Achieved 100% protection in 2024
Stop advanced cyber
threats with one solution
Cynet’s All-In-One Security Platform
- Full-Featured EDR and NGAV
- Anti-Ransomware & Threat Hunting
- 24/7 Managed Detection and Response
Malware is a software program designed to perform malicious activities. Different types of malware have different capabilities, such as monitoring browser activity, granting remote access to a computing device, stealing sensitive information, and encrypting data in exchange for a ransom.
Many malware infections occur through social engineering methods, in which attackers coerce users into clicking links to malicious websites or opening malicious email attachments. Other ways in which malware infects devices include drive-by downloads (triggered without any user action on a compromised website), installation of seemingly benign programs that deploy malware, and exploitation of vulnerabilities in software and communication protocols.
Antivirus software has been available since the 1980s, and was traditionally based on signature-based malware detection. Legacy antivirus tools contain a database of known malware signatures, and when one is detected on a machine, the tool is able to block and remove it.
Signature-based malware detection is still a core part of malware protection strategies, but it is not enough. New technologies like next generation antivirus (NGAV) add several more layers of protection. Most notably, they perform behavioral analysis, based on machine learning algorithms, which can help identify new malware that does not match any known signature.
This is part of an extensive series of guides about information security.
Related content: Read our guide to malware prevention, dll malware, redline stealer.
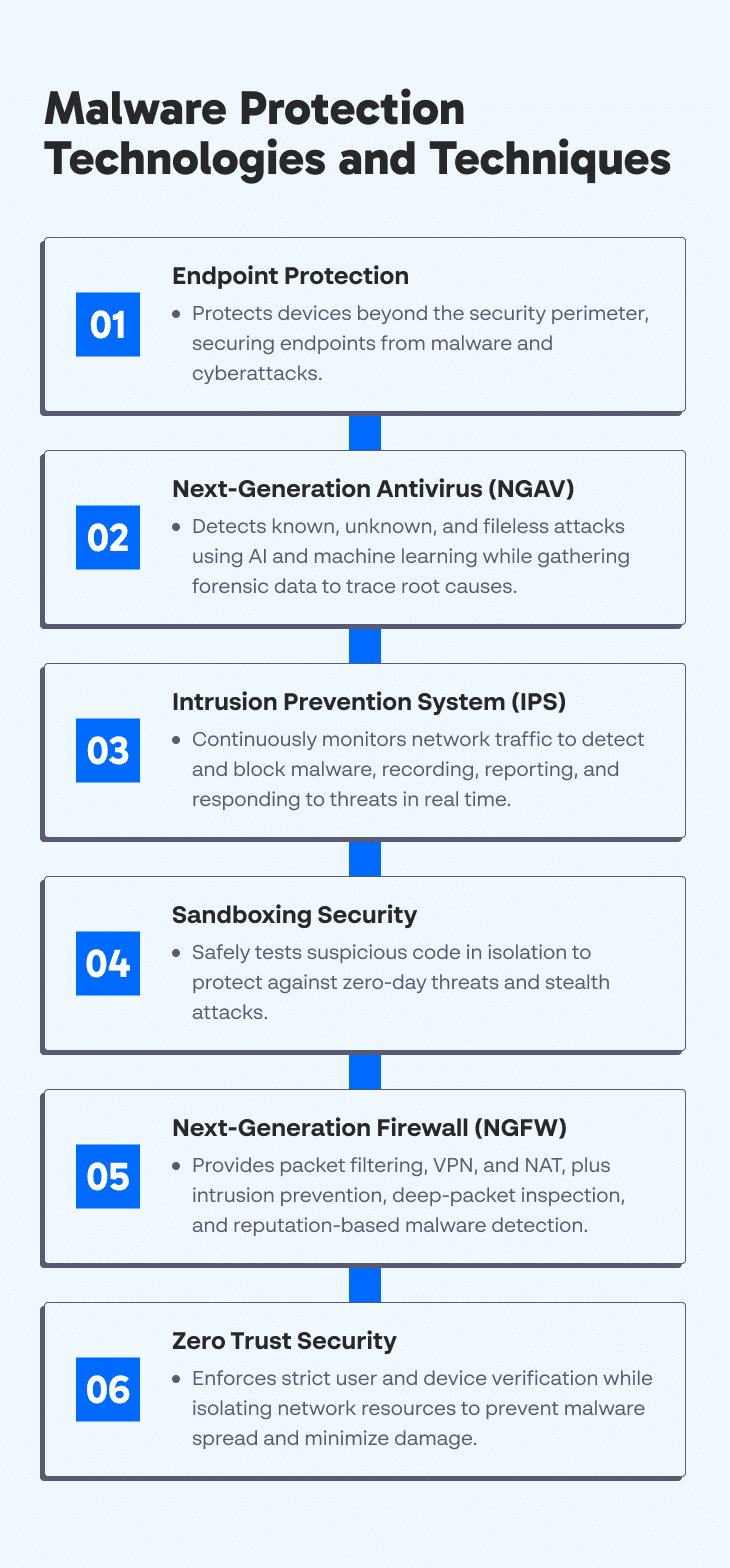
Endpoint protection tools provide security coverage to prevent endpoint breaches and protect IT (IT) systems against endpoint threats, including malware infections and various cyberattacks.
Endpoint protection extends visibility into devices that are traditionally outside the security perimeter, such as personally-owned laptops and tablets used for work purposes, as well as company-owned servers and workstations.
Learn more in our detailed guide to cyber attacks 2020, sunburst attack, emotet analysis.
Next-Generation Antivirus (NGAV) solutions monitor and respond to attacker tactics, techniques, and procedures (TTPs) to help prevent both known and unknown threats. This technology was created to fill in the gaps left by traditional antivirus software that can only defend against known, file-based malware attacks.
NGAV technology offers a cloud-based, system-centric approach. It employs predictive analytics powered by machine learning (ML) and artificial intelligence (AI) in combination with threat intelligence to detect attacks, collect forensics data, and respond to threats. NGVA can identify fileless non-malware attacks, malicious behaviors, and malware, respond to threats, and collect endpoint data to determine the root cause.
An intrusion prevention system (IPS) continuously monitors network traffic to identify an ongoing malware infection or security breach. It can also perform response actions during specific cases that were pre-defined by the network administrator.
IPS continually monitors the network in real-time to quickly identify and respond to potential threats, performing prevention actions for observed events. It works by examining network traffic flows for malicious software. The technology identifies malicious activities, records detected threats, reports detected threats, and takes preventative actions to block the threat.
Sandboxing security provides an additional layer of protection against security threats. It involves using a sandbox, an isolated environment mimicking end-user operating environments, to execute suspicious code.
A sandbox provides a safe environment that separates the threat from the host device or network. It is particularly useful when dealing with zero-day malware and stealth attacks, ensuring you can isolate and check these threats to prevent them from spreading.
A next-generation firewall (NGFW) enforces security policies to detect and block sophisticated attacks at the protocol, port, and application levels. You can implement this third-generation firewall technology in hardware or software.
Data traversing the Internet or a network is split into small pieces called packets. Firewalls inspect these packets because they contain content requesting to enter the network. The firewall is responsible for blocking or allowing packets, working to prevent malicious content, including malware, from entering the network.
NGFWs employ traditional firewall capabilities alongside new and improved features. Traditional capabilities include:
NGFW extends the above with quality of service (QoS) functionality and additional features, such as:
The zero trust model is a security approach that removes implicit trust and enforces strict user and device authentication to protect the network. It helps provide strong protection against various attacks, including data theft and compromised credentials. Zero trust implementations often employ role-based policies to enforce strict authentication and authorization rules.
This model assumes that trusting individuals or devices can cause many vulnerabilities, as even authorized parties can become compromised. The network should never trust any user and require identity and device authentication throughout the network and not only at the perimeter.
Implementing zero trust security typically involves using microsegmentation to separate network resources. Isolating resources helps contain threats within one microsegment of the network, preventing the threat from spreading to other areas. It minimizes the attack surface and reduces the scope of damage inflicted by an attack.
