Incident Response at the Speed of Light
As organizations come to the realization that they cannot skimp on security, they are increasingly turning to the services of outside experts to fill the gap that exists between daily security implementations, to security at times of critical need, such as during attack or breach. Outsourcing serves as a quick avenue to meet this need, and MSSPs have been stepping up to meet the challenge with Incident Responder services.
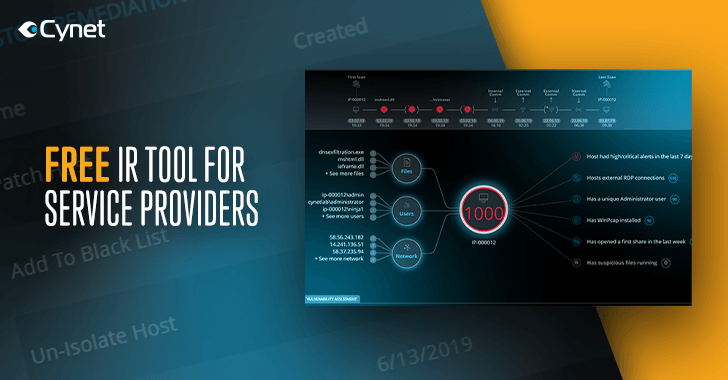
With this in mind, Cynet has launched a free offering for IR service providers, seamlessly deploying in minutes across thousands of endpoints and giving immediate access to the Cynet 360 platform. For the incident responder, this means gaining immediate visibility into the entire environment in one shot – visibility which otherwise could be achieved only by manually installing tools on each endpoint.
MSSPs and their clients get the most advanced solution available for incident response, while their clients also get the ever-elusive peace-of-mind that comes with knowing you have secured the environment.
Cynet’s free offering for IR service providers gives:
-
- Immediate time-to-value – the IR provider is onboarded to take a suspicious environment and return it after validating there is neither malicious presence or activity. Cynet 360 boosts the speed and reliability of this process, enabling the IR provider to deliver faster and scale its operations.
- 60 minutes to full visibility – Cynet 360 automates the collection of incident data, its correlation and analysis, and automates event prioritization and focus by assigning a live risk score to all hosts, processes, user accounts and network destinations.
- Active Threat Detection – if there is indeed an attacker in the network, Cynet will automatically raise a real-time alert upon malicious file execution, attacker-controlled traffic and other post-compromise malicious actions.
- Threat removal – an environment under attack requires a multitude of types of remediation actions to declare it secure again. Cynet provides the largest remediation toolset to apply on infected endpoints, malicious processes/files, compromised user accounts and attacker-controlled traffic.
Learn more and get access to the Cynet free offering for IR service providers.