Cynet 2020 – Fall Platform Release: XDR, Response Automation, and MDR in one platform
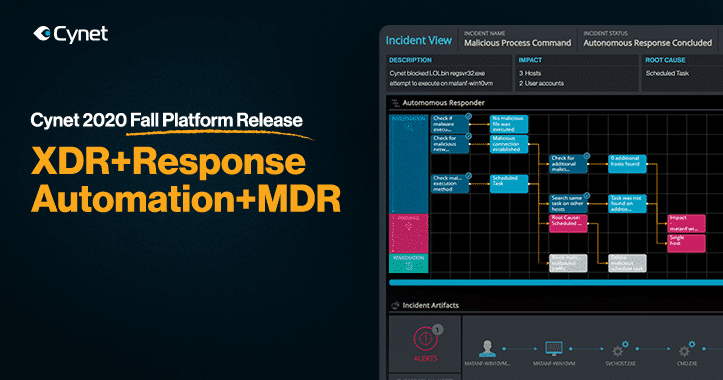
The Cynet 4.0 release includes a major upgrade to the Cynet platform
Most product releases, despite vendor fanfare, provide incremental and often inconsequential improvements. So it’s not often that a company releases a real technology breakthrough as part of a new release. Well, we just did. The Cynet Incident Engine is a game changer for cybersecurity teams everywhere. Coupled with unmatched prevention and detection coverage, the Cynet 360 platform replaces the tremendous time, effort and cost now required to protect an organization from breaches.
To get a full demo of Cynet 4.0 click here
Prevention and Detection
Solution providers take different approaches to detecting and preventing cyber threats, relying on a variety of technologies, such as:
- NGAV – Next Generation AntiVirus (for basic endpoint malware prevention and detection)
- EPP/EDR – Endpoint Protection Platform/Endpoint Detection and Response (for more advanced endpoint protection, detection and response)
- NTA – Network Traffic Analysis (for malicious activity on your network)
- UEBA – User and Entity Behavioral Analytics (to detect anomalous user behaviors)
A new technology category, Extended Detection and Response (XDR), merges these controls on a single platform to better understand threat signals so that you don’t need to purchase, integrate and manage multiple control and integration technologies. This approach provides far better results than when deploying multiple siloed controls and then trying to figure out the stream of alerts and data from each. From day one, Cynet has combined all of these capabilities on the Cynet 360 platform, and adds deception technology as well.
New Incident Engine Redefines Response Automation
Until now, Cynet 360 protection, and all other threat prevention and detection solutions, focused on preventing and detecting malicious activity. This capability is extremely helpful and important for breach protection. Every time a threat is discovered, an alert is generated and the better solutions can automatically remediate the threat.
However, most high-risk alerts should be followed with an investigation to reveal whether the detected threat represents the entire attack or is part of a larger scale operation.
Cynet’s new Incident Engine automates the entire response workflow, including automating investigation to reveal root cause and full impact of the identified threat and a wide set of remediation actions across hosts, process, files, users and network traffic.
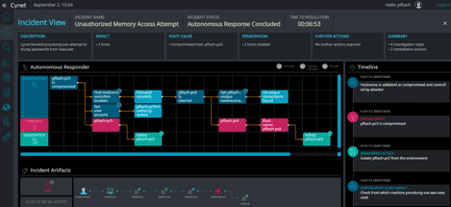
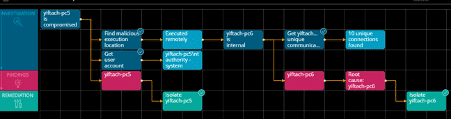
Clicking the Incident View button leads to a totally new page that reflects the full set of investigation steps and remediation actions that Cynet 360 performs:
In the Autonomous Responder graph, the investigation queries and results (blue) lead to findings (red) that are addressed with remediation (green). The Timeline on the right show a more verbose description of every step, while the Incident Artifacts displays the attack flow. The full incident is summarized in the upper text boxes.
In this example, we see an Unauthorized Memory Access Attempt alert that was triggered by an attempt to dump credentials – a common attack that we often encounter. The initial alert indicates that Cynet neutralized the attempt and that the credentials were not accessed. However, the Incident View goes much further: it isolates the compromised host against which the attack was launched, and reveals that a lateral movement – the attack was actually launched remotely from another host in the environment which is the true root cause. This finding is concluded by isolating the root cause host as well.
CyOps – Cynet’s Elite MDR Team
CyOps, our 24×7 Managed Detection and Response (MDR) team, will continue doing what they do best – monitor all client environments around the clock to ensure that dangerous threats are not overlooked and provide expert help on demand. On demand services include ad-hoc threat investigations and forensic analysis, as well as guidance for system tuning and remediation actions. CyOps will continue to be automatically included with the Cynet platform – at no additional cost.
Summary
Full threat protection, coupled with thorough automated response capabilities is a boon to any cybersecurity team. Experienced, but overworked cybersecurity teams that are inundated with alerts and simply don’t have the time to perform full investigation and remediation steps for all threats can rely on the Incident Engine to automate all these tasks for them. The company that simply can’t afford – or find – the expertise necessary to follow all the investigation steps necessary can now have full threat protection available by using the new Incident Engine.