Zero trust helps create a more comprehensive defense against malware and ransomware attacks by providing extended monitoring and detection capabilities. Zero trust can significantly limit the ability of malware and ransomware to perform lateral movement and infect additional parts of a corporate network. In addition, since human error is often the root cause of a cyberattack, zero trust focuses on user identity and access management.
Learn more in our detailed guide to hafnium, squirrel waffle, quakbot.
After you deploy the best possible malware protection solutions, follow these best practices to better protect your organization against malware threats:
Learn more in our detailed guide to bladabindi, clipbanker, emotet analysis, defense evasion.
Tips From the Expert
In my experience, here are tips that can help you better protect your environment from malware threats:
The Cynet 360 Advanced Threat Detection and Response platform provides protection against threats including zero-day attacks, advanced persistent threats (APT), advanced malware, and trojans that can evade traditional signature-based security measures.
Block exploit-like behavior
Cynet monitors endpoints memory to discover behavioral patterns that are typical to exploit such as an unusual process handle request. These patterns are common to the vast majority of exploits, whether known or new, and provide effective protection even from zero-day exploits.
Block exploit-derived malware
Cynet employs multi-layered malware protection that includes ML-based static analysis, sandboxing, and process behavior monitoring. In addition, they provide fuzzy hashing and threat intelligence. This ensures that even if a successful zero day exploit establishes a connection with the attacker and downloads additional malware, Cynet will prevent this malware from running so no harm can be done.
Uncover hidden threats
Cynet uses an adversary-centric methodology to accurately detect threats throughout the attack chain. Cynet thinks like an adversary, detecting behaviors and indicators across endpoints, files, users, and networks. They provide a holistic account of the operation of an attack, irrespective of where the attack may try to penetrate.
Accurate and precise
Cynet uses a powerful correlation engine and provides its attack findings with near-zero false positives and free from excessive noise. This simplifies the response for security teams so they can react to important incidents.
You can carry out automatic or manual remediation, so your security teams have a highly effective yet straight-forward way to detect, disrupt, and respond to advanced threats before they have a chance to do damage.
Learn more about Cynet’s Next-Generation Antivirus (NGAV) Solution.
Learn more in our detailed guide to emotet malware, china chopper.
Zeus Malware: Variants, Methods and History
Zeus is one of the most dangerous and globally widespread network security threats. It has allowed attackers to obtain user credentials to financial systems, and actually steal funds from the bank accounts of millions of people.
Learn about the dangerous and globally-spread Zeus malware, which infects machines, steals financial credentials and illicitly transfers funds.
Read more: Zeus Malware: Variants, Methods and History
Malware Prevention: A Multi-Layered Approach
Malware, or “malicious software,” is a general term describing any program created to disrupt or unlawfully retrieve information from a computer system.
Get a modern definition of malware, examples of malware attacks, and 5 steps to creating a multi-layered security posture.
Read more: Malware Prevention: A Multi-Layered Approach
4 Malware Detection Techniques and Their Use in EPP and EDR
Threat actors employ malicious software, known as malware, to perform certain malicious activities. There are numerous types of malware, each deployed to achieve different objectives. For example, spyware aims to gather information from computing devices, trojans aim to gain a persistent hold on a computer system, and ransomware aims to encrypt information and extort its owners.
Learn about innovative static and behavioral malware detection techniques and how they are used in modern endpoint protection solutions.
Read more: 4 Malware Detection Techniques and Their Use in EPP and EDR
9 Types of Malware Attacks and What You Can Do About Them
Malware is a program or file that intentionally damages or grants unauthorized access to a computer system. In other cases malware is used to destroy or steal sensitive data. Malware can infect devices, operating systems, and networks. Depending on the type and purpose of the malware, infection can have different levels of impact on users, endpoints, and organizations.
Learn about the main types of malware attacks including ransomware, fileless attacks, trojans, and rootkits, and discover critical best practices to prevent them.
Read more 9 Types of Malware Attacks and What You Can Do About Them
Together with our content partners, we have authored in-depth guides on several other topics that can also be useful as you explore the world of information security.
Authored by Cynet
Authored by Cynet
Authored by CyCognito
Search results for: