Automate, Orchestrate, and Respond from a Single, Unified Platform
Security Orchestration, Automation, and Response (SOAR)
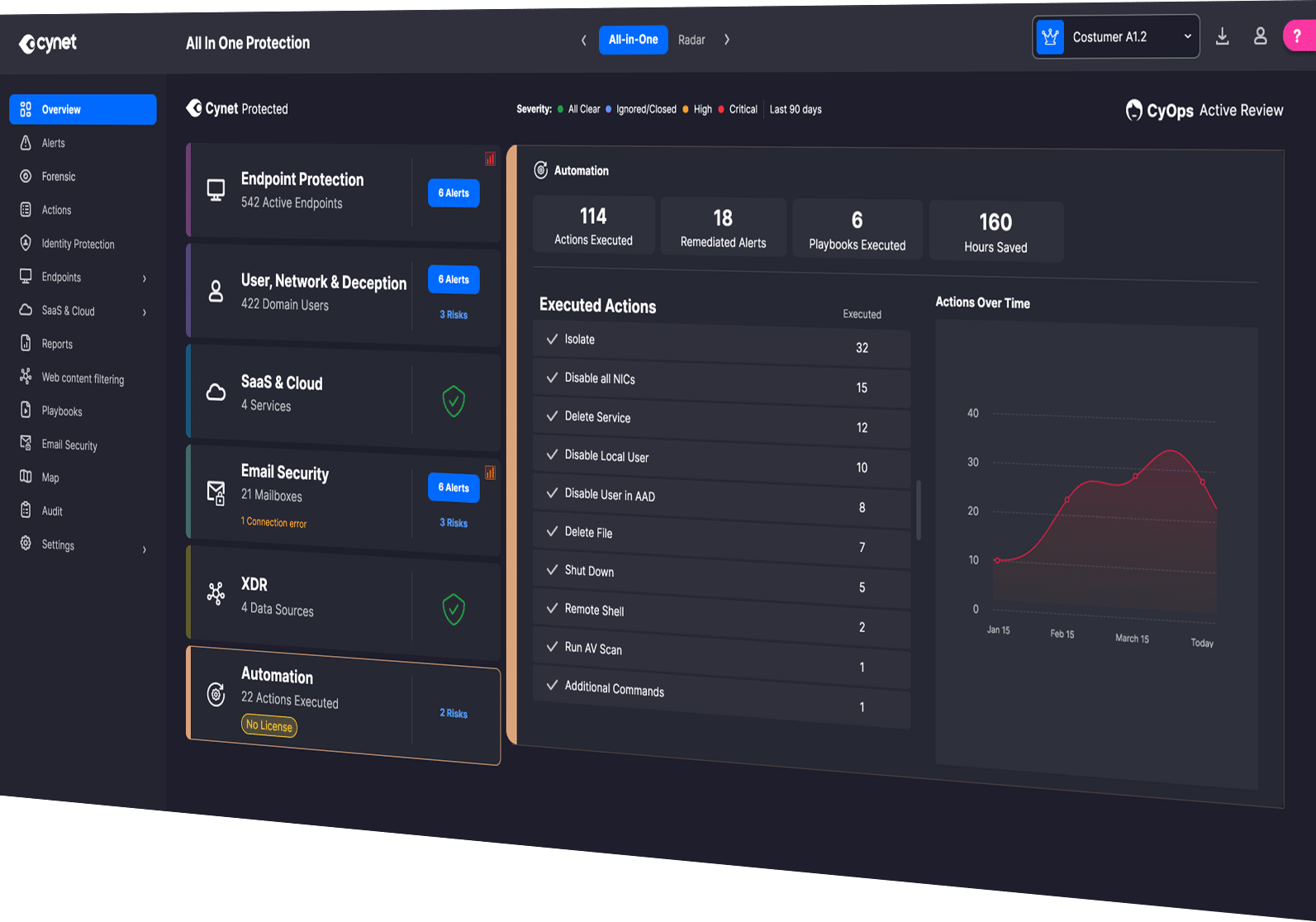
Cynet SOAR puts security on autopilot by unifying detection, investigation, and response across the entire environment. Built directly into the Cynet platform, it eliminates the need for expensive third-party tools while empowering teams to respond instantly and confidently to any threat.
Resolve threats 50x faster and reduce manual incident handling by 90%.
-
Reduce Cost and Complexity
Avoid the costly and resource-intensive implementation and support of a complicated 3rd party SOAR system.
-
Eradicate Attacks Before Damage Is Done
Uncover and resolve all attack components across the environment in seconds – not minutes or hours.
-
Increase Operational Efficiency
Eliminate time-consuming manual tasks by automating workflows and accelerating threat detection, investigation, and response.
-
Enhance Response Skills
Boost the IT and security team’s expertise by leveraging automated best practice investigation and response workflows.
Cynet SOAR
Modern attacks move fast. Manual response slows you down. Cynet’s built-in SOAR automates every step — from investigation through remediation — so you can contain threats in seconds, not hours.
Integrate
Incorporate third party log data into investigation flows and extend remediation action to third party IT components such as switches, firewalls, active directory, and more.
Investigate
Automatically determine the root cause and full scope of an attack across the environment. Includes a graphical timeline and layout of attacks, along with the automated investigation and response actions.
Consolidate
Investigate alerts, remediate threats, orchestrate, and automate incident response workflows across the environment, all from a single pane of glass.
Orchestrate
Cynet Remediation Playbooks automate comprehensive multi-action responses across the environment for any attack scenario. Leverage prebuilt playbooks or easily create customized playbooks with Cynet’s intuitive drag-and-drop Playbook Editor.
Remediate
Eliminate malicious presence and activity across endpoints, networks, users, SaaS applications, and other IT components with the broadest set of remediation actions available from any EDR or XDR provider.
The Cynet Advantage
-
Unified Platform
SOAR is natively built into the Cynet platform — no extra integrations or licenses required.
-
AI-Driven Correlation
CyAI connects signals across endpoints, users, email, network, and cloud for instant clarity.
-
Pre-Built Playbooks
Automate complex multi-stage responses with proven, ready-to-use playbooks.
-
Complete Visibility
Investigate, orchestrate, and automate from a single pane of glass.
-
Expert-Led Guidance
Every action is backed by CyOps 24x7 MDR security experts, ensuring complete accuracy and control.
of threats remediated automatically without human intervention
detection to containment across endpoints and networks
faster response vs. manual workflows
false positives through CyAI continuous learning and validation
Trusted by Security Experts. Built for You.
Every SOAR action is informed by CyOps, Cynet’s 24x7 MDR team of security experts. Together with CyAI automation, CyOps delivers precise, policy-driven response without complexity. You stay in control, while Cynet takes the lead when every second counts.
Put Security Automation to Work for You
Discover how Cynet SOAR simplifies response and scales protection.

