Introduction
Cynet’s customers are fully protected against HAFNIUM APT recent campaign targeting MS Exchange
The HAFNIUM attack campaign came to light last week with Microsoft’s public release of the China-sponsored attack group that is actively exploiting on-premises versions of Microsoft Exchange Server. The targeted attack exploits four 0-day vulnerabilities that expose Microsoft’s customers to remote code execution attacks, without requiring authentication. Post exploitation of the vulnerabilities, the HAFNIUM group establishes remote access to the Exchange Server and exfiltrates corporate data, through a series of tools.
In this article we refer to how Cynet 360 detects the usage of these tools and protects customers against HAFNIUM-related attacks.
As part of its research, Cynet also released a blog post last week detailing China Chopper – A tool that was potentially used in the HAFNIUM campaign and by other threat actors – indicating that the latest published Microsoft vulnerabilities were already exploited in the past.
You can read more about “CHINA CHOPPER OBSERVED IN RECENT MS EXCHANGE SERVER ATTACKS” here.
Detection Mechanisms
Customers receive protection via the following Cynet360 security mechanisms:
- Advanced Detection Technology (ADT)
- Memory Protection Mode
- Cynet Anti-Virus (CyAV)
High level overview of the attack
From initial observations it seems that the attack includes the following three steps.
- Gaining access to an Exchange Server – either through stolen passwords or by using the previously undiscovered vulnerabilities to disguise as someone who should have access.
- Controlling the compromised Exchange Server – by creating a web shell and establishing a Command-and-Control server through US-based virtual private servers.
- Exfiltrating data – using the already-established remote access to exfiltrate data from the organization’s network.
Microsoft released emergency patches to the exploited vulnerabilities, and it is important to ensure their patching.
It is important to note that zero-day vulnerabilities will continue to exist. The key to protecting organizations is to ensure the detection of malicious and abused web shell scripts in order to prevent the attacker’s progression in the cyber kill chain (see Appendix: MITRE ATT&CK).
HAFNIUM’s Post-Exploitation Tools
Once the HAFNIUM APT group gained access to the Exchange Server, they used the following tools:
- ProcDump – A legitimate Sysinternals admin tool that the attackers abused to dump the memory of the Local Security Authority Subsystem Service (LSASS) which stores credential materials.
- Nishang and PowerCat – open-source hacking tools that enabled the HAFNIUM group to establish a reverse shell connection from the compromised Exchange Servers to the malicious command and control of the attackers and exfiltrate data. Nishang and PowerCat are frameworks based on PowerShell (PowerShell is commonly used in fileless attacks to prevent their detection by AV and NGAV tools) scripts and payloads.
Cynet protects its customers against Nishang, PowerCat, and ProcDump abuse.
Cynet vs ProcDump Ab(use)
The Cynet 360 platform has full visibility of the Local Security Authority Subsystem Service (LSASS). This is done via hardening policies and detection rules that provide full protection and prevention capabilities against LSASS memory dumping.
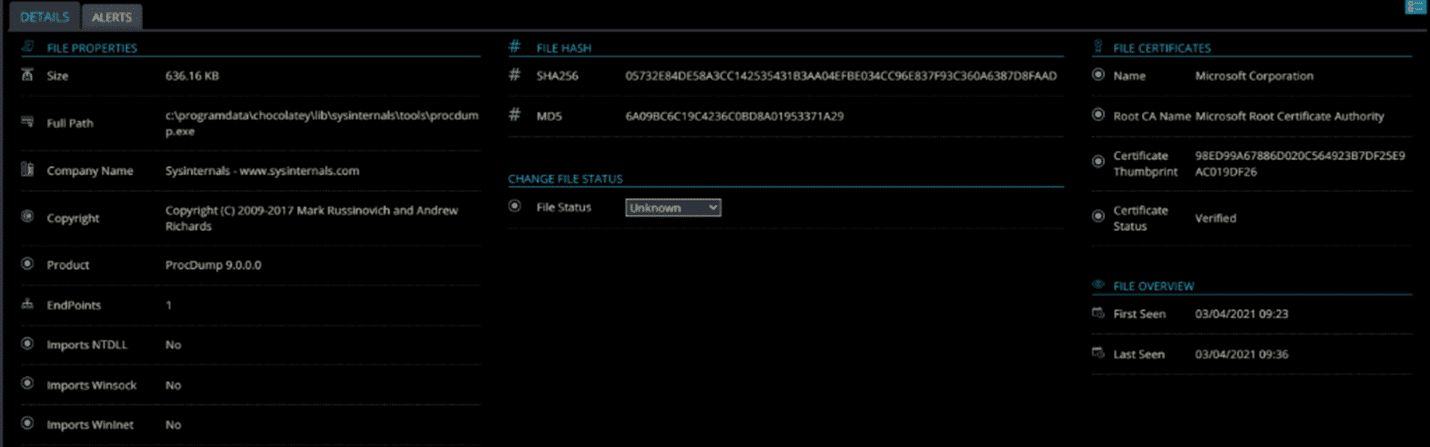
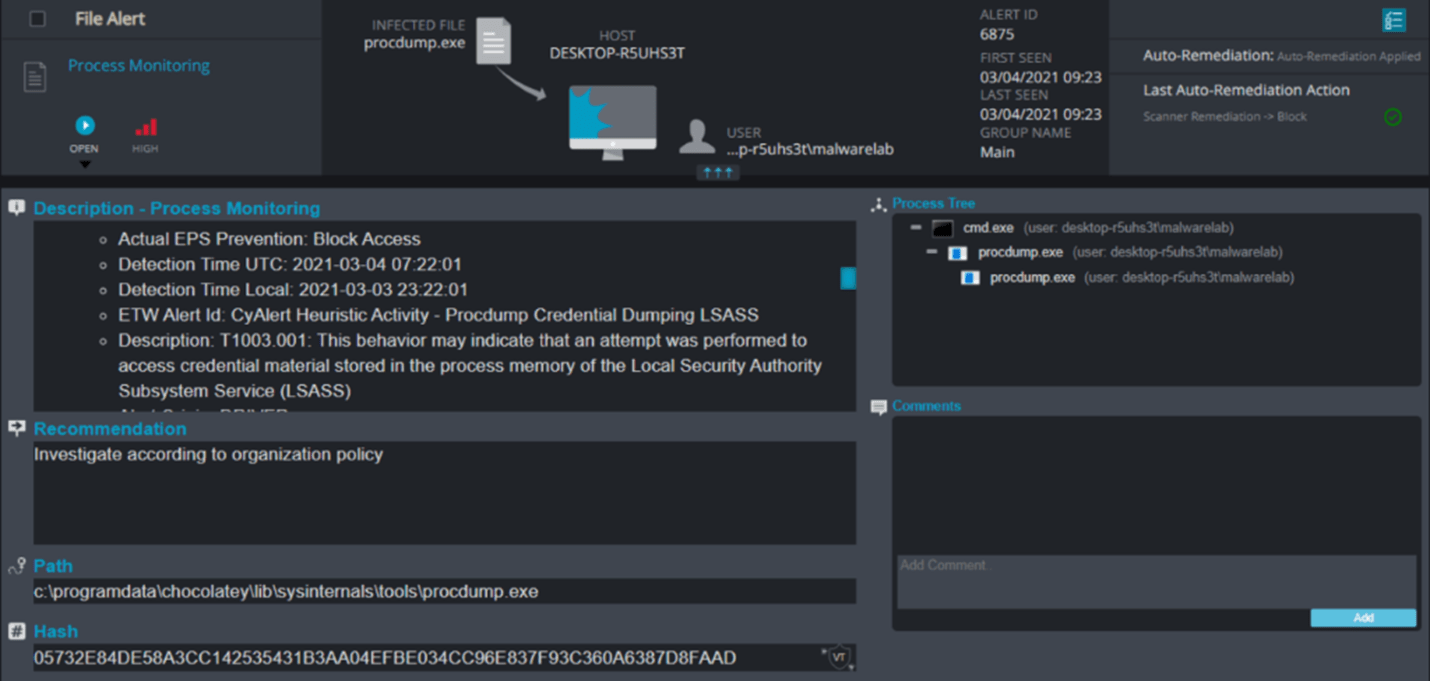
Figure 1: Cynet forensics of ProcDump
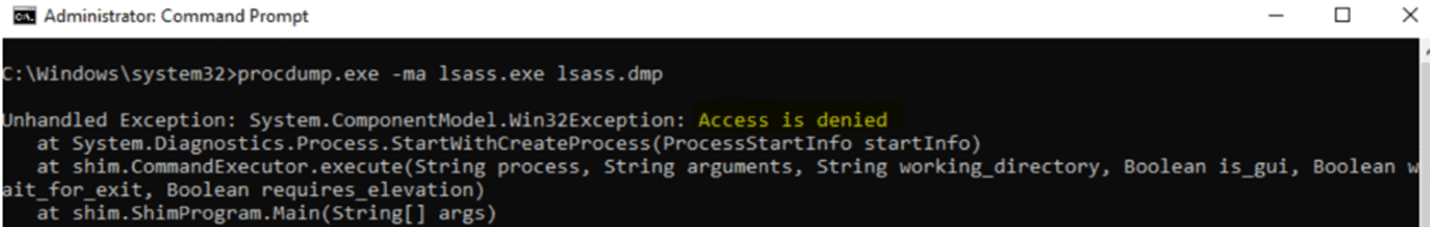
Figure 2: ProcDump command blocked
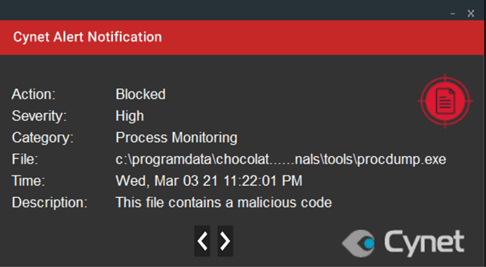
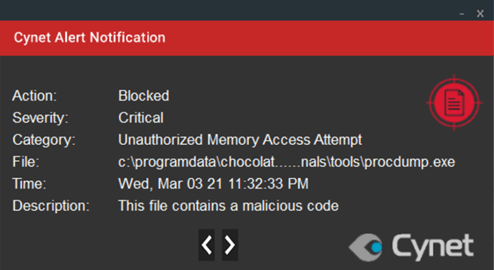
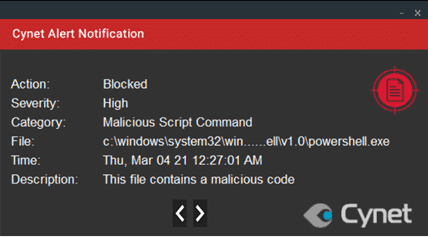
Local Cynet alert notification triggered on the host:
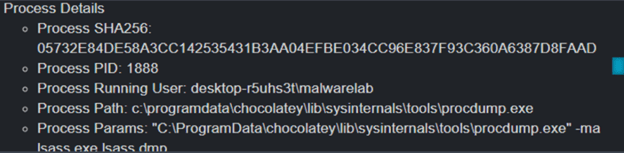
Figure 3: Process Monitoring alert that blocks the ProcDump activity
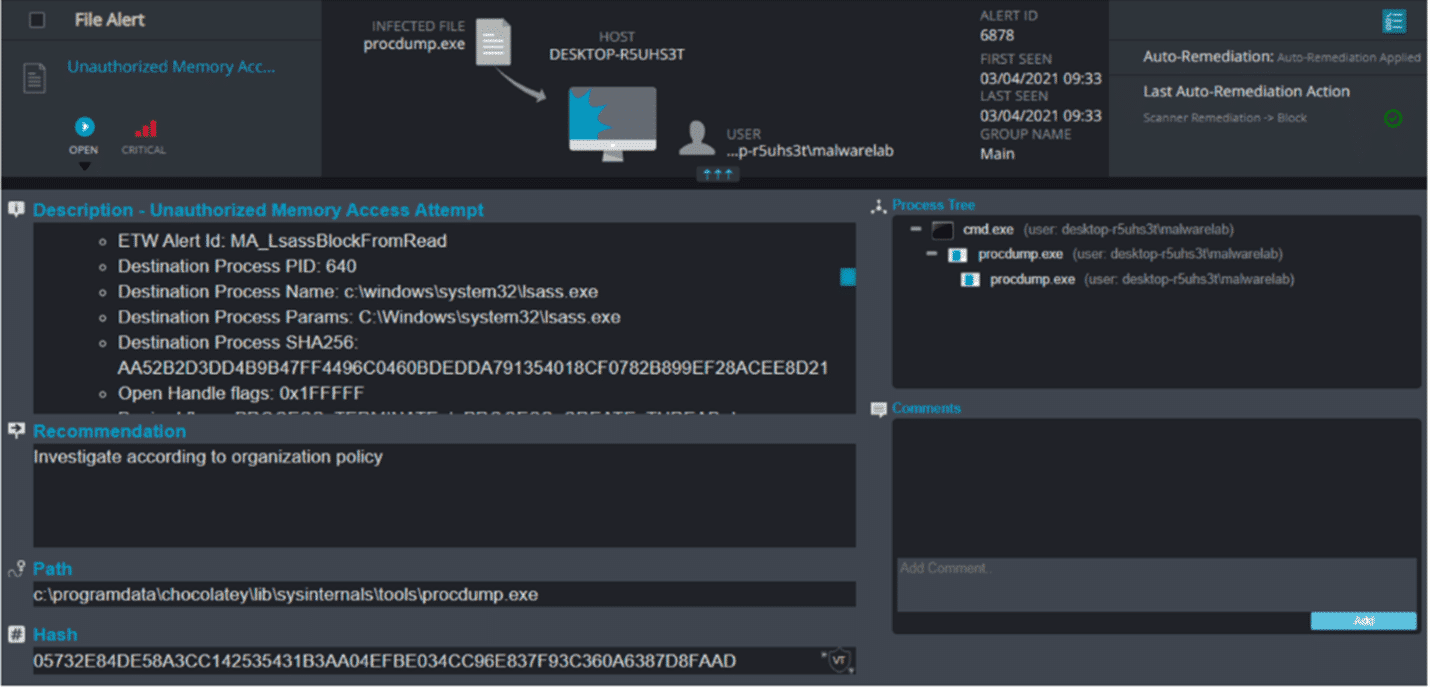
Figure 4: Unauthorized Memory Access Attempt alert that blocks ProcDump access to LSASS memory
Figure 5: Cynet console high severity alert, including complete information of the malicious Procdump activity.
Figure 6: Zooming into alert information as appears in Figure 5.
Figure 7: Cynet console critical severity alert, containing information of LSASS access by ProcDump.
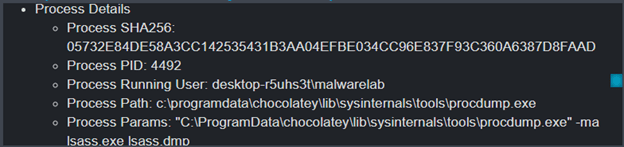
Figure 8: Zooming into alert information as appears in Figure 7.
Cynet vs Nishang and PowerCat PowerShell
Figure 9: PowerShell Powercat fileless command.
Local Cynet alert notifications are triggered on the host:
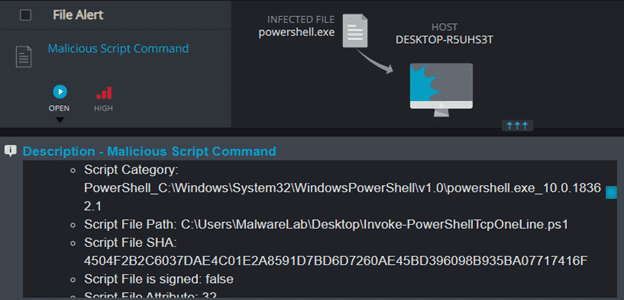
Figure 10: Malicious script command alert that blocks fileless PowerShell command.
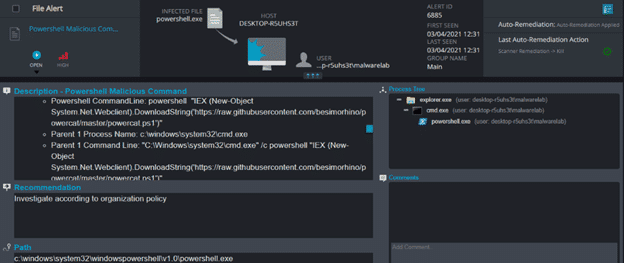
Figure 11: Cynet console high severity alert, containing information of malicious PowerShell command.
As seen, Cynet was able to detect the fileless command. However, were an attacker to use a novel technique to bypass Cynet’s mechanism, Cynet would have regardless blocked the malicious module content from being executed.
This is how it would work:
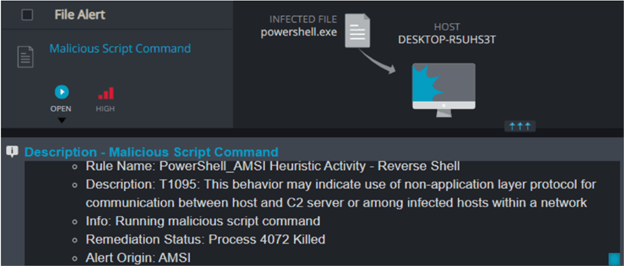
Figure 12: The Cynet detects the next stage of the PowerCat malicious script command and classifies it as a reverse shell execution attack.
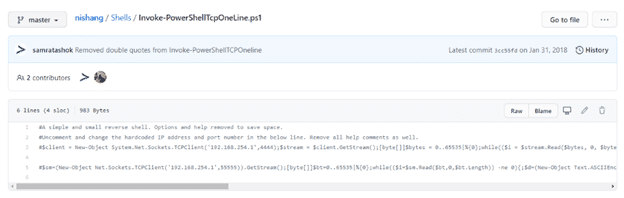
Figure 13: Script of Nishang’s malicious module as taken from Github repository
Figure 14: Cynet detects and prevents Nishang execution using rules related to malicious PowerShell reverse shell command.
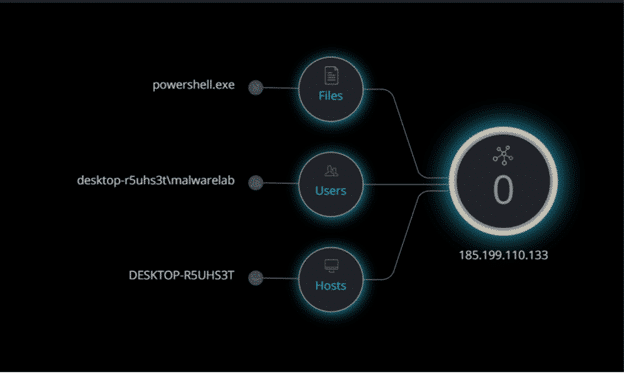
By using Cynet forensics, you can see that the PowerShell instance opens a socket to the 185.199.110.133 IP address which is related to the raw.githubusercontent.com. This is a repository that stores the Nishang and PowerCat content.
Figure 15: Cynet network forensic capabilities displays PowerShell socket to external IP
Appendix
Who is HAFNIUM
HAFNIUM is an attack group which have been observed while primarily targeting entities in the United States for the purpose of exfiltrating information from several industry sectors, including law firms, education institutions, defense contractors, NGOs, and others. While Hafnium is based in China, most observations indicate that it conducts its operations primarily from leased virtual private servers (VPS) in the United States.
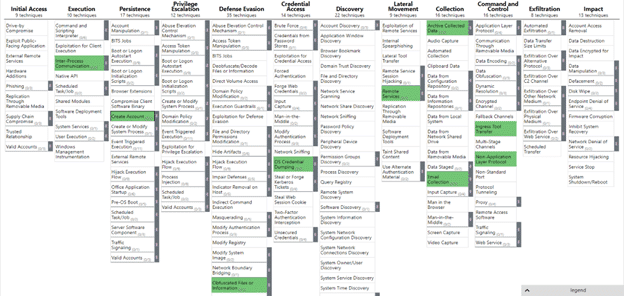
MITRE ATT&CK
The MITRE ATT&CK framework provides security researchers with a high-level overview of the TTPs used by HAFNIUM in their attack:
IOC
Web shell hash:
- b75f163ca9b9240bf4b37ad92bc7556b40a17e27c2b8ed5c8991385fe07d17d0
Paths:
- C:\inetpub\wwwroot\aspnet_client\
- C:\inetpub\wwwroot\aspnet_client\system_web\
- In Microsoft Exchange Server installation paths such as:
- %PROGRAMFILES%\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\
- C:\Exchange\FrontEnd\HttpProxy\owa\auth\