Through ongoing research and hands-on incident response engagements, Cynet Research and the CyOps team have observed a growing increase in identity-centric attack activity targeting enterprise Microsoft Entra ID (Microsoft 365) environments. Across investigations spanning multiple industries, these campaigns increasingly combine phishing-based credential or token theft, abuse of automation tooling, and non-interactive authentication techniques, enabling threat actors to bypass traditional security controls and compromise cloud identities at scale.
CyOps, Cynet’s managed detection and response team, works alongside Cynet Research to investigate and respond to real-world attacks across customer environments.
- Category: ITDR – Identity Threat Detection & Response
- Incident Flow: Phishing –> Token Theft –> Token Abuse –> Mailbox Manipulation
- Impacted Platform: Microsoft Entra ID (Microsoft 365)
During the investigation, Cynet’s Identity Threat Detection and Response (ITDR) capabilities identified anomalous and high-risk identity activity targeting a Microsoft Entra ID account. Rather than a single noisy alert, the activity emerged through a combination of subtle signals, including non-interactive authentication attempts using an atypical user agent, access attempts from previously unseen geographic locations, and the creation of unauthorized inbox rules.
When analyzed together, these indicators pointed to misuse of authentication artifacts, such as session token abuse, rather than a traditional password compromise. The authentication patterns observed were inconsistent with normal user behavior and reflected the use of automation tooling, allowing the threat actors to operate quietly without triggering common password-based defenses.
As the activity progressed, Cynet observed the creation of inbox rules designed to redirect or suppress email communications, a technique frequently used to maintain covert access and reduce user visibility following identity compromise. This mailbox manipulation represented a clear shift from initial access to post-authentication abuse, signaling threat actors’ intent to persist and monitor sensitive communications.
By correlating these low-noise identity signals, Cynet ITDR was able to surface behavior consistent with business email compromise (BEC) tradecraft before overt impact occurred. This incident illustrates how modern identity attacks rely on legitimate platform features and automation, and why behavioral identity analytics are essential for detecting threats that bypass traditional authentication and endpoint-focused controls.
Key Takeaways
- Cynet ITDR identified early indicators of an identity-based attack, beyond simple login failures.
- The activity suggests session token misuse, not confirmed password compromise or malware involvement.
- Unauthorized inbox rule creation confirms post-access persistence and potential email data exposure.
- The behavior aligns with modern Business Email Compromise (BEC) and Microsoft 365/Entra ID account takeover trends.
- Cynet’s behavioral identity analytics are designed to detect these evolving attacks that bypass traditional authentication controls.
| Tactic | Technique | ID |
| Initial Access | Phishing | T1566 |
| Valid Accounts: Cloud Accounts | T1078.004 | |
| Credential Access | Steal Application Access Token | T1528 |
| Persistence | Hide Artifacts: Email Hiding Rules | T1564.008 |
| Collection | Email Collection: Email Forwarding Rule | T1114.003 |
Technical Analysis: Identity Compromise and Post-Authentication Abuse
MITRE ATT&CK:
- Initial Access – Phishing (T1566)
In this specific case, Cynet assesses phishing email delivery as the most likely initial access vector. Direct evidence of the phishing email was not captured, as the investigation began after post-exploitation activity had already occurred, limiting visibility into the initial delivery phase of the attack.
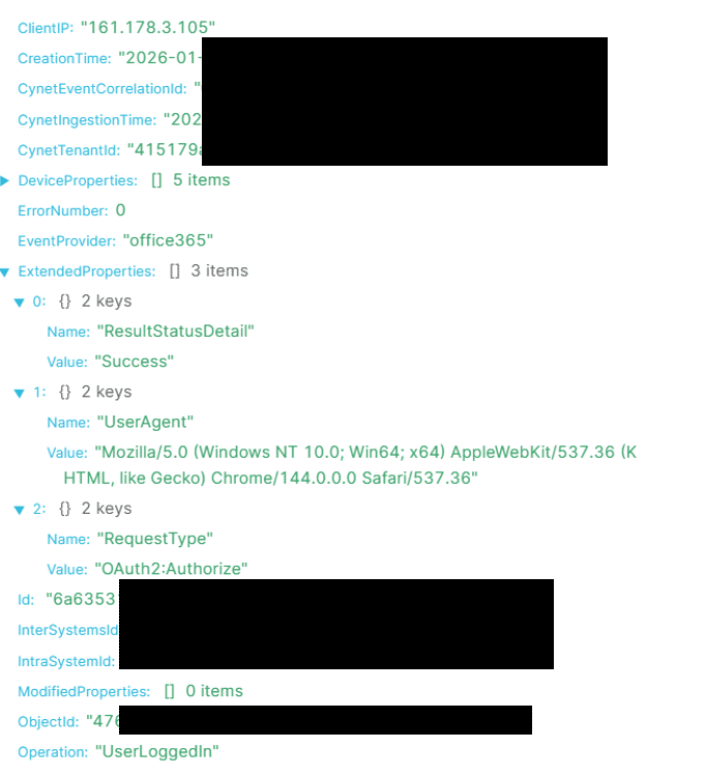
Automated Authentication Attempts Using Non-Standard Client
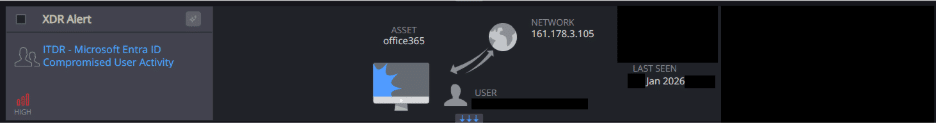
Cynet ITDR detection alert, high severity:
MITRE Mapping:
- Credential Access – Steal Application Access Token (T1528)
- Initial Access – Valid Accounts: Cloud Accounts (T1078.004)
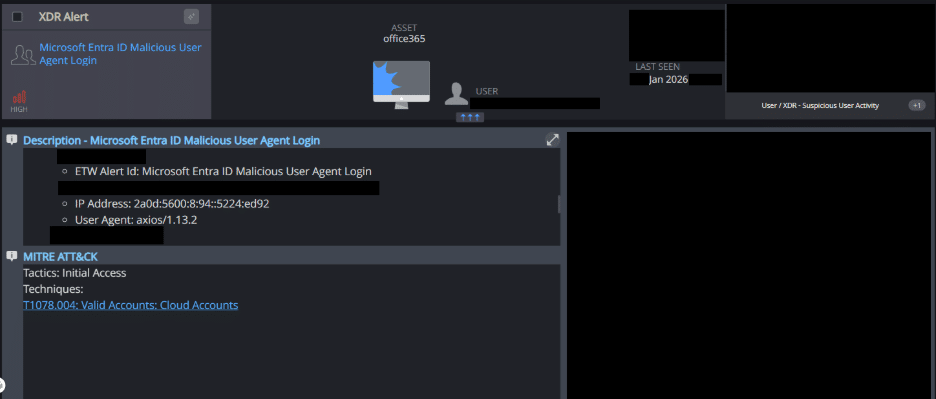
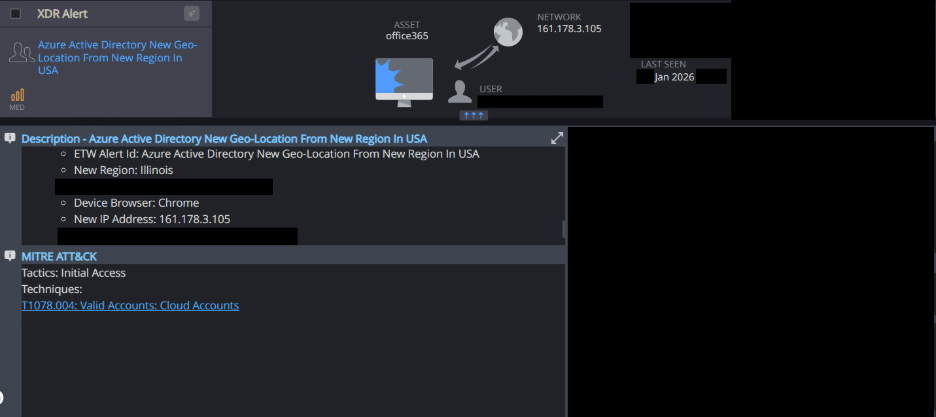
In this incident, Cynet observed automated authentication attempts performed using a non-standard HTTP client, specifically Axios, rather than an interactive browser session. By issuing authentication requests programmatically, the threat actor was able to control authentication flow and session handling without relying on user-driven login behavior.
In the activity detected by Cynet, authentication attempts identified themselves with the user agent axios/1.13.2 and leveraged authentication behavior associated with persistent sign-in sessions (for example, “Keep Me Signed In”).
Observed Activity:
- User Agent: axios/1.13.2
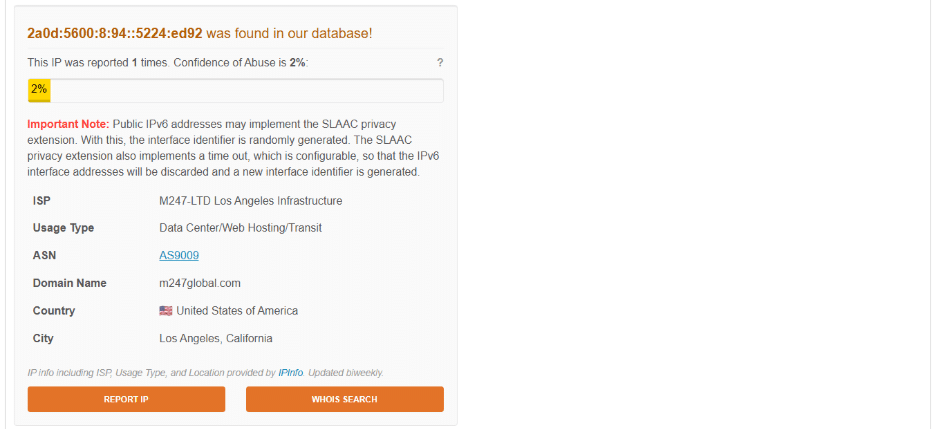
- Source IP (IPv6): 2a0d:5600:8:94::5224[:]ed92
- Authentication Method: KMSI
- Geo-Location: United States, California
Authentication Attempts from New Geographic Location
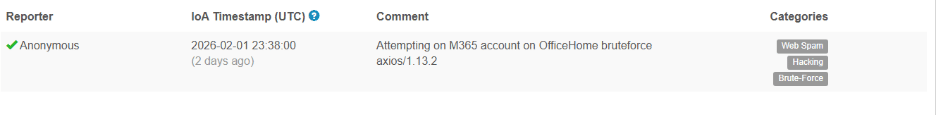
Cynet ITDR detection alert, new Geo-location:
MITRE Mapping:
- Initial Access – Valid Accounts: Cloud Accounts (T1078.004)
Cynet identified a technique in which threat actors leverage AWS API Gateway pass-through proxies to evade traditional source-IP–based aggregation and detection.
AWS API Gateway can be configured as a transparent pass-through proxy, allowing threat actors to forward authentication requests through AWS-managed infrastructure. In this configuration, each request can originate from a different AWS-controlled IP address, effectively rotating the apparent source IP on a per-request basis.
This technique highlights the importance of behavioral correlation, including user agent analysis, authentication patterns, and post-authentication action.
One commonly abused implementation of this technique is FireProx, an open-source tool that automates the creation of API Gateway endpoints.
Observed Activity:
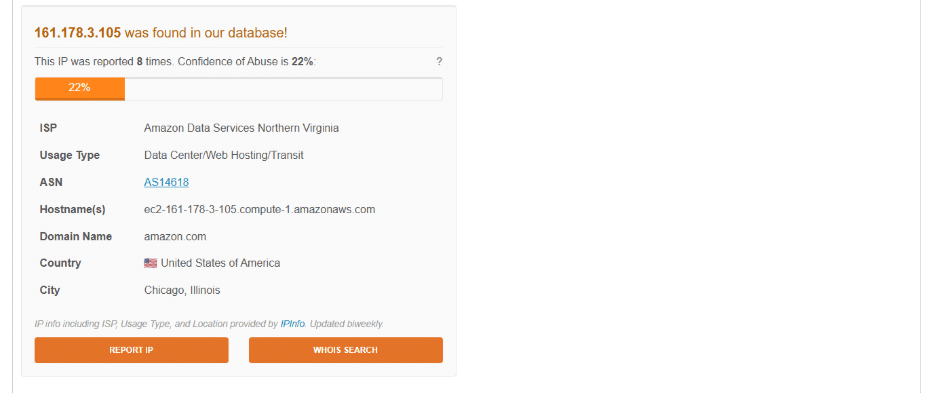
- Source IP: 161.178.3[.]105
- Location: Previously unseen U.S. region
- Reputation: IP associated with potential fraud or spam activity
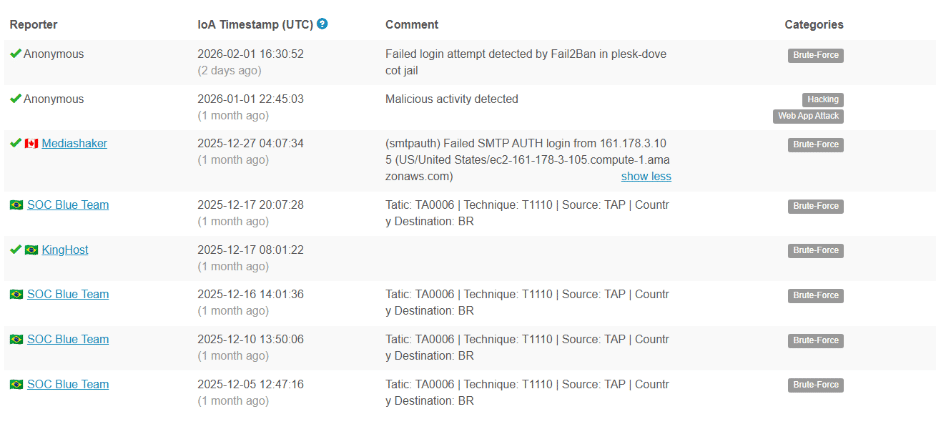
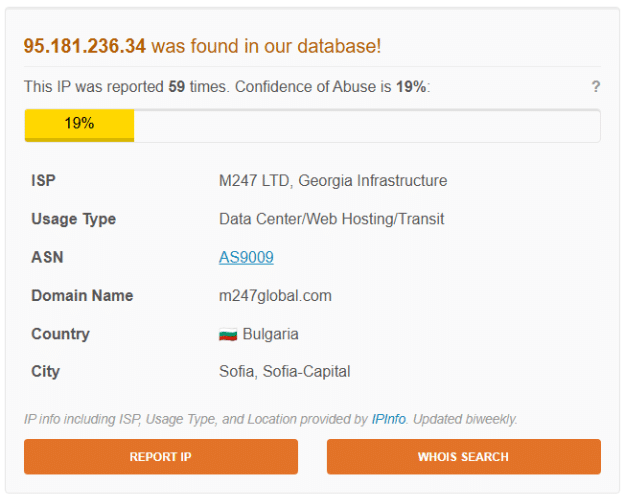
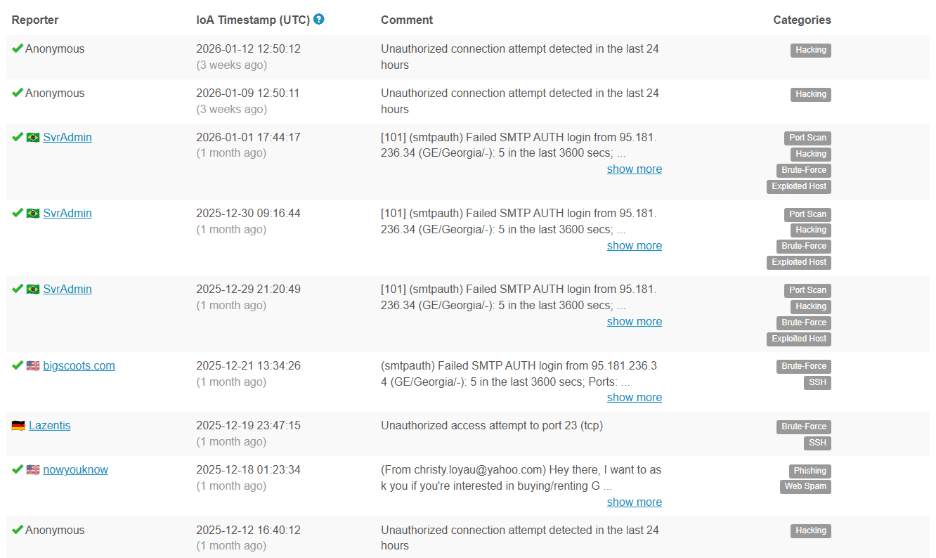
In addition, Cynet observed a subsequent authentication attempt that reused a previously issued authentication artifact. This attempt originated from IP address 95.181.236[.]34 (geolocated to Bulgaria, Europe) and resulted in a failed login with error code 50133 (SsoArtifactRevoked). This error indicates that the authentication artifact presented during the request had already been revoked or expired, preventing successful authentication.
Observed Activity:
