Search results for:
In 2011, security researcher Benjamin Delpy discovered with Windows WDigest vulnerability. This security hole allows attackers to access internal storage on a Windows system, which holds user account passwords, and also obtain the keys to decrypt them. Microsoft ignored Delpy, and he created an open-source tool that can leverage WDigest to steal passwords.
The tool has since evolved into a powerful platform for compromising user credentials, used by penetration testers and ethical hackers to test the strength of their endpoint defenses, but also by network threat actors to gain unauthorized access to Windows systems.
Mimikatz is an open source tool originally developed by ethical hacker Benjamin Delpy, to demonstrate a flaw in Microsoft’s authentication protocols. Simply put, the tool steals passwords. It is deployed on a Windows endpoint, and allows its users to extract Kerberos tickets and other authentication tokens from the machine.
Since then, Mimikatz has gone through many versions and has evolved into a powerful tool used by hackers to attack authentication mechanisms on Microsoft-based endpoints. The same tool is also used by penetration testers and security staff to evaluate their vulnerability to these types of attacks.
Mimikatz is still maintained by Delpy, and new versions are constantly developed to keep up with updates to Windows operating systems. You can download the latest versions on Github. There are many forks and implementations of Mimikatz, some of which are packaged in popular malicious threat kits, including NotPetya and BadRabbit. At least 20 advanced persistent threat groups have been identified using Mimikatz as part of their arsenal.
Mimikatz has numerous modules that let attackers perform a variety of tasks on the target endpoint. Some of the more important attacks facilitated by the platform are:
The original version of Mimikatz exploited a Windows feature called WDigest that enables Single Sign On (SSO) for large numbers of enterprise users. WDigest loads encrypted passwords into memory together with their decryption key, making it possible for attackers to perform a memory dump and decrypt the passwords.
Mimikatz creator Delpy contacted Microsoft to remediate the vulnerability but was ignored, and was motivated to create his tool. Microsoft eventually allowed users to disable WDigest, starting from Windows 8,1, and in Windows 10 disabled it by default. But the feature still exists and can be enabled by an attacker who gains administrative privileges. Meaning that Mimikatz is still highly effective and can be used to attack Windows 10 endpoints.
Here are a few things you can do on a Windows endpoint to prevent the use of Mimikatz in a cyber attack.
Disable WDigest
Disabling WDigest severely limits the attacker’s options in a Mimikatz attack. Legacy versions of Windows such as Windows XP are extremely vulnerable to Mimikatz because they do not make it possible to disable WDigest. On Windows 7 and Windows Server 2008, you can install a patch (KB2871997) that makes it possible to disable WDigest. On newer Windows operating systems there is a built-in ability to disable this service.
LSA protection
Windows provides the Local Security Authority Server Service (LSASS) that is used to validate local user accounts and remote logins to a Windows system. If the attacker manages to interact with this service, they can obtain unencrypted passwords stored in its memory. LSA protection is an option that prevents untrusted processes from communicating with the LSA. Before Windows Server 2012 R2 and Windows 8.1, LSA protection was disabled by default, and should be enabled to help protect against Mimikatz.
Debug privilege
By default, Windows systems grant the local administrator permission to debug the system. This privilege is used by Mimikatz to communicate with LSASS. A best practice is to disable this privilege on endpoints, because in most cases the user is not a developer and does not really need to perform debugging.
Credential caching
Windows uses a system registry variable to cache password hashes that were recently used, in case the domain controller is unavailable. Mimikatz can gain access to these cached hashes and use them to impersonate user accounts.
You should change the caching policy on endpoints to cache 0 recent passwords instead of the default which is 10. This can be defined in Windows Settings > Local Policy > Security Options > Interactive Logon.
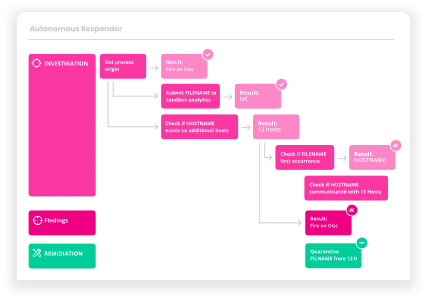
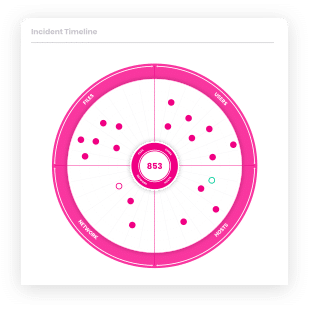
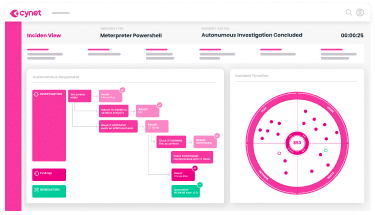
Cynet 360 is a holistic security solution that can help with three important aspects of unauthorized access—network security, endpoint security and behavioral analytics.
Unauthorized access to endpoints is a common cause of data breaches. Cynet EDR continuously monitors endpoints, so defenders can detect the active malicious presence and make swift and precise decisions on its impact and scope.
Behavioral analytics can help detect anomalous activity on IT systems or user accounts. Cynet User Behavior Analysis monitors and profiles user activity continuously, to establish a legitimate behavioral baseline and detect anomalous activity that suggests compromise of user accounts.
Learn more about Cynet 360.
Let’s get started
Ready to extend visibility, threat detection and response?
Prefer a one-on-one demo? Click here
By clicking next I consent to the use of my personal data by Cynet in accordance with Cynet's Privacy Policy and by its partners