Incident Response Management: Key Elements and Best Practices
Incident response management enables organizations to prepare and respond to security incidents in an effective, thought-out, and resourceful manner. In the detailed guide below, we explain the key elements of an incident response management plan, best practices for incident response management, which tools to use, and expert tips. After reading this article, you’ll be able to better automate and strengthen your incident response management efforts.
What is Incident Response Management?
Incident response management is a systematic strategy that allows an organization to address cybersecurity incidents and security breaches. The goal of incident response is to identify real security incidents, get the situation under control, limit the damage caused by an attacker, and reduce the time and costs of recovery.
Incident response management typically includes formal documentation describing incident response procedures. These procedures should cover the entire incident response process, including preparation, detection, analysis, containment, and post-incident cleanup. By following these procedures, organizations can limit damage, prevent further losses, and comply with applicable compliance regulations.
Key Elements of Incident Response Management
The following are the primary elements of an incident response management program: an incident response plan, a team responsible for incident response, and tools used to facilitate and automate stages of the process.
Incident Response Plan
An incident response plan should specify in detail how your team should perform the following incident response stages, who is responsible for what, and what documentation and notifications are necessary:
- Responding to threats – The action to take that will contain or limit the impact of a detected threat. For example, isolating affected systems or initiating alerts.
- Triaginge incidents to determine severity – Assessing and prioritizing the threat based on its scope, impact, and urgency to determine the right response path.
- Mitigatinge a threat to prevent further damage – Applying temporary fixes or security controls to stop the attack from spreading or worsening. For example, blocking IPs or disabling accounts.
- Eradicatinge the threat by eliminating the root cause – Identifying and removing the source of the threat to ensure it doesn’t resurface. For example, removing malware, compromised credentials, or fixing vulnerabilities.
- Restoring production systems – Safely bringing affected systems back online. This will often require using clean backups, reimaging, or reconfiguring to ensure stability and security.
- Post-mortem and action items to prevent future attacks – Analyzing what happened, documenting lessons learned, and implementing changes to strengthen defenses, for example, updating policies or implementing new security controls.
Learn more in our detailed guide to incident response plan
Incident Response Team
Incident response teams typically include the following roles. Each role should be clearly informed of their responsibilities in the event of a security incident:
- Incident response managers – They lead the response effort by making strategic decisions, coordinating team activities, liaising with management, and ensuring proper documentation.
- Security analysts – They monitor, investigate, and assess security alerts to identify threats and analyze indicators of compromise, so they can recommend response actions.
- IT and security engineers – They implement technical measures to contain and mitigate threats, restore systems, and patch vulnerabilities that may have been exploited.
- Threat researchers – They analyze malware, threat intelligence attacker behavior to uncover attack vectors, identify attribution, and inform defensive strategies.
- Legal and risk management – They advise on regulatory and legal obligations, help manage liability, ensure compliance with data breach laws and industry standards, and help with cyber insurance.
- Corporate communications – They craft and convey clear, accurate communications to stakeholders, customers, and the media during and after the incident.
- Human resources management – They become involved when incidents involve employees. They handle issues like insider threats, policy violations, or disciplinary actions.
External security forensics experts – Brought in for complex incidents. They perform deep-dive forensics, assist with incident reconstruction, and validate internal findings.
Learn more in our detailed guide to incident response teams
Incident Response Tools
To be effective, modern security organizations use technological tools to detect and even automatically respond to security incidents. The following security tools can be leveraged by incident response teams if they are present in the organization’s environment:
- Security Information and Event Management (SIEM)—collects data and logs from applications, infrastructure, network security tools, firewalls, and so on. Correlates data from multiple sources, generates alerts to inform security teams of malicious activity, and enables further investigation.
- Endpoint Detection and Response (EDR)—typically deployed as agents on laptops, workstations, servers, and cloud endpoints. Can detect threats on these devices, enable real time investigation of breaches, and can perform automated mitigation such as isolating a device from a network or wiping and re-imaging it.
- Network Traffic Analysis (NTA)—captures, records, and evaluates network data and communication patterns, looking for suspected malicious traffic. Enables detection and response to security incidents traversing the core network, operational networks, and cloud networks.
- Security Orchestration, Automation & Response (SOAR) – coordinates incident response automatically based on pre-defined playbooks. It helps determine the root cause of attacks, orchestrate remediation actions, and manage the process.
- Extended Detection and Response (XDR) – unifies threat data from isolated security tools. It combines data from various security layers, including email, endpoints, servers, cloud workloads, and network, and provides a unified view of threats even when multiple attack vectors are involved.
Related content: read our guide to incident response platforms
Incident Response Management Best Practices
Here are several best practices that can help you make your organization’s incident response management program more effective.
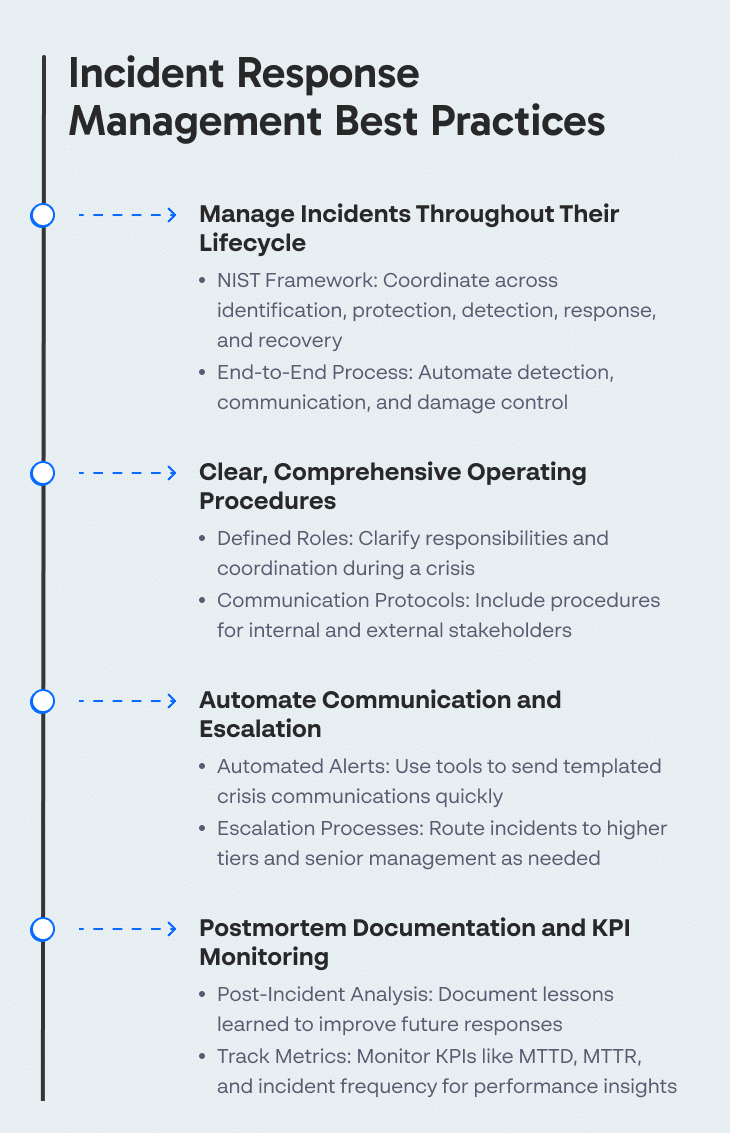
Manage Incidents Throughout Their Lifecycle
According to the NIST framework, the cybersecurity lifecycle includes five areas: identification, protection, detection, response and recovery. An effective incident response management program must coordinate and automate the entire process—from initial detection of an incident to communication, damage control, and lessons learned after an incident has been contained.
Clear, Comprehensive Operating Procedures
Robust incident response management helps security teams stay calm and take the necessary action while the organization is under attack. An important advantage of an organized incident response management process is that it is immediately clear what needs to be done in the early stages of a crisis. Incident response procedures clarify who is responsible for coordinating all resources in the most effective way possible to mitigate the threat.
In addition to technical personnel, the plan should include clear risk management and communication procedures. It should be clear who can speak on behalf of the organization and what they should communicate. There should be procedures for informing lawyers, insurance companies and other relevant internal or external stakeholders.
Automate Communication and Escalation
When a security breach occurs, the organization’s reputation can be seriously affected. It is very important to instruct employees how to communicate in a crisis situation. Automated communication tools allow teams to focus on solving high-priority problems without wasting valuable time during the crisis.
For example, automated communication can take the form of an automated email system that sends templated messages to all relevant parties, based on incident information provided by the response team. Another direction for automation is event escalation—depending on the severity of an event, it can be communicated to higher analyst tiers in the security organization, and if necessary, to other departments and senior management.
Postmortem Documentation and KPIs Monitoring
Postmortem analysis and documentation, after a security incident has ended, is an important part of effective incident response management. It allows employees to turn crisis events into an organization-wide learning experience.
Periodically, the incident response team should perform an analysis of incident response activities and record metrics like the number of incidents per month, mean time to detection (MTTD) and mean time to resolution (MTTR), and downtime rates for affected systems. Tracking these and other relevant metrics over time can indicate the success of the incident response process.
Tips From Expert
In my experience, here are tips that can help you better adapt to incident response management:
- Create playbooks for specific attack types
Beyond generic response plans, develop playbooks for handling specific threats like ransomware, phishing, or insider threats. This ensures rapid, focused responses tailored to the threat type. - Integrate threat intelligence feeds into incident response tools
Leveraging external threat intelligence can help anticipate and recognize threats faster. Integrate these feeds with your SIEM and EDR tools for enhanced detection and contextualized alerts. - Use deception technology to slow down attackers
Employ honeypots, honey tokens, or decoy files to trap attackers and gather intelligence during an incident. This approach also buys your team time to detect and respond to the breach. - Establish a rapid response “SWAT” team for critical incidents
Identify top security talent who can be pulled together quickly for high-severity incidents. This cross-functional team should be trained to respond to critical threats, working as an elite force to minimize damage. - Monitor for signs of lateral movement post-incident
Even after an incident seems contained, continuously monitor for lateral movement within your network. Attackers often leave backdoors to regain access, so proactive vigilance post-incident is crucial.
Incident Response Management FAQ
What is the Incident Response Process (IRP)?
An incident response process covers the entire incident investigation lifecycle, including the following stages:
- Preparation – Building readiness through policies, training, and tools to ensure the organization can respond effectively to incidents in real-time when they occur. It includes defining roles, assembling the response team, and conducting simulations or tabletop exercises.
- Detection – Identifying security incidents through monitoring systems, alerts, and user reports to enable fast response and limit the impact of a breach.
- Analysis – Investigating the nature, scope, and impact of the incident. This involves reviewing logs, system behavior, and potential indicators of compromise to determine the cause and intent.
- Containment – Isolating affected systems to prevent the threat from spreading further. It involves short-term fixes to stop the damage and long-term strategies to prevent recurrence during the response window.
- Post-incident cleanup – Restoring systems to normal operations and closing backdoors or vulnerabilities. The team also conducts a post-mortem to document lessons learned and improve future response efforts.
How does incident management differ from the incident response process?
Incident management is a broader term that encompasses the entire lifecycle of an incident, from preparation to detection to resolution and documentation. Incident response, on the other hand, is a more focused discipline that specifically deals with an incident in real-time. It zeroes in on detecting, analyzing, containing, eradicating, and recovering from malicious attacks or breaches.
What are some common challenges in incident response management?
Many organizations struggle with alert fatigue, where security teams are overwhelmed by the volume of alerts, many of which are false positives. This can lead to real threats being missed or not acted upon quickly enough. Another major challenge is coordination and communication during a live incident. In high-pressure situations, poor communication can lead to missteps, such as improper containment measures, data loss, or public relations fallout. Finally, many organizations lack preparation, like updated incident response playbooks or practicing response procedures, which slows down decision-making and increases the risk of mismanagement.
What is the Role of an Incident Response Team?
An Incident Response Team, also known as the Cyber Incident Response Team (CSIRT), is a group that can include dedicated full-time staff, part-time staff, and third-party vendors. The team is responsible for:
- Proactive incident response planning
- Testing and resolving system vulnerabilities
- Maintaining strong security best practices
- Handling security incidents from detection to closure and recovery
- Analyzing previous incidents and implementing lessons learned
Who Handles Incident Response in the Organization?
To properly prepare and respond to incidents across your business, your organization must have an incident response team, or an outsourced incident response team from a managed security service provider (MSSP) or managed detection and response (MDR) provider.
Whether in-house, outsourced, or a mix of both, incident response teams include security analysts, engineers, threat researchers, and an incident response manager who is ultimately responsible for managing severe incidents. They work closely with other departments including communications, legal, and human resources.
How can incident response tools enhance the efficiency of a response?
Incident response tools can automate repetitive tasks and accelerate threat detection and triage. They can aggregate logs, detect anomalies, and correlate data across the network in real time. This helps teams quickly identify the root cause of an incident and reduces the manual effort required to investigate threats. Automation also ensures that standard response actions can be executed rapidly, minimizing potential damage. In addition, these tools improve collaboration and consistency across teams. This minimizes confusion during a crisis and helps with efficient decision-making.
Which incident response tools work best for small teams?
For small security teams, the best incident response tools are those that offer strong automation, intuitive interfaces, and all-in-one capabilities, reducing the need for manual analysis and multiple point solutions. Tools like Cynet are particularly well-suited for small to mid-sized teams because they combine endpoint protection, detection, and automated response in a single platform. Cynet also includes a 24/7 MDR service, which is valuable for small teams without round-the-clock coverage.
How do I measure the effectiveness of my incident response management?
KPIs like Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), and Mean Time to Contain (MTTC) are commonly used to evaluate how quickly your team identifies, analyzes, and mitigates threats. Additionally, track the number of false positives, repeat incidents, and successful containment efforts. On the qualitative side, post-incident reviews and tabletop exercises can provide valuable insights for continuous improvement.
How often should I review and update incident response procedures?
Incident response procedures should be reviewed and updated at least annually, but more frequent updates are recommended when significant changes occur in your IT environment, threat landscape, or organizational structure. In addition, if you onboard new tools, adopt cloud services, undergo a merger or acquisition, or experience a major security incident, it’s highly recommended to reassess and revise your procedures right away to reflect those changes.
Automated Incident Response Management With Cynet
Incident Response Automation
Cynet provides a holistic solution for cybersecurity, including Cynet Response Orchestration which can automate your incident response policy. Users can define automated playbooks, with pre-set or custom remediation actions for multiple attack scenarios.
Cynet Response Orchestration can address any threat that involves infected endpoints, malicious processes or files, attacker-controlled network traffic, or compromised user accounts.
Learn more about Security Automation and Orchestration
Incident Response Services
Cynet provides Incident Response (IR) services that add deep security experience to its world-class incident response platform. Cynet’s proactive 24/7 security team acts as your extended team, identifying incidents, leading any required analysis, and responding on your behalf. Our incident response services provide:
- Best of breed tech – delivers alerts and insights from endpoints, users and networks. Since everything is automated, we respond faster.
- Fast and scalable IR setup – no need for open source or manual tools. Our platform is easy to deploy, allowing for speed and scale across endpoints.
- Transparent incident response – dedicated IR project manager and point of contact.
- Customized reports – from executive summaries to detailed IoCs that can be exported to CSV for consumption by other systems.
Related Posts
Looking for a powerful, cost effective XDR solution?
- Full-Featured XDR, EDR, and NGAV
- Anti-Ransomware & Threat Hunting
- 24×7 Managed Detection and Response