Built for speed. Powered by simplicity.
Network and User Security
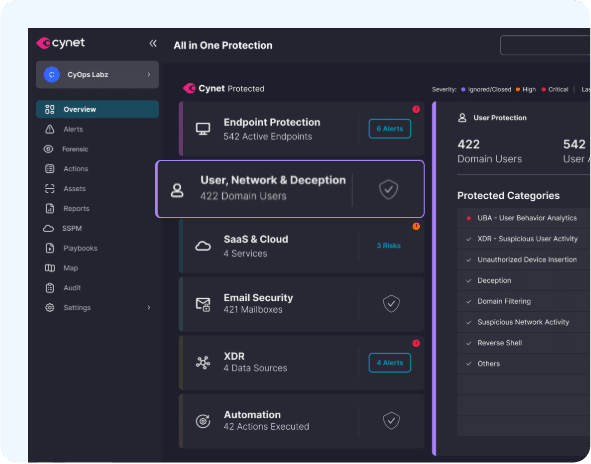
Combining network and user security with other Cynet protections form a multi-layered defense strategy that addresses multiple attack vectors. This holistic approach is crucial for effectively mitigating threats and protecting organizational assets.
Jump to Section
01
Cynet detects stealthy threats and anomalous behaviors across your network, analyzing interactions with devices and users to provide high fidelity threat detection. Network signals are combined with other Cynet native telemetry for unparalleled threat visibility and detection accuracy.

Network Scan Detection
Identify patterns of activity indicative of malicious network scanning activity

DNS Attack Detection
Identify a variety of attacks targeting the DNS infrastructure.

Deception
Deploy decoy hosts and servers, and monitor for unauthorized access.

Tunnel Exfiltration Detection
Protect against exfiltration of sensitive data even through encrypted communication pathways.

Risky Connection Detection
Identify active communication with malicious sites to protect against malware distribution, phishing, and known C2C based communication.

Port Scanning
Identify vulnerable ports and suspicious port scanning activities to minimize the risk of adversary exploitation
02
Cynet continuously monitors user activity to pinpoint suspicious behaviors that are indicative of compromised accounts and malicious insiders. User behavior signals are combined with other Cynet native telemetry for unparalleled threat visibility and detection accuracy.

Windows Events Visibility
Continuously correlate user activities against other events — on endpoints, files and external network locations — to provide holistic information to determine real-time risk levels

Full Environment Visibility
Continuously correlates user activities against other events — such as endpoints, files and external network locations — to determine real-time risk levels.

Malicious User Identification
Rapidly detect suspicious user activities such as lateral movement, C&C activity, accessing bad domains, etc.

Lateral Movement Detection
Detect the use of compromised credentials accessing network assets.

Anomaly Detection
Detect abnormal user behaviors such as lateral movement, C&C activity, accessing bad domains, etc.

User Visibility
Visibility into all user activity and login events.

Deception
Deploy decoy users and monitor for unauthorized access.
03
Cynet Domain Filtering restricts access to specific domains and leverages domain categorization to block entire categories of potentially harmful websites.

Cynet Domain Filtering prevents endpoints from connecting to malicious or compromised websites.

Configure and enforce granular policies based on domain categories, allowing or blocking website access based on content (e.g., gambling, social media, etc.).

Choose between detection and prevention modes to either alert on or block connections to malicious domains, providing adaptable security measures.

Monitor all Windows-based endpoint browsers and processes regardless of endpoint location or connection (in/outside the corporate firewall).

Protect across all browsers and network protocols (ex., HTTP, HTTPS, TCP).

Whitelisted domains and alerts are configurable.