Dynamic Analysis: EARTH GRASS Ransomware
A new ransomware variant named “EARTH GRASS” recently surfaced in the wild. It masquerades as a legitimate Microsoft application to trick users into its execution. When initiated, EARTH GRASS performs actions to ensure that encryption of the host will be complete and uninterrupted, as well as locally irreversible, by deleting and terminating local backup files and services on the host.
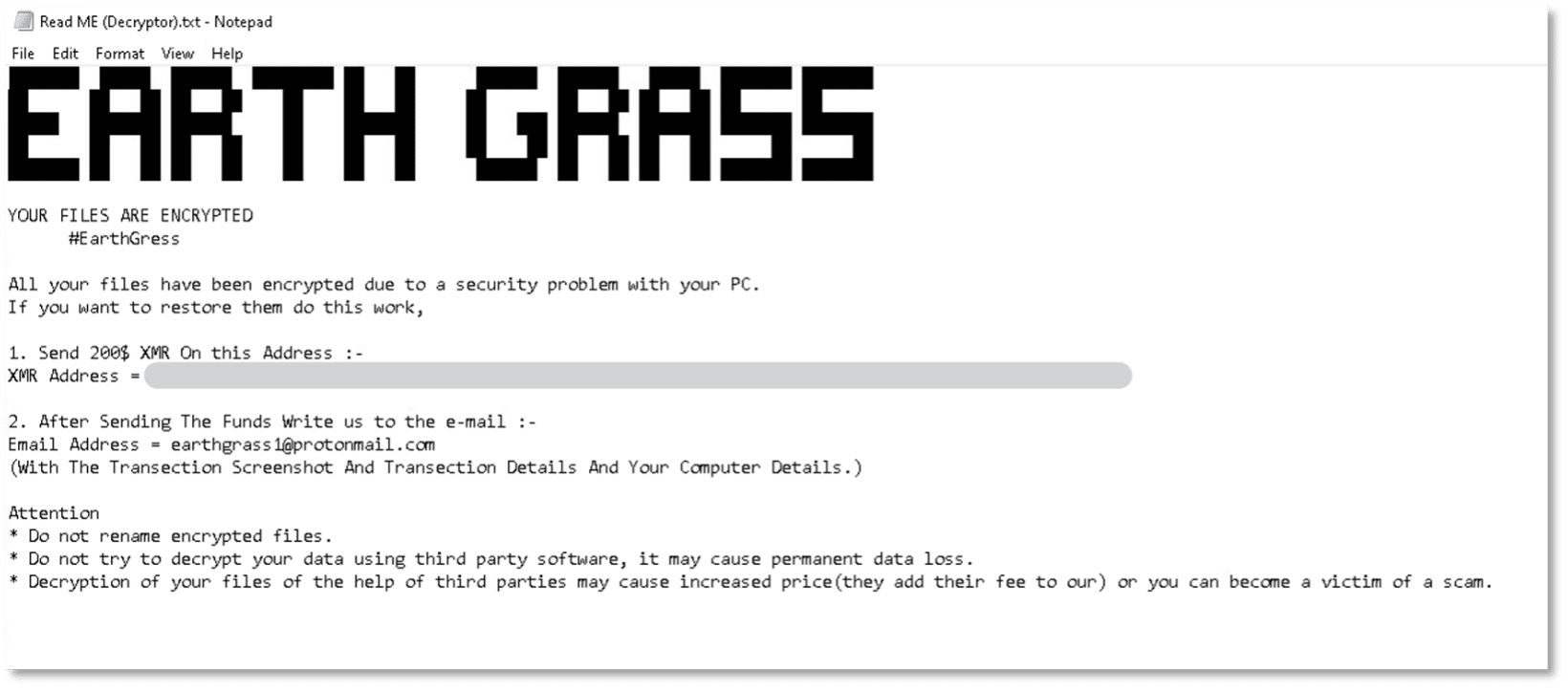
A ransom note from the attacker demands payment in crypto currency in exchange for the decryption of files. It is important to note that complying with the threat actor’s demands will not necessarily remedy the situation and may incentivize further similar attacks by the same and/or additional attackers.
For more, you can review a static analysis of EARTH GRASS or see how Cynet stops the threat in this step-by-step breakdown.
Time to dive into our dynamic analysis!
Dynamic analysis
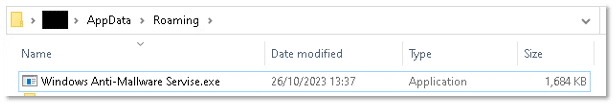
Upon file execution, another executable file is dropped on the host to the path “C:\Users\*\AppData\Roaming\Windows Anti-Mallware Servise.exe”:
This file is then executed, and the main EARTH GRASS executable terminates.
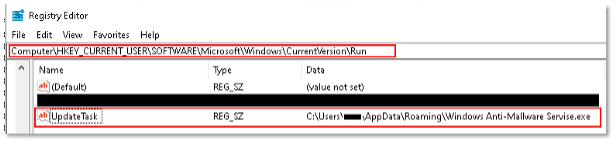
The dropped file initiates its execution by creating a registry Run key named “UpdateTask”, pointing to the malicious dropped file, which ensures the file will be executed automatically with every logon:
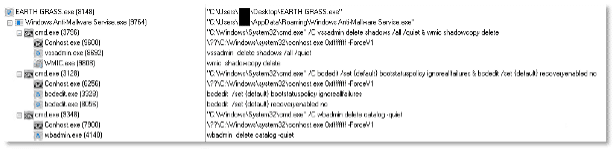
The process continues by running several commands, the same found in our static analysis, to delete any backup files that may be present on the host, and terminates several local backup processes:
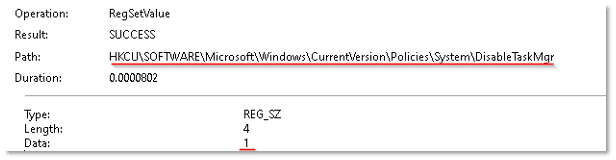
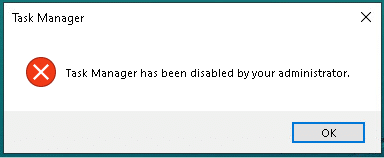
Then, by modifying a registry key, the process disables the ability of the user to open Task Manager, no doubt to prevent the user from terminating the process before it can complete the encryption of their files:
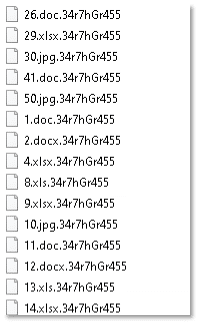
The process then initiates encryption on the filesystem. Encrypted files are appended with the extension “.34r7hGr455”:
The ransom note file “Read ME (Decryptor).txt” is dropped and presented open on the desktop. The note demands that $200 worth of Monero digital coin be sent to a given crypto wallet address in exchange for the decryption of the files:
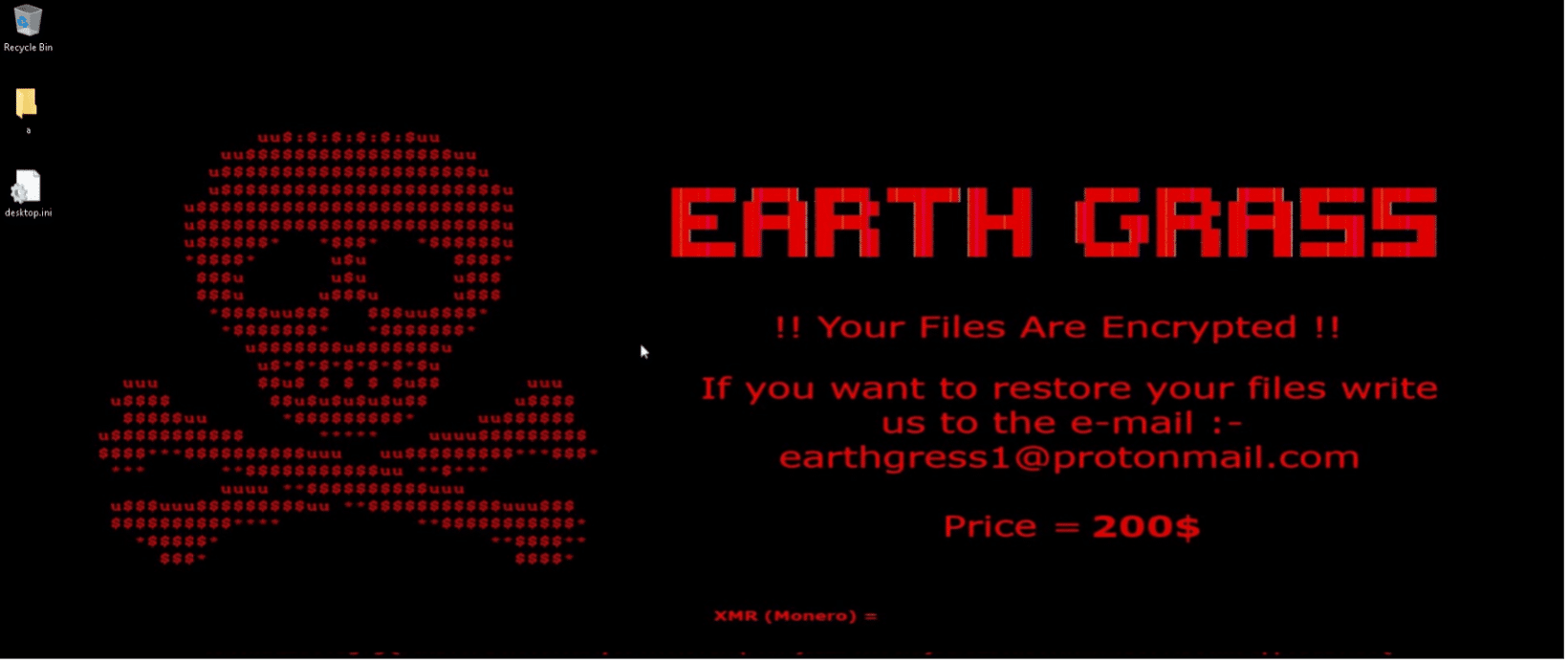
At the same time, the desktop background image is changed to the image we uncovered in our static analysis: