or delete messages based on specific criteria.
In normal use, inbox rules improve productivity. In malicious use, they become a high-impact control mechanism. A malicious inbox rule does not need to exploit a vulnerability or launch a process on an endpoint. It simply instructs the mail server on how to handle incoming data. Once a rule is created, it can continuously manipulate the victim’s mailbox environment, determining what gets forwarded externally and which communications disappear from view. This creates a state of “passive persistence,” where the attacker receives a stream of sensitive data without having to maintain an active session.
Mechanics of Abuse in Microsoft 365
To understand how threat actors abuse inbox rules, it is essential to examine their logic model: Conditions (filters) determine when a rule is triggered, and Actions define the subsequent automated response.
Key components and actions frequently utilized in attack scenarios include:
- MoveToFolder
- Moves emails to a specific folder.
- Abuse: Hiding messages in rarely used folders (e.g., RSS Feeds).
- MarkAsRead
- Marks emails as read upon arrival.
- Abuse: Preventing users from noticing new or important messages.
- StopProcessingRules
- Stops additional rules from being applied.
- Abuse: Ensuring malicious rules take priority and override legitimate ones.
- ForwardTo / RedirectTo
- Sends emails to another recipient.
- Abuse: Silent data exfiltration to threat actor-controlled accounts.
- DeleteMessage
- Deletes emails automatically.
- Abuse: Removing visibility of targeted communications.
Figure 1 illustrates how a new rule is created in Microsoft Outlook.
Fig. 1
The Evolution of Inbox Rule Abuse
Inbox rule abuse is not a static technique; it has evolved in direct parallel with the migration to cloud-native email platforms. Over the last decade, threat actors have meticulously refined their methods to prioritize stealth, persistence, and the bypass of modern defensive layers.
2013: Initial Abuse
Early BEC campaigns targeting Office 365 began using simple email forwarding rules.
Threat actors passively collected sensitive communications, primarily to gain visibility into workflows. Detection was relatively straightforward, as activity was limited to basic forwarding behavior.
2017: Evasion and Persistence
Threat actors expanded beyond simple forwarding. Inbox rules were used to hide security alerts, filter sensitive messages, and prevent visibility. At the same time, more advanced techniques emerged, including the ability to create hidden or hard-to-detect rules via MAPI. This marked a shift toward stealth and long-term persistence, making detection significantly more challenging.
2021: Identity-Driven Attacks
As organizations moved to cloud and identity-first environments, tradecraft evolved accordingly.
Inbox rule abuse became part of broader identity attacks, combined with:
- Token theft and session hijacking
- OAuth application abuse
- API-based access (e.g., Microsoft Graph)
Threat actors no longer relied on user interaction. Rules could be created and modified programmatically, significantly reducing visibility and bypassing traditional controls.
Present: Integrated Attack Chains
Inbox rule abuse is now a standard stage in modern attack flows.
In campaigns involving AiTM phishing and token theft, threat actors establish access and immediately manipulate inbox rules to:
- Hide activity
- Maintain persistence
- Control communication
This is no longer a standalone technique, but part of a coordinated, multi-step attack chain designed to evade detection and enable fraud.
Threat Landscape: Threat Actors and Campaigns Associated with Inbox Rule Abuse
Inbox rule abuse is not limited to a single campaign or actor type. Public reporting and incident response patterns show that it manifests across several threat models.
- Financially motivated adversaries have long exploited mailbox access to intercept communications related to wire transfers, invoices, payroll, and banking modifications. Groups such as FIN7, FIN11, TA505, and more recently Storm-2755, exemplify how this technique plays a pivotal role in Business Email Compromise (BEC) and fraudulent campaigns. These actors leverage mailbox access to monitor financial transactions, selectively exfiltrate data, and manipulate ongoing threads. Specifically, inbox rules are deployed to filter, forward, or conceal emails related to payments, allowing threat actors to maintain persistence over sensitive workflows without alerting the user.
- In parallel, identity-focused threat actors such as Scattered Spider highlight a more advanced evolution of this technique. These groups specialize in SaaS and identity abuse, where access to a cloud account is quickly followed by actions that establish control and persistence. Within this context, mailbox manipulation – including inbox rule abuse – becomes a natural extension of post-compromise activity, enabling threat actors to control communication channels and operate under a trusted identity.
- Additionally, token-based attack campaigns, such as those observed in Storm-0558-style activity, demonstrate how unauthorized access to cloud mailboxes can be achieved without traditional credential compromise. Once access is established via stolen or forged tokens, threat actors can leverage mailbox-level actions, including inbox rule creation, to silently monitor communications and maintain long-term persistence while avoiding typical authentication-based detections.
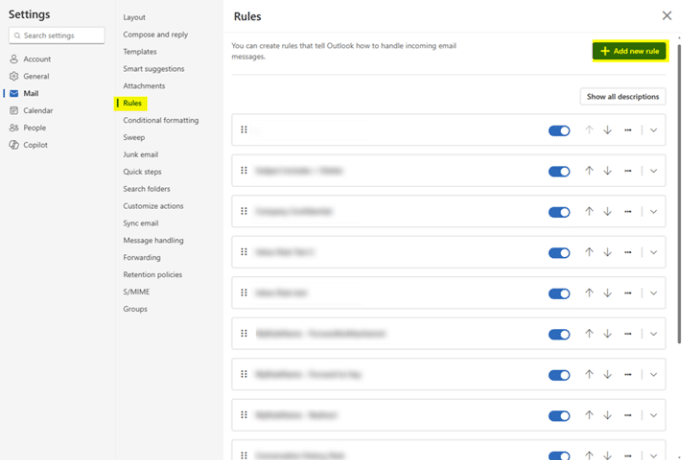
Common Attack Patterns and Investigation Signals
Inbox rule abuse follows repeatable patterns that can be identified through audit telemetry, mailbox activity, and identity logs when these signals are correlated.
Rule Creation as a Primary Signal
One of the most relevant indicators is the creation or modification of inbox rules monitored through events such as:
- New-InboxRule
- Set-InboxRule
These events manifest when rules are established through Outlook Web Access (OWA), PowerShell, or programmatic API-based access such as Microsoft Graph. In identity-driven incidents, rule creation typically occurs in close temporal proximity to initial access.
Evasion Through Naming
Threat actors often select rule names that avoid attention. Examples include minimal values such as “.”, “…”, or short random strings. In other cases, the name is made to look routine, such as “Archive” or “Forward All”. The naming itself is not conclusive. In context, it becomes meaningful.
Automated Data Exfiltration
Rather than forwarding all emails, threat actors often filter finance or security-related keywords. Examples include:
- ForwardTo or RedirectTo external threat actor-controlled accounts
- Keyword-based filtering, such as:
- invoice
- payment
- password
This enables threat actors to selectively capture high-value communications in real time.
Full Control of Visibility:
One of the most impactful patterns is not forwarding but suppression. Threat actors move emails to rarely used folders, mark them as read, or delete them entirely. This lets them maintain visibility while keeping the legitimate user unaware.
Cross-signal correlation is the real detection point
Any single event may look benign. A new mailbox rule alone is not necessarily malicious. An anomalous login alone may not be enough. The real signal emerges when the events appear together in the right sequence.
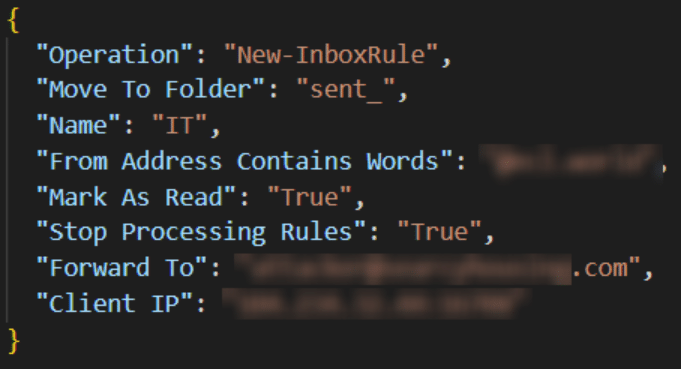
Figure 2 shows the creation of a suspicious inbox rule.
Fig. 2
Cynet Handles Real-World Attacks
Cynet teams have handled multiple incident response cases in Microsoft Entra ID environments, investigating identity-driven attacks to understand how threat actors gain access, establish persistence, and operate undetected.
The following example reflects a real-world investigation flow based on those cases.
