This is part of our ongoing blog series breaking down the use cases in the 2025 2H CyOps ECHO report. Download the complete report here.
When most people think about cyberattacks, they imagine shadowy figures exploiting obscure technical vulnerabilities. The Microsoft Teams incident at a manufacturing company in 2025 tells a different story. The attacker’s most powerful weapon wasn’t code. It was a phone call.
Or rather, a Teams video call, from someone who seemed entirely legitimate.

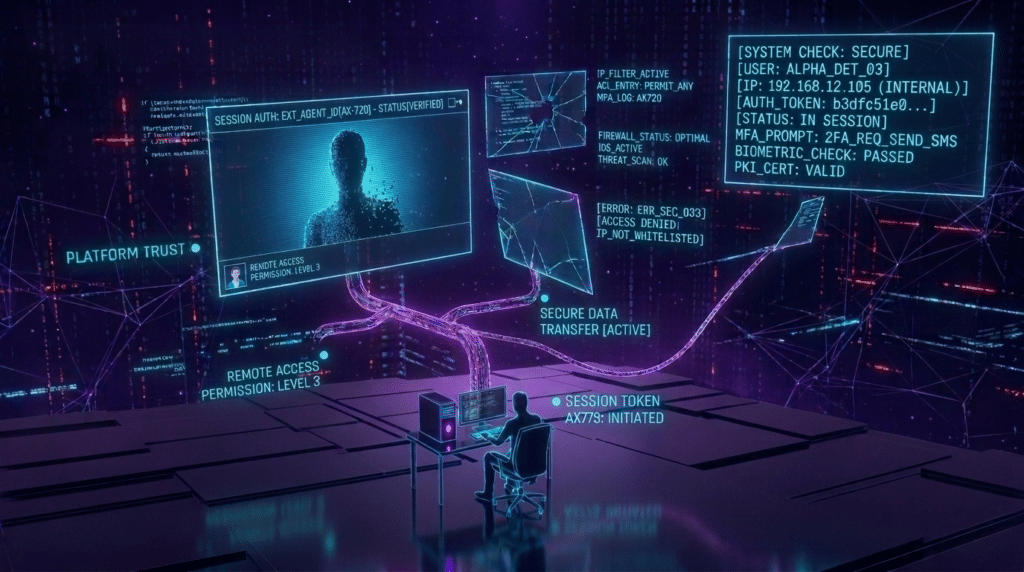
The Setup: Trust as the Attack Surface
An employee received an unexpected contact through Microsoft Teams from an external account. The conversation was framed as a support interaction (the kind of thing that happens dozens of times a day in large organizations). The ‘support agent’ needed to troubleshoot something on the employee’s machine and asked if they could take a look.
The employee agreed. They clicked through the QuickAssist prompt (a legitimate Microsoft remote access tool) and handed over control of their screen. From that moment, the attacker had everything they needed.
Attack Sequence
| Step | Action | Status |
| 01. Foothold | Employee contacted via Teams by external actor posing as support. QuickAssist executed; attacker granted remote control of the endpoint. | Access Achieved |
| 02. Execution | Enumeration commands run; PowerShell command downloads payload from external address. Webshell dropped, providing persistent remote execution capability. | Payload Deployed |
| 03. Expansion | Task creation and deletion commands executed via webshell; reverse shell drop attempted; existing AV tools probed; network reconnaissance underway. | Contained |
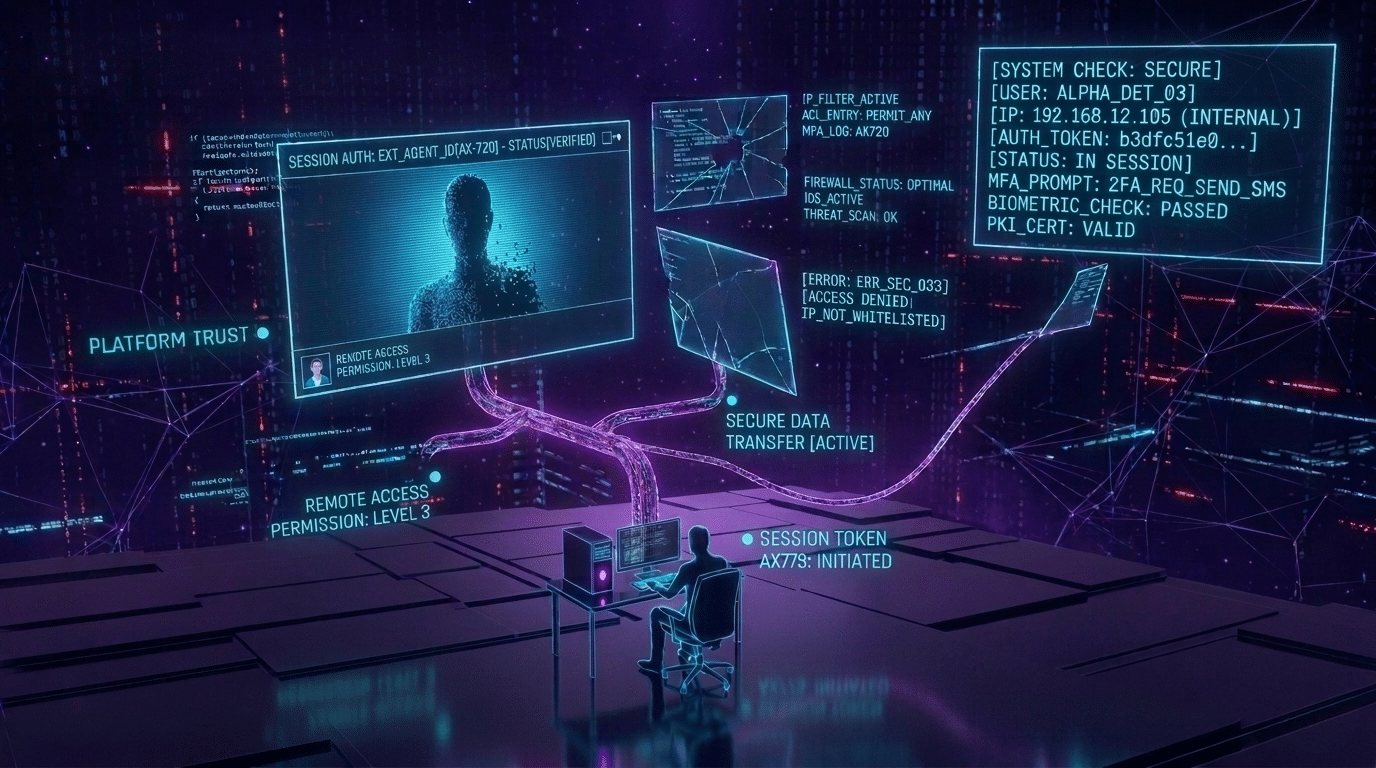
Why Teams? The Logic of Platform Trust
The choice of Microsoft Teams as the attack vector was deliberate. Teams sits at the center of modern enterprise communication. It carries an implicit sense of legitimacy. Messages arrive inside the authenticated corporate environment, not in a junk email folder. And critically, Teams supports external contacts by default in many configurations, meaning a threat actor can initiate a conversation with an employee without any prior relationship.
The ’email bombing and vishing’ variant of this attack, where attackers first flood the target’s inbox to create panic and urgency, then call via Teams or other trusted channels to ‘resolve’ the problem, surged over 500% in 2025. The psychology is straightforward: a confused, overwhelmed employee receiving a helpful call from someone offering to fix a crisis is far more likely to comply than someone approached cold.
The Shift to Identity-Bending Attacks
What the CyOps team observed across 2025 was a fundamental repositioning of the attack surface. Where previous years saw attackers targeting the network perimeter, 2025 saw them targeting the human layer by foregoing phishing emails that security-aware employees could spot, and instead using contextually appropriate, conversational manipulation that sidesteps every technical control.
Similar social engineering tactics were using in two high-profile breaches that set the template years earlier: the 2023 MGM Resorts attack, where Scattered Spider social-engineered the IT help desk over a phone call to reset an employee’s MFA credentials, triggering a $100M+ outage; and the 2023 Clorox breach, in which attackers similarly used voice-based manipulation to gain initial access, ultimately disrupting manufacturing operations and costing the company an estimated $49M in recovery. Ongoing Teams incidents show that despite public warnings, voice and conversational social engineering remains one of the most reliable and lightly-defended entry points in enterprise security.
Social Engineering Risks are Compounding
Traditional security awareness training teaches employees to spot suspicious emails. It does not always prepare them for a helpful phone call from someone using a trusted corporate platform. The attack surface has shifted from inboxes to conversations, and training programs haven’t caught up.
In 2026, AI will make this dramatically worse. AI-generated social engineering can now produce perfectly localized, context-aware lures in real time, adapting language, referencing accurate organizational details, and mimicking the tone of legitimate internal communications. The traditional red flags of phishing (grammatical errors, generic greetings, suspicious links) are disappearing.
What Defenders Must Do Differently
The manufacturing incident was contained quickly through network isolation, enabled by MDR capabilities detecting anomalous behavior in near real time. Without that, the webshell would have provided a persistent foothold for weeks or months.
Three defensive priorities stand out from this case:
- Review Microsoft Teams external access settings: many organizations have external contact enabled by default, and for many the right posture is to require approval before external parties can initiate contact.
- Expand security awareness training: ensure training goes beyond email phishing to include social engineering through collaboration platforms, including realistic simulations involving voice and video calls.
- Monitor end-user deployment of remote access tools: even legitimate tools like QuickAssist should trigger alerts and require validation before proceeding.
The Bottom Line
Some of the most dangerous attacks in 2025 didn’t require a single line of exploit code. They required a convincing conversation. When identity becomes the perimeter, the controls designed to protect the network offer no protection at all, and human risk requires defenses that go beyond phishing simulations.