Stop Every Threat. Protect Every Endpoint.
Endpoint Security
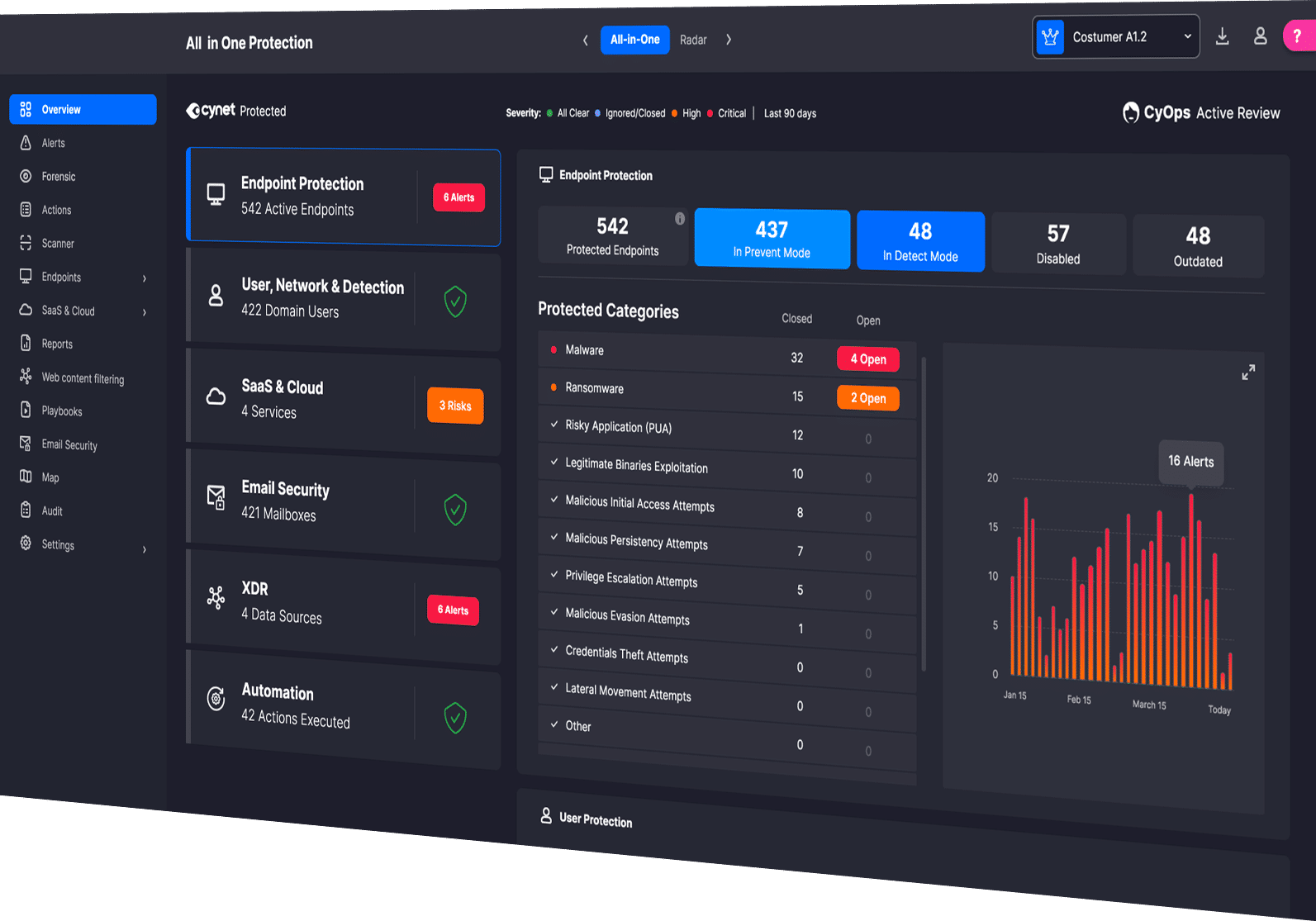
Cynet delivers complete endpoint protection with automated threat detection, investigation, and response through a unified, AI-powered platform backed 24x7 by CyOps MDR security experts.
Jump to Section

Top MITRE ATT&CK Performance
The 2025 MITRE ATT&CK Evaluations included assessments of Endpoint Operating Systems across Windows and Linux environments. Cynet’s EDR, EPP, and ESPM capabilities delivered exceptional results with 100% Detection Visibility, 100% Protection, and 100% Technique-Level Coverage, with zero false positives, and zero configuration changes in the Initial Run.
Not a single vendor performed better than Cynet.
01
Endpoint protection is a core pillar of the Cynet platform. With industry leading performance proven in MITRE Engenuity ATT&CK Evaluations, Cynet EPP includes multiple prevention technologies to automatically stop ransomware, fileless malware, lateral movement, credential theft and zero-day exploits.

Next-Gen Antivirus (NGAV)
Uses AI Static and Behavioral Analysis to detect and stop threats, scanning files pre-execution with signature-based AV and machine learning, and terminating malicious processes at runtime.

Malware Protection
Multiple detection components, including memory patterns, signatures, file behavior, dll loading behavior, access to sensitive processes, etc.

Threat Intelligence
Use over 30 live feeds of various indicators of compromise to ensure your protections are always up to date with the latest threat intelligence data.

Ransomware Protection
Unique logic to protect against a range of ransomware attacks.

Exploit Protection
Detect known attack patterns used to exploit 0-day vulnerabilities.

Critical Component Protection
Detect unexpected access to critical system components.

Memory Access Control
Ensure only legitimate processes can access critical areas in memory.

Fuzzy Hashing
Identify files with high similarity to known malware hashes.

Credentials Theft Protection
Protect against unauthorized access to user credentials.

Critical File & Documents Protection
Defend against unauthorized access to sensitive files and documents.

Device Control Monitor
Monitor, manage, and control access to USB storage devices.

Endpoint Management
Filter and sort for complete control over how endpoints are viewed and managed to focus on the most critical assets requiring attention.

MITRE ATT&CK Integration
Detects and prevents suspicious endpoint activity according to industry standard technique IDs.
02

Windows Events Visibility
Insight (in the forensics screen) into Windows Events that are automatically collected by Cynet.

Full Environment Visibility
Detect even the stealthiest threats by automatically ingesting and analyzing native device, file, network, user, and deception telemetry feeds.

Automatic Remediation
Easily perform and automate remediation actions across the environment.

File & Process Events Monitoring & Logging
Record every file or process action making detailed forensics data available on demand.

Autonomous Detection and Response
Investigate and remediate 3rd party products like Firewalls or Active Directory.

Application and Endpoint Inventory
See all your hosts and the installed applications in your environment.

Memory Access Control
Create complex automatic investigation and remediation steps that will save you hours of manual work. See Cynet SOAR for more.

Active Directory