- Activity: Failed Login
- Source IP: 95.181.236[.]34
- Geo-Location: Europe, Bulgaria
- Error Code: 50133(SsoArtifactRevoked)
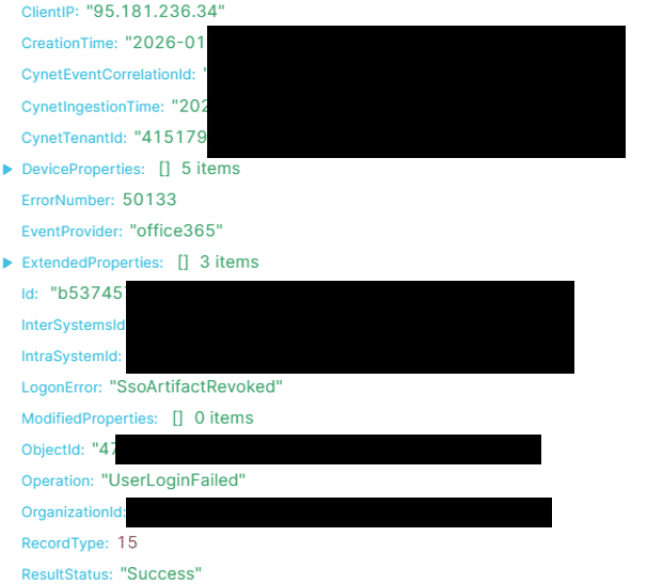
Reputation: IP is again associated with potential fraud or spam activity:
Malicious Inbox Rule Creation
Cynet ITDR detection alert, Suspicious inbox Rule, high severity alert:
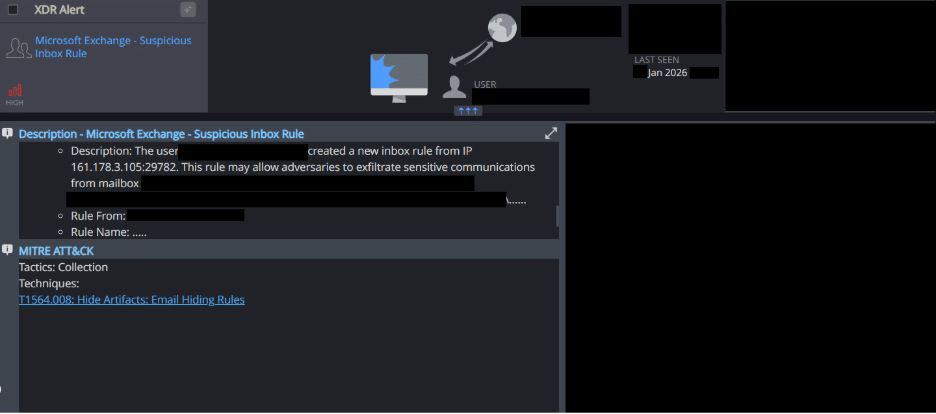
MITRE Mapping:
- Defense Evasion – Hide Artifacts: Email Hiding Rules (T1564.008)
- Collection – Email Collection via Forwarding Rules (T1114.003)
After gaining access, the threat actors did not immediately perform noisy or destructive actions. Instead, they transitioned into a low-profile post-compromise phase, focusing on mailbox manipulation to maintain covert control over ongoing communications.
Cynet observed the creation of inbox rules with non-descriptive, seemingly benign names. This is a common tactic used to evade detection during manual review. These rules were configured to target finance-related email communications, automatically marking messages as read and moving them to the Deleted Items folder.
This mailbox manipulation enabled a highly effective impersonation technique. The threat actors were able to continue corresponding with the finance department using the victim’s identity, while preventing the legitimate user from seeing incoming responses. From the user’s perspective, no new emails appeared, no alerts were triggered, and no obvious indicators of compromise were visible.
Beyond the confirmed malicious inbox rule creation observed in this incident, Cynet has consistently identified similar mailbox abuse patterns across multiple incident response engagements in Microsoft Entra ID environments. In these cases, threat actors leveraged native mailbox features such as inbox rules and message routing to evade detection and maintain persistent, covert access following identity compromise.
Across these investigations, threat actors commonly created or modified inbox rules to forward, delete, or deprioritize inbound messages, enabling the silent collection or suppression of sensitive communications without user awareness. In some environments, Cynet also observed abuse of RSS subscription functionality or related message-handling rules to divert specific categories of notification emails away from the primary inbox, further reducing visibility into security-relevant events. This technique is frequently used in Business Email Compromise scenarios to covertly monitor and influence sensitive email communications.
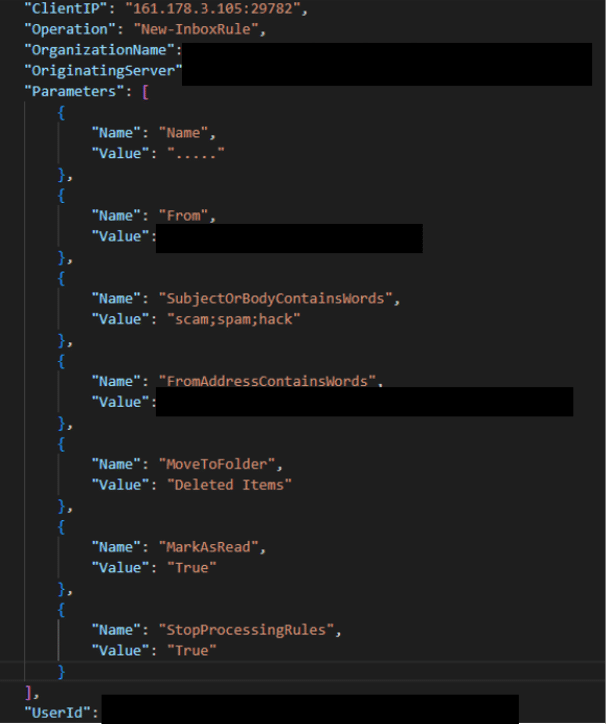
Observed Activity (rule configuration):
- Rule Name: “…..”
- From Address: <REDACTED>
- From Address Contains Word: <DOMAIN>
- Subject Or Body Contains Word: scam, spam, hack
- Mark As Read: True
- Stop Processing Rules: True
- Move To Folder: Deleted Items
Conclusion
Based on the investigation and correlated identity telemetry, these incidents are assessed as a high-confidence identity abuse event affecting a Microsoft Entra ID (Microsoft 365) environment. The observed behavior demonstrates how modern threat actors can maintain covert access using legitimate identity mechanisms, without relying on malware or traditional credential compromise. Cynet’s ITDR capabilities enabled early identification of this activity by correlating subtle authentication anomalies and post-authentication actions into a clear risk assessment. This conclusion underscores the necessity of behavioral, identity-focused security controls to detect and respond to evolving business email compromise and cloud account takeover threats.