Deploy in minutes
Scale Cynet across as many as 5,000 hosts within minutes to quickly assess your client’s situation and take action.
Reports That You Need
Automatically update your clients with reports ranging from executive summaries to detailed IoCs.
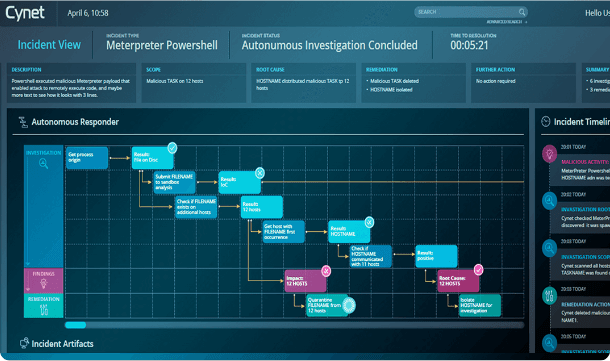
Automatic remediation
Cynet’s automated incident response reduces manual incident handling by 90% for 50x faster results.


.svg)
.svg)
.svg)
.svg)