See Cynet 360 AutoXDR™ in Action
Prefer a one-on-one demo? Click here
By clicking next I consent to the use of my personal data by Cynet in accordance with Cynet's Privacy Policy and by its partners
Search results for:
There is a huge proliferation of endpoints in organizations: workstations, corporate mobile devices, Bring Your Own Device (BYOD), container-based resources, cloud servers, and more. All of these are attractive targets for attackers, who can bypass the traditional security perimeter and directly target endpoints.
Until not long ago, an antivirus package was considered state of the art endpoint security. Today, legacy antivirus is still important but is only a small piece of the puzzle. In this article we explain how modern Endpoint Protection Platforms (EPP) and a new EPP Security paradigm can help prevent a wide range of evolving threats, as well as allow teams to detect and react to breaches on endpoints across the enterprise via EDR security technology.
To learn how to move beyond EPP with Extended Detection and Response (XDR) solutions, click here.
Endpoint Protection Platforms (EPP) are defined by Gartner as:
“A solution deployed on endpoint devices to prevent file-based malware attacks, detect malicious activity, and provide the investigation and remediation capabilities needed to respond to dynamic security incidents and alerts.”
The first part of the definition – “a solution to prevent malware …” is the next logical step after traditional antivirus. EPP aims to prevent and block a wide range of threats, by providing:
You can learn more about endpoint security in our guides:
The preventive side of an EPP solution can block many types of attacks, including:
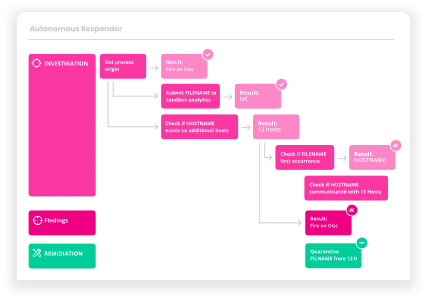
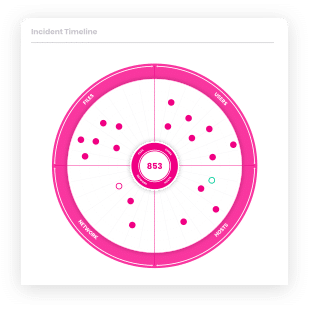
The second part of the Gartner definition – “provide investigation and remediation capabilities” – talks about Endpoint Detection and Response (EDR) technology, which helps security teams react to incidents that occur on endpoints, gather information and take immediate action to contain and mitigate them.
To many in the industry, EPP is only about preventive measures that can block threats on endpoints. But in Gartner’s holistic definition, EPP also includes EDR.
Keep in mind that in the modern definition of EPP, EPP includes both the preventive aspects and also EDR components that allow security teams to respond if a security breach has also occurred.
The differences between these two parts of EPP solutions can be summarized as follows:
| Preventive EPP is a first-line defense that “just works”, it blocks threats without requiring active involvement from security staff. It focuses on protecting each endpoint individually | EDR helps deal with ongoing attacks that have already occurred. It helps security staff identify and respond to security incidents, by aggregating endpoint data from across the enterprise, and executing automatic or manual actions on the endpoint to mitigate the threat. |
Below we show the main system components of the preventive part of EPP platforms, vs. the EDR part.
| Components of Preventive EPP | Components of EDR |
|---|---|
| Legacy antivirus | Data collection via software agents |
| Next-Generation Antivirus | Detection engine to discover anomalies on the endpoint |
| Device Firewall | Data analytics to identify security incidents |
| Application Control | Threat intelligence |
| Device Control | Automated incident response |
| Sandbox |
Before evaluating EPP solutions, do some research about your needs:
Capabilities checklist
Create a checklist and identify, for each of the vendors you are evaluating, who has the points below that are most significant you:
| Infrastructure Capabilities | Prevention Capabilities |
|---|---|
|
|
Learn more in our detailed guide to advanced endpoint protection.
Learn more in our detailed guide to cloud endpoint protection.
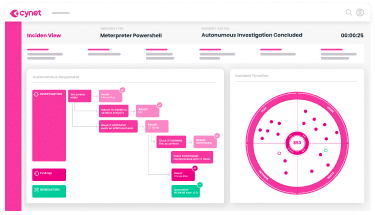
Cynet 360 is a security solution that includes a complete Endpoint Protection Platform (EPP), including Next-Generation Antivirus (NGAV), device firewall, advanced EDR security capabilities and automated incident response. The Cynet solution goes beyond endpoint protection, offering network analytics, UEBA and deception technology.
Cynet’s platform includes:
Learn more about the Cynet 360 security platform.
Let’s get started
Ready to extend visibility, threat detection and response?
Prefer a one-on-one demo? Click here
By clicking next I consent to the use of my personal data by Cynet in accordance with Cynet's Privacy Policy and by its partners