Below we’ll demonstrate how Cynet detects and prevents Hazard ransomware. For more, you can review our experts’ static analysis and dynamic analysis of this threat.
Note that during the execution simulation, Cynet 360 AutoXDR is configured in detection mode (without prevention) to allow the Hazard ransomware to execute its full flow. This lets Cynet detect and log each step of the attack.
Cynet can detect and prevent this malware using multiple mechanisms.
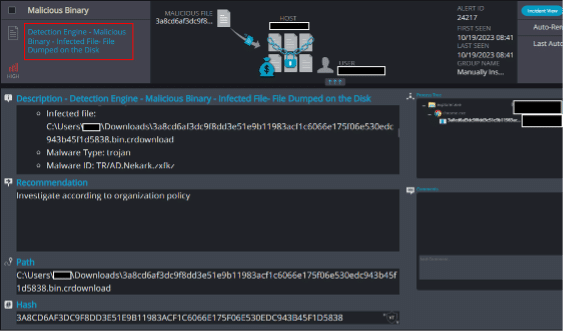
File Dumped on the Disk
Cynet’s AV/AI engine detects that a malicious file is dumped on the disk or is attempting to run:
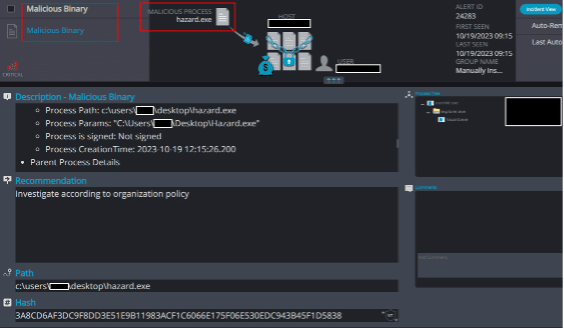
Malicious Binary
By inspecting the file’s SSDEEP hash value, Cynet is able to detect the file’s malevolence:
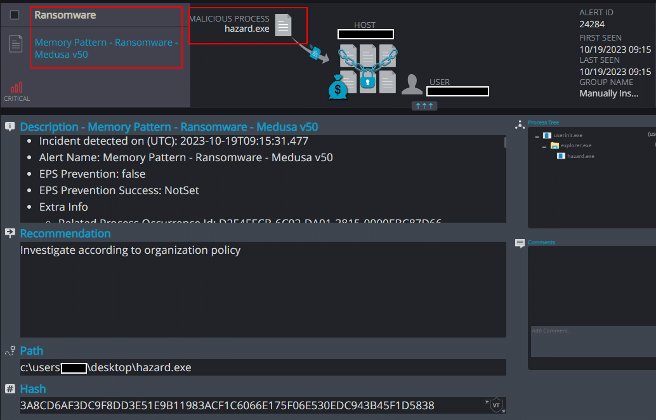
Memory Pattern – Ransomware – Medusa v50
Cynet detects malicious strings running in the process’ memory that matches known “MedusaLocker” activity:
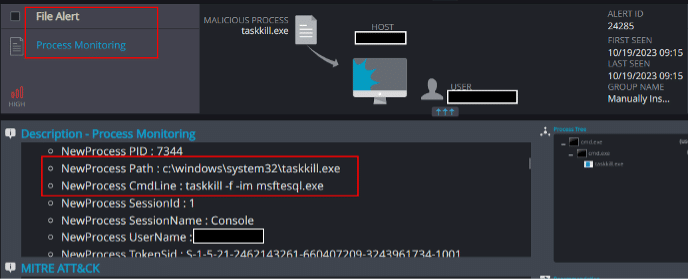
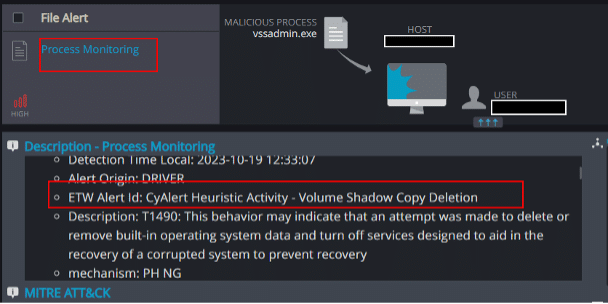
Process Monitoring
The process monitoring detection mechanism is able to detect the process’s attempts to terminate the database services, as well as the attempt to delete the host’s shadow copies:
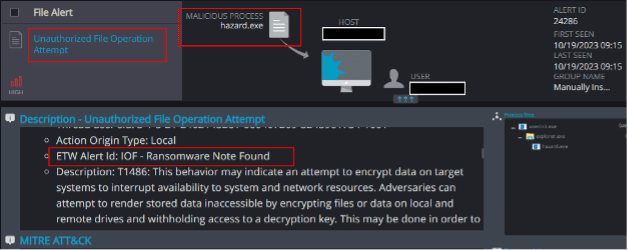
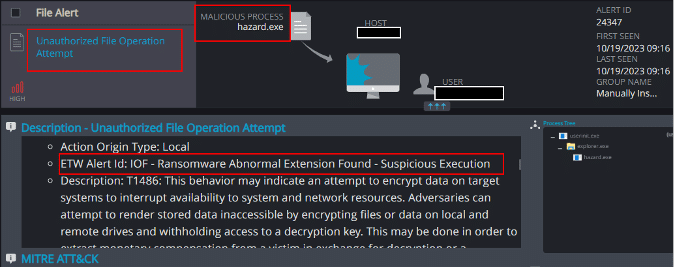
Unauthorized File Operation Attempt
This mechanism is able to detect and report on attempts to modify Cynet’s Ransomware decoy files, the presence of files with suspicious extensions, and the creation of a ransom note on the host:
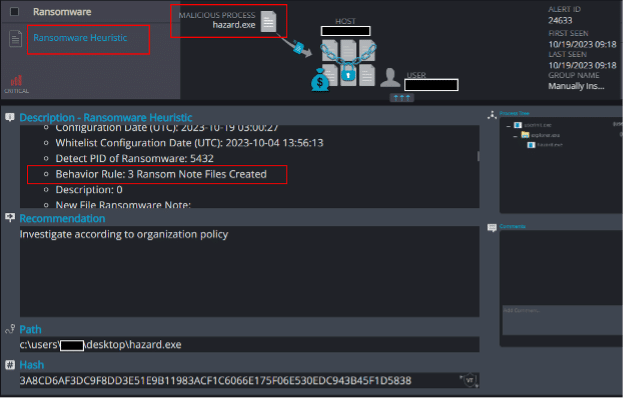
Ransomware Heuristic
An additional detection mechanism is able to detect the creation of ransom notes on the host: