EXECUTIVE SUMMARY
LockBit is a relatively new Ransomware that started in September 2019, where the developers use third parties to spread the ransomware through any means the third party decides. Once an environment is infected the victim is sent to a payment site managed by the ransomware developers.
A feature of the LockBit ransomware allows threat actors to breach a corporate network and deploy the ransomware to encrypt hundreds of devices in just a few hours.
LockBit threatens to leak the data of their victims to extort payments.
The ransomware itself also includes several technical improvements that show LockBit’s developers are climbing the ransomware learning curve and have developed an interesting technique to circumvent ‘Windows User Account Control (UAC).
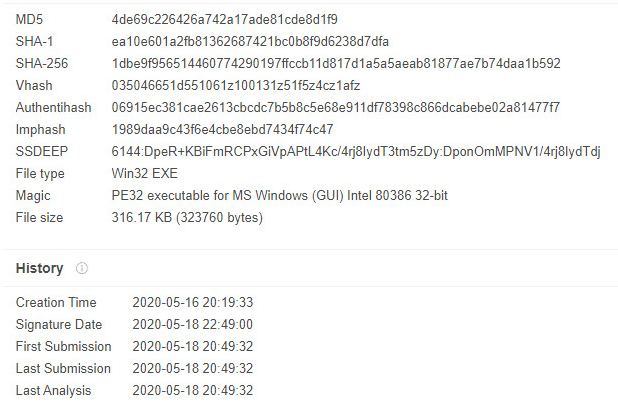
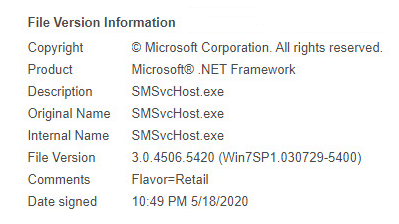
Metadata
As we see above, the file poses to be from ‘Microsoft’, pretending to be legitimate and safe.
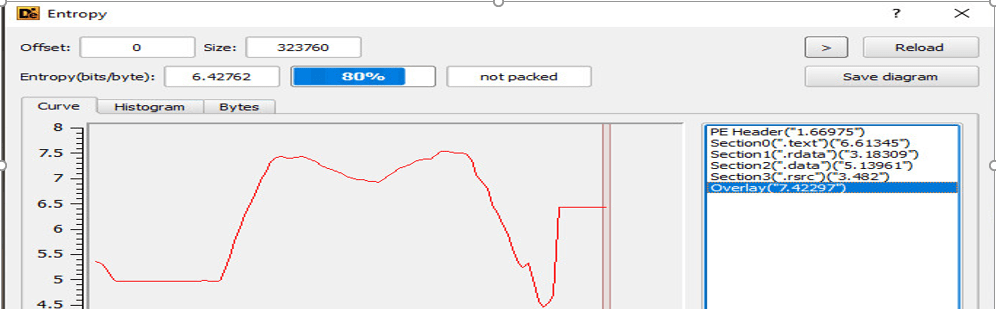
Another indicator we see is statically high entropy levels that the executable has. We can assume that the payload hides under the ‘.text’ sections. Which tells us that the attacker tries evading traditional AV’s mechanism from detecting this file via file scanning on the disk which is signature-based, by compressing the file with a unique format.
Attack Flow
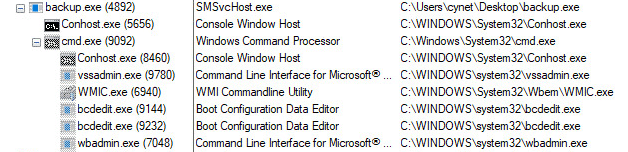
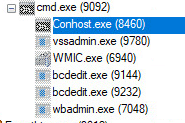
Once the file is executed, the following flow will take place:
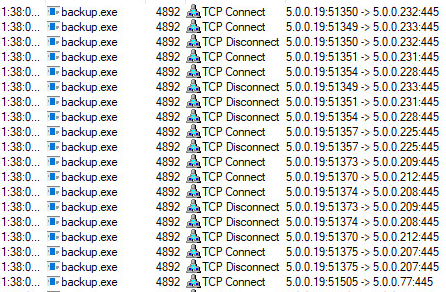
The file scans the entire LAN network and tries to connect to the hosts via SMB port (445) to spread the malicious file all over the internal network.
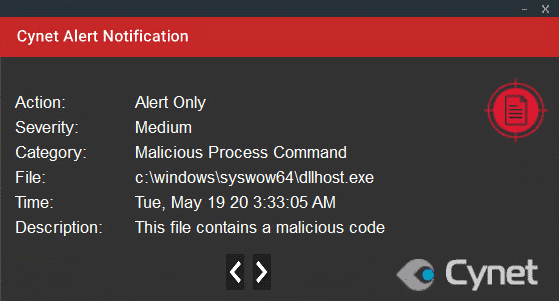
An instance of SVCHOST.exe is running by the process DLLhost.exe which runs with the following command to bypass the need for User Access Control when doing so:
C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7}
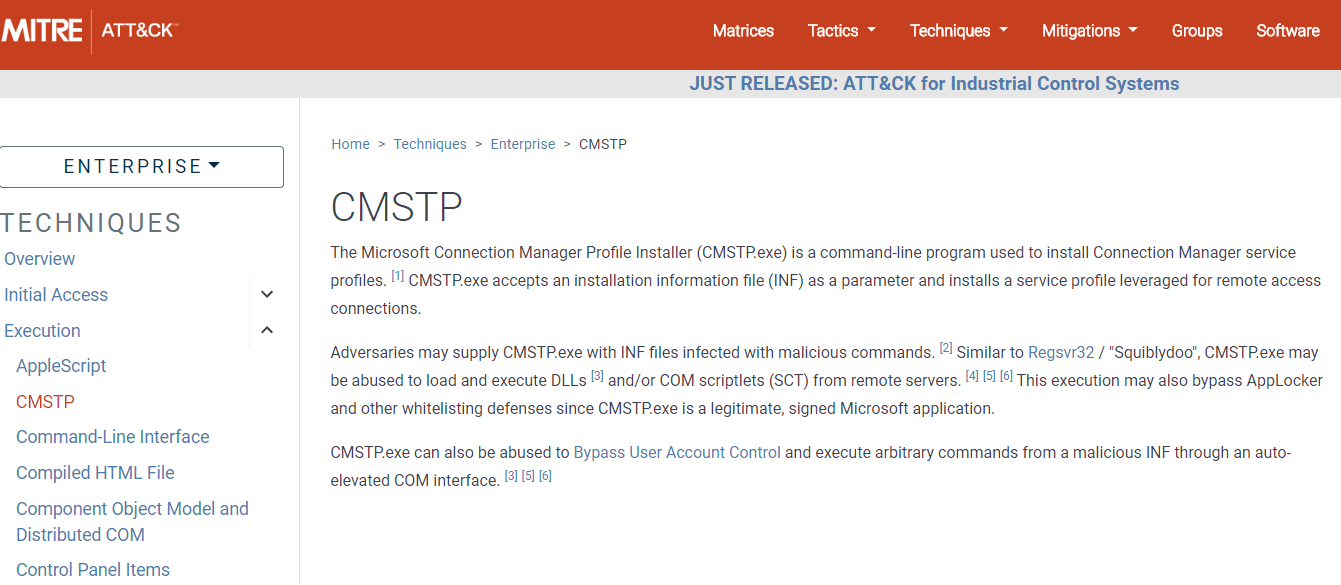
This method is known as CMSTP:
The ‘backup.exe’ file will execute the payload and encrypt most of the user’s files and change their extensions to ‘lockbit’:
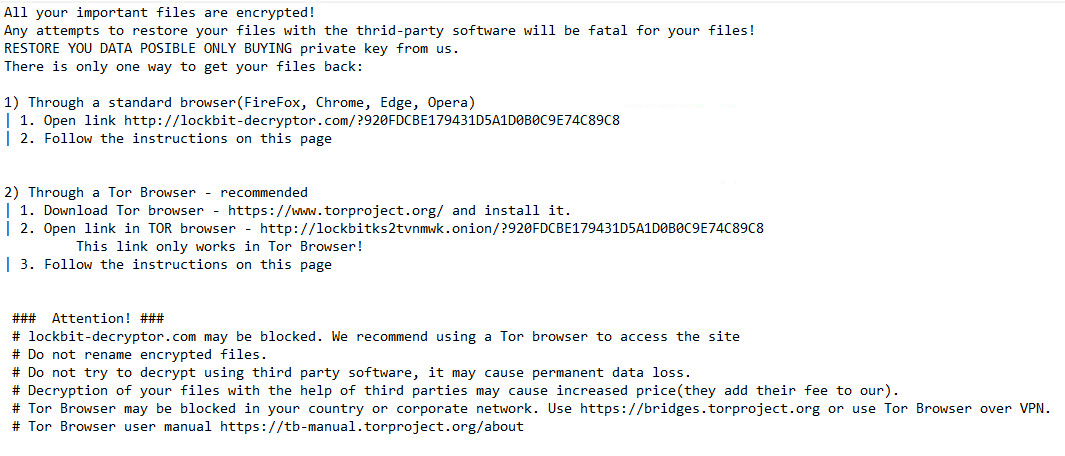
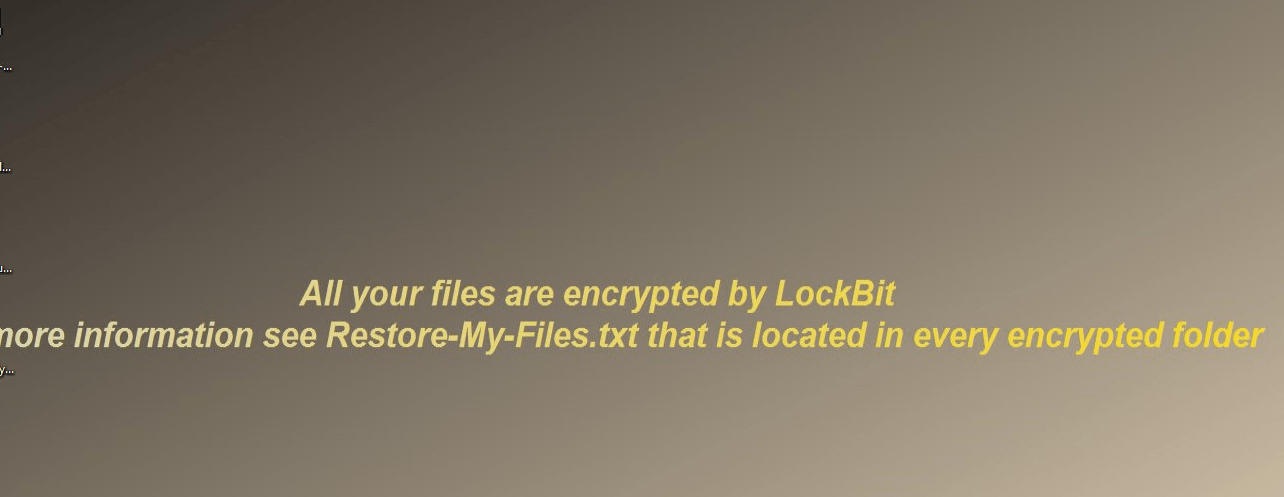
Immediately after, a ransom note called ‘Restore-My-Files.txt’ will be dropped in several folders on the host:
A new instance of CMD is launched to execute the following command:
/c wevtutil cl application
/c wevtutil cl security
These commands are used to clear logs that contain records of login/logout activity or other security-related events specified by the system’s audit policy and applications. The attacker hides their tracks to avoid future forensics on the host by the IT/Security Team.
Persistency Technique
To maintain the persistency of the malicious file on the user’s host, the payload creates a registry key that will execute the file every time the host will startup.
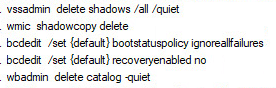
Erasing Backup Copies
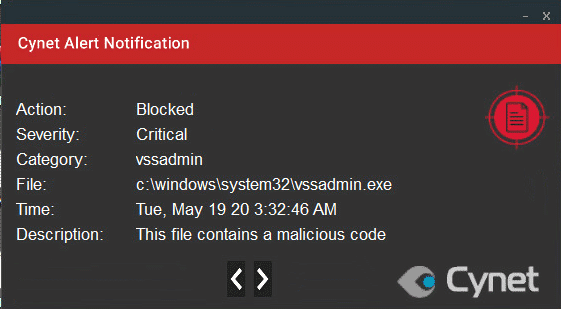
While the files are been encrypted and the note is dropped on the user host, an instance of CMD is launching, executing commands to delete the shadow backup copies, and the backup catalog on the user host by using ‘VSSADMIN’ and ‘WMIC.exe’ to prevent system recovery using ‘bcdedit.exe’ to ignore errors if there is a failed boot/failed shutdown and to disable the ‘Windows Automatic Repair’
Cynet VS LockBit
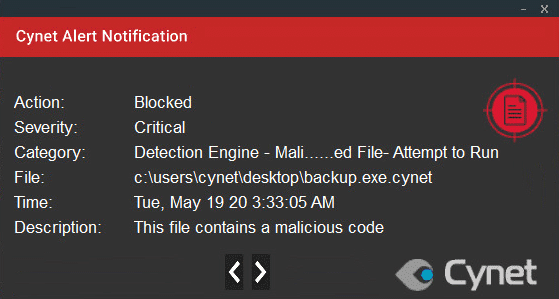
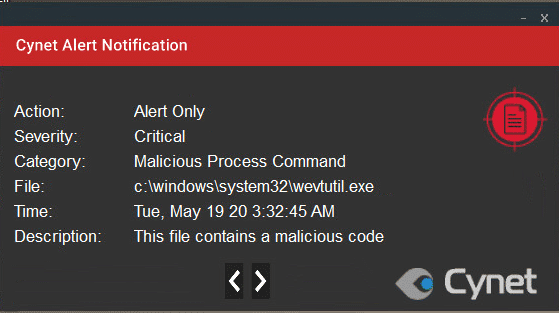
Cynet detects and prevents this attack by using several mechanisms:
Anti-Virus/AI – This alert triggers when Cynet’s AV/AI engine detects a malicious file that was loaded to the memory.
ADT – Malicious Process Command – This alert triggers when Cynet detects a CMD process that executes a command that contains suspicious arguments or is associated with malicious patterns.
RECOMMENDATIONS
- To clean up an infected host, it is crucial to revert each of the steps taken by the payload of the attack.
- Clean the Registry for any of the manipulated values (once infected).
- Delete the malicious file from the paths mentioned under (once infected).
- Blacklist the SHA256 of the ransomware.
- Enabling the heuristic, AV, and driver mechanisms.
- If necessary – format the host and install a clean version of Windows (once infected).
INDICATORS OF COMPROMISE
| Type | Indicator |
| Registry Key | HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\random-generated-letters HKCU\SOFTWARE\LockBit |
| Ransom note names | Restore-My-Files.txt |
| Network IOC’s | Lockbitks2tvnmwk[.]onion
Ocsp.usertrust[.]com Crl.usertrust[.]com |