Phase 1: Initial Access Through Phishing
- Initial Access (TA0001)
- Phishing: Spearphishing Link (T1566.002)
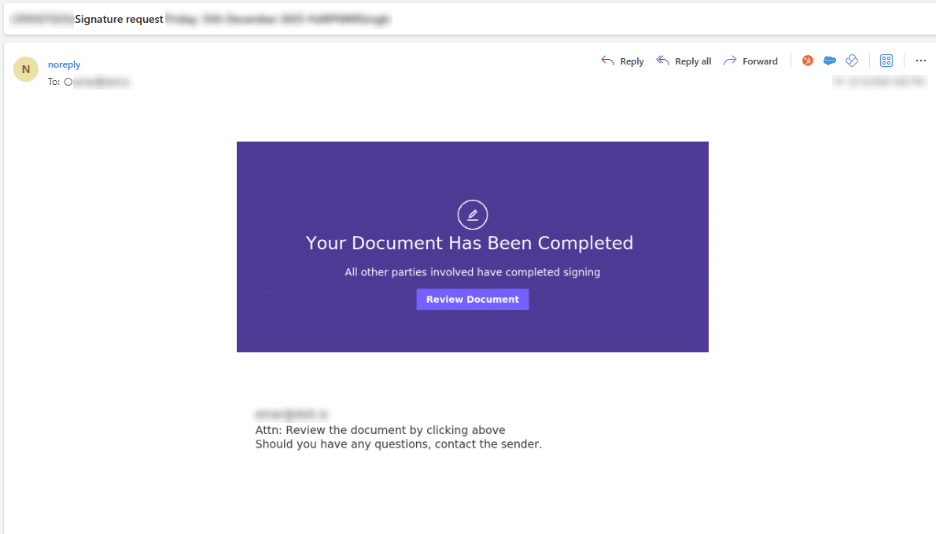
The attack began with a phishing email sent to the victim. The message appeared legitimate, requesting the recipient to review and sign a document. Clicking the link redirected the user to a malicious site, where credentials or session data were likely compromised.
Figure 3 shows the malicious email that was sent to the victim.
Fig. 3
Phase 2: Token-Based Persistence and Evasion
- Persistence/Privilege Escalation/Defense Evasion/Lateral Movement (TA0003, TA0004, TA0005, TA0008)
- Use Alternate Authentication Material: Application Access Token (T1550.001)
- Account Manipulation (T1098)
Within hours, an anomalous login was observed. The authentication originated from a previously unseen geographic location and leveraged what appeared to be a stolen session token, allowing the threat actor to bypass standard authentication controls without raising immediate suspicion.
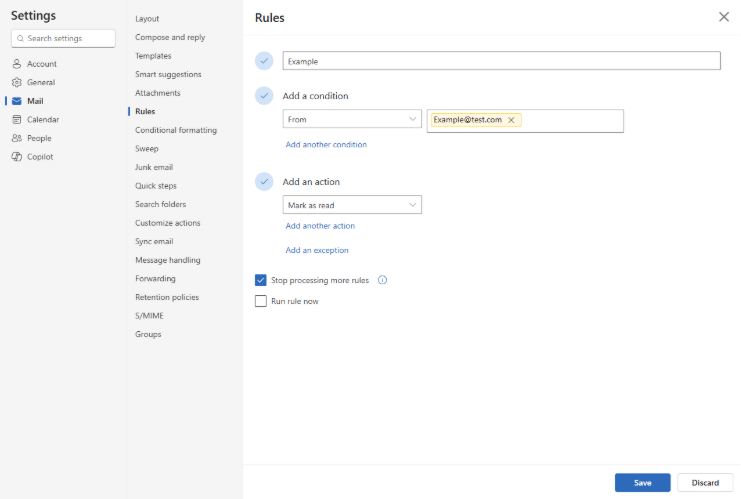
Phase 3: Post-Authentication Mailbox Control
- Defense Evasion /Collection (TA0005, TA0009)
- Email Collection: Email Forwarding Rule (T1114.003)
- Hide Artifacts (T1564)
Minutes after gaining access, the threat actor moved quickly to establish control.
A new inbox rule was created shortly after the login event. The rule specifically targeted emails from the organization’s finance department, indicating intent aligned with BEC activity.
The rule included multiple actions:
- Isolation: Move emails to “RSS Feeds” folder
- Obfuscation: Mark all matched emails as read
This ensured that critical financial communications were removed from the user’s primary view. Even if accessed, the messages appeared already processed, significantly reducing the likelihood of detection.
From this point forward, the threat actor no longer needed to actively interact with the mailbox.
Phase 4: Passive Persistence
This configuration enables a form of passive persistence. The inbox rule continuously processes incoming emails, allowing the threat actor to:
- Monitor sensitive communications
- Intercept critical business workflows
- Maintain long-term access without repeated logins
As a result, the threat actor remained embedded within the account for an extended period, collecting information without generating noticeable indicators for the end user.
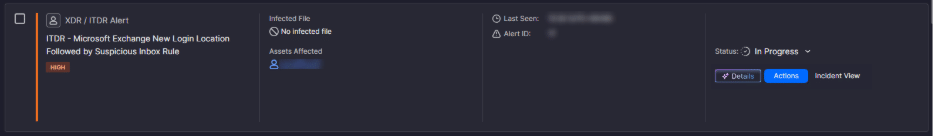
Closing the Visibility Gap with Cynet ITDR
Had Cynet been deployed at the time, this activity would have been surfaced earlier in the attack chain.
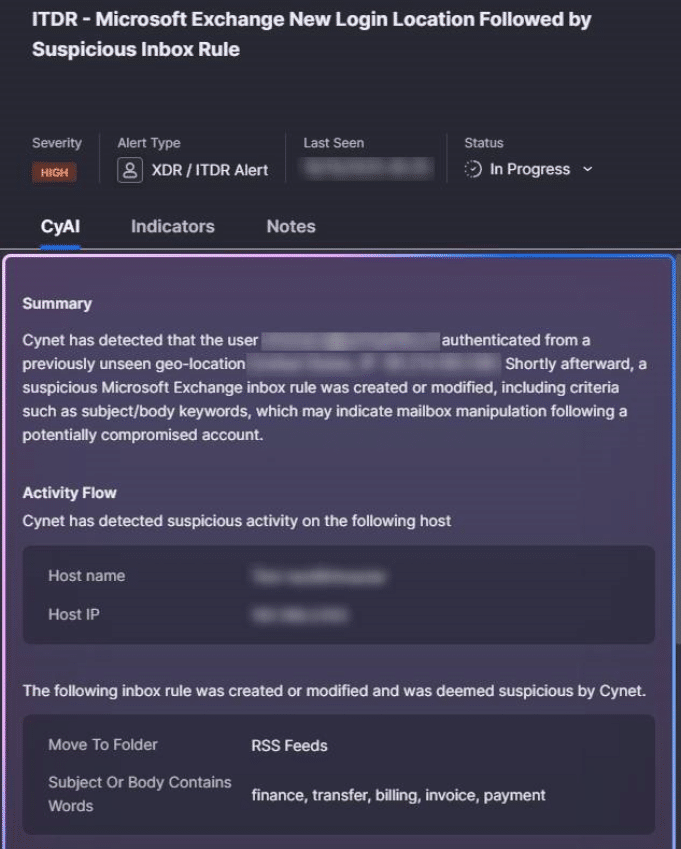
Specifically, the combination of an anomalous login event, including access from an unfamiliar geographic location and the use of a suspicious session token – followed closely by the creation of an inbox rule- represents a high-confidence behavioral pattern.
This is exactly where Cynet’s unified platform, with native ITDR capabilities, delivers critical value. Cynet’s ITDR engine correlates identity-based anomalies directly with post-compromise actions, enabling the detection of sophisticated attack patterns that traditional, siloed solutions often overlook.
AI-Enriched Investigation: As shown in the Cynet console (Figure 4), the alert is enriched with AI-driven analysis, providing security teams with the full context of the attack flow—from the stolen token to the specific logic of the malicious rule.
By unifying identity and SaaS telemetry, Cynet enables organizations to intercept these stealthy threats before they escalate from a compromised account into a full-scale breach.
Fig. 4
The Business Impact of Inbox Rule Abuse
The technical aspects of inbox abuse is important, but it’s the business impact that makes it particularly dangerous.
Scenario 1: Compromising a CTO
A CTO’s account is compromised. The threat actor creates a rule that hides key communications and marks them as read. From that moment, the CTO is effectively blind.
Requests sent from the account are trusted and executed. Responses are intercepted. Decisions are made based on manipulated information. The organization operates under false assumptions, without knowing it.
Scenario 2: Compromising an administrative assistant
An administrative assistant’s mailbox is compromised. A rule silently forwards sensitive emails while hiding the originals. The threat actor gains continuous visibility into financial workflows and internal operations. Over time, this leads to action. Payment requests are initiated. Details are modified. Fraud is executed. No disruption. No clear alerts. Just normal communication.
Financial processes are controlled from within, without detection.
MITRE ATT&CK Mapping
Inbox rule abuse and related identity-based techniques align with several MITRE ATT&CK tactics and techniques:
- T1114.003: Email Collection: Email Forwarding Rule
- T1098: Account Manipulation
- T1078: Valid Accounts
- T1550.001: Application Access Token
- T1564: Hide Artifacts
Conclusion
Inbox rule abuse highlights a fundamental shift in modern attacks. Threat actors no longer need to break systems. They exploit them from within, using legitimate functionality to gain persistence, stealth, and control.
These attacks are difficult to detect because they do not rely on traditional indicators. Visibility is fragmented, and signals are weak. This is exactly the gap Cynet is designed to close.
Cynet’s unified platform, with native ITDR capabilities, provides unified visibility across identity, endpoint, network, and SaaS activity, allowing security teams to detect subtle behaviors like inbox rule abuse as part of a complete view into an attack path.
Combined with continuous monitoring and investigation by Cynet Research and CyOps teams, organizations are able to identify, understand, and stop these threats early, before they translate into real business impact.

