CISOs and security administrators often face the dilemma of which cybersecurity approaches to incorporate into their strategies. While there are a number of security frameworks to choose from, two of the most popular are Zero Trust and Defense in Depth.
Both Zero Trust and Defense in Depth are comprehensive cybersecurity methodologies and some would argue that they are complementary. This post will provide a guide to both approaches, explain why we think Zero Trust is a superior framework, and share tips so you can choose the best approach for your organization.
What Is Zero Trust?
Zero trust as a cybersecurity methodology has become very popular because it prevents internal as well as external intrusions with a single solution suit.
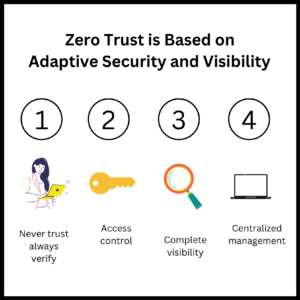
The Zero Trust cyber security approach is based on the premise that no one from inside or outside the organization can be trusted before being verified. In this approach, no user or entity that tries to access applications or services from inside or outside a corporate network is automatically trusted.
The framework is founded on several basic principles that aim to identify the user’s intent and risk:
Zero Trust Basic Principles:
- Attackers may come from anywhere: Attackers may come from inside or outside the network, thus you don’t trust any machines or users by default.
- Least-privilege access: One of the main pillars of zero trust security is applying the principle of least-privilege access. This means each user only has access to what they need to complete their tasks.
- Don’t trust endpoints by default: In Zero Trust, endpoints are never trusted by default, though the system will validate an endpoint if it has sufficient security controls. Authentication extends to endpoint security to ensure that only approved devices can access the network.
- Use multiple authentication methods: One of the basic features of Zero Trust security is the usage of multiple authentication methods. Multi-factor authentication (MFA) provides strong authentication measures, in case of one authentication failing.
- Segment the network: The Zero Trust framework uses network microsegmentation to enhance security. It separates the network into smaller regions with separate access, which helps prevent lateral movement.
- Access control is a must: Zero Trust frameworks enforce strict access controls and constantly monitor the network to ensure each user and device is authorized. This effectively minimizes the attack surface.
What Are the Top Zero Trust Use Cases?
While a Zero Trust implementation can be applicable to many cases, here are the three top examples:
- Your organization has to secure third parties working inside the network
- Your organization has a hybrid or remote workforce
- Your organization uses IoT devices and sensors
How Is an XDR an Important Component of a Zero Trust Strategy?
Extended detection and response (XDR) is an effective security measure to provide holistic protection against malicious actors. While these solutions have merits on their own, when combined with a Zero Trust framework, they strengthen the organization’s security posture.
There are two main features in XDRs that support zero trust implementations:
- Robust endpoint protection: provides visibility into endpoint activities and potential threats.
- Comprehensive data collection and correlation: constant correlation and monitoring allows for continuous assessment of the assets’ security status.
Combining Zero Trust with XDR has the advantage of simplifying the work of security teams. The XDR detects security vulnerabilities and gaps, alleviating the work for security teams.
What Is Defense in Depth?
Defense in Depth is a cyber security strategy that uses multiple security measures to protect an organization’s system or assets. If one line of defense is compromised, the additional layers of protection can compensate and ensure continuous protection.
The Defense in Depth framework uses a combination of security tools and technologies to protect the organization’s network, endpoints, applications, and data. The framework not only focuses on preventing attacks but also stops an attack already underway.
What Are the Basic Principles of Defense in Depth?
Defense in Depth works under the principle of building many layers of security. The layers may consist of firewalls, secure gateways, intrusion detection systems, and authentication measures. The elements of defense in depth include:
- Network security controls
- System monitoring
- Endpoint protection
- Antivirus software
- Data integrity analytics and data protection
- Behavioral analysis and access control
The levels go one on top of the other, and the multiple layers of protective methods serve as a backup in case other security measures fail.
Common use cases for Defense in Depth include regulated industries and end-user and network security. Organizations use Defense in Depth approaches for data protection.
What Are the Key Differences between Zero Trust and Defense in Depth?
While a Zero Trust strategy may use some elements of defense in depth, the frameworks are not equivalent
| Benefits | |
| Zero Trust | Defense in Depth |
| Better protection against internal and external threats. | Easy to implement in large organizations. |
| If done right, can help improve the user experience. | The multiple layers work as backups of each other, keeping critical data safe from attacks. |
| Cost effective in the long run. | Defense in layers slows down attackers. |
| Drawbacks | |
| Zero Trust | Defense in Depth |
| Costly and complex to implement and maintain. | Difficult to coordinate multiple security layers. |
| If not done right, it can slow the user experience. | Gives a false sense of security. |
| The complexity may make it impractical to install in large organizations. | Costly because it involves using multiple security products. |
Which Cybersecurity Model Is Right for Your Company?
Can Zero Trust and Defense in Depth complement each other? You can, indeed, include Zero Trust principles as part of a general Defense in Depth strategy. However, doing so is impractical, and you won’t derive the true benefits of either framework.
Furthermore, it is said that Zero Trust is intended to replace Defense in Depth, and this is partly true. At the end of the day, Zero Trust delivers a more solid security model. The benefits far outweigh the challenges. Moreover, when combined with an XDR, the advantages of a Zero Trust approach truly shine.
If you want to learn more about how a comprehensive Zero Trust model can work for you, let’s chat!