This blog is part of an ongoing series examining the findings in the February 2026 Cyber Threat Intel Report from Cyops. Read the full report here.
February 2026 delivered 701 confirmed ransomware victims (according to officially announced data, which likely greatly underrepresent the total damage), with the United States as the most targeted country and the technology sector taking the hardest hits. The top group by victim count, Qilin, claimed 113 victims alone. These numbers are not a background statistic. They represent active, ongoing campaigns that are targeting organizations like yours right now.
Here is what the threat intelligence from this month tells us, and what it demands from defenders.
Ransomware Groups that Dominated February
The top 10 groups by victim count last month:
| Group | Victims |
| Qilin | 113 |
| TheGentlemen | 83 |
| Clop | 79 |
| Akira | 47 |
| IncRansom | 39 |
| DragonForce | 34 |
| Play | 32 |
| NightSpire | 30 |
| LockBit5 | 29 |
| Vect | 20 |
Clop‘s continued high volume is consistent with its known pattern of mass-exploitation campaigns targeting file transfer and enterprise software vulnerabilities. Qilin and Akira remain operationally aggressive across multiple sectors.
Two New Ransomware Operations Worth Tracking
Green Blood Group
Green Blood Group is an emerging double-extortion operation first observed in early 2026. Written in Go (Golang) and compiled as a Windows x64 executable, the ransomware is technically mature, not an amateur operation.
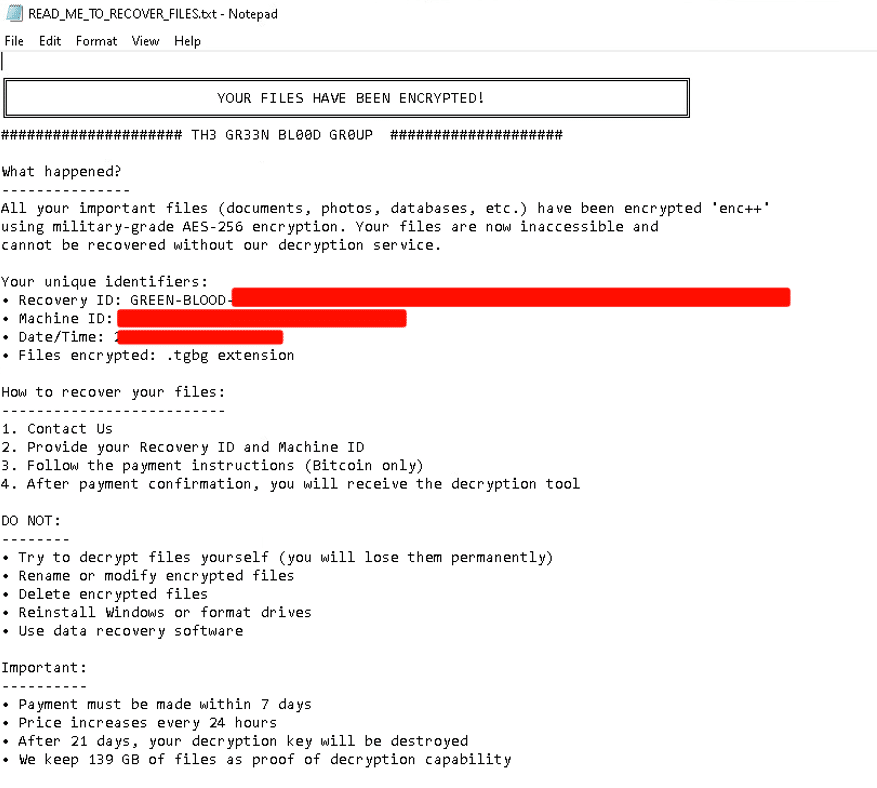
Key behavioral characteristics identified through analysis:
- Privilege validation at runtime: The binary checks for local Administrator group membership before proceeding. If running with admin rights, it executes a full recovery-inhibition routine — deleting Volume Shadow Copies, removing Windows Backup catalogs, disabling the Windows Recovery Environment, and turning off the Windows Firewall.
- AES-256 encryption: Files are encrypted and renamed with the .tgbg extension. Ransom notes are dynamically generated with unique Recovery IDs per victim.
- Bitcoin-only payment: With a 7-day deadline, escalating price, and a 21-day key destruction threat.
- Self-cleanup: A batch script (cleanup_greenblood.bat) is generated and executed post-encryption to delete the ransomware binary and minimize forensic artifacts.
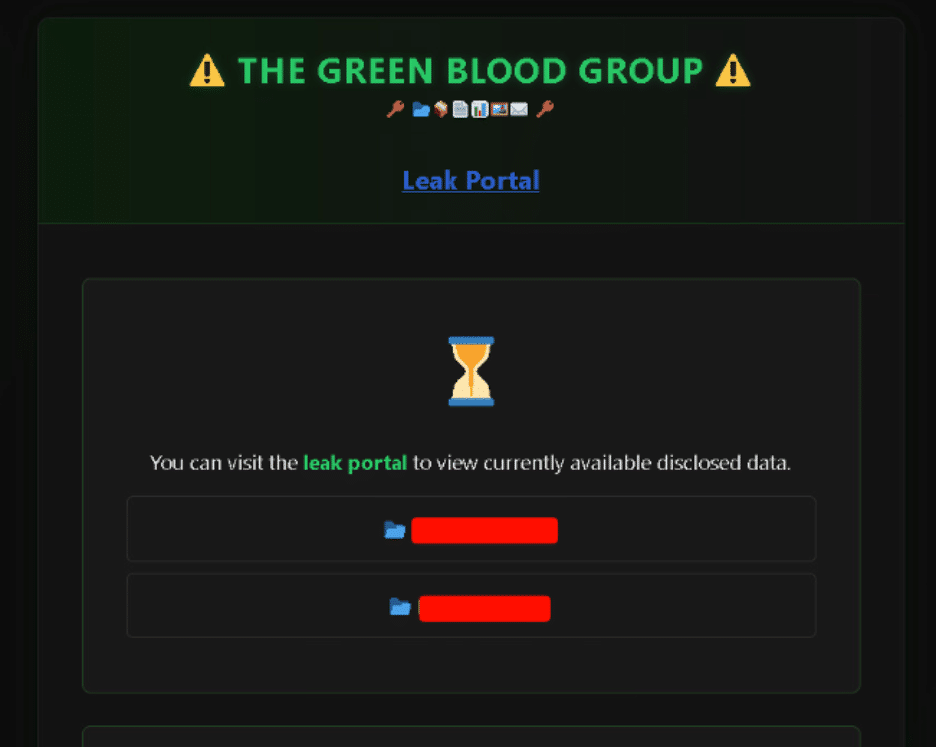
- Tor-based leak portal: Victims are publicly listed with structured data including compromised domains, data size, and categorized datasets.
One notable weakness: the attempt to disable Microsoft Defender real-time monitoring via registry modification contained a syntax error and failed to execute successfully. That said, the group’s operational maturity in all other areas suggests this will be corrected in future versions.
0APT Ransomware
0APT emerged in late January 2026 promoting a Ransomware-as-a-Service model with a rapid flood of victim claims. While researchers have flagged credibility concerns — the volume of claims appeared artificially inflated and several named organizations showed no evidence of compromise — the group does possess functional ransomware.
The analyzed sample is a Rust-based 64-bit Windows executable that performs recursive filesystem traversal, appends the .0apt extension to encrypted files, drops a ransom note named README0apt.txt, and modifies the desktop wallpaper. The binary claims AES-256 and RSA-2048 hybrid encryption, enforces a 24-hour payment deadline, and includes aggressive data leak threats.
Critically, the binary does not elevate privileges and does not perform lateral movement or establish C2 communication — limiting its impact compared to more capable groups. The negotiation portal was also found to be offline during analysis.
The key lesson from 0APT is not technical — it is strategic. Extortion pressure does not require a confirmed breach. The mere credible threat of a public data leak can trigger premature ransom payments. Your incident response plan must include explicit guidance on validating breach claims through internal telemetry before any external response decision is made.
The RAMP Forum Seizure: A Win, But Not the End
The FBI’s seizure of the RAMP forum (one of the most prominent ransomware-associated underground platforms) is a meaningful law enforcement success. RAMP operated as an open marketplace for ransomware promotion and affiliate recruitment, hosting groups including LockBit, ALPHV, Conti, DragonForce, Qilin, and RansomHub over its lifespan.

The forum operator, using the alias Stallman, publicly confirmed the takedown, describing it as having destroyed years of work.
Despite the short-term win, ransomware ecosystems are resilient. Early indicators already show groups like DragonForce migrating toward alternative platforms such as ReHub. Fragmentation, not dissolution, is the expected outcome. Expect a period of repositioning, followed by reconsolidation on successor platforms.
This seizure is a disruption, not a structural end to ransomware operations.
What Defenders Need to Act On Today
Immediately:
- Patch the CVEs covered in this month’s report — particularly CVE-2026-22769 (Dell RecoverPoint, CVSS 10.0), CVE-2026-21643 (FortiClientEMS SQL injection, CVSS 9.8), and CVE-2026-1731 (BeyondTrust RCE, CVSSv4 9.9). Pre-authentication vulnerabilities in internet-facing systems must be treated as critical-priority patches with no delay tolerance.
- Audit Volume Shadow Copy and backup catalog protections. Ensure VSS deletion attempts are alerted on in your SIEM.
- Confirm that bcdedit, wbadmin, and vssadmin executions by non-administrative processes generate high-priority alerts.
Operationally:
- Review your ransomware response playbook. Does it include a step to validate breach claims before engaging with threat actors? If not, add one.
- Ensure offline, immutable backups are tested and restorable. Green Blood Group’s recovery inhibition routine is designed specifically to make in-place recovery impossible.
- Integrate Go-compiled binary detection heuristics into your EDR ruleset. Both Green Blood Group and Morbius Stealer are Golang-based — a growing trend among threat actors exploiting Go’s cross-platform compilation and limited AV signature coverage.
Ransomware actors are technically proficient, operationally aggressive, and adapting faster than most organizations are patching. The window between vulnerability disclosure and active exploitation continues to narrow. Treat every critical CVE as if it is already being actively exploited, because statistically, it likely will be soon. For more in-depth analysis of the latest threat actor activity, download the February 2026 Cyber Threat Intelligence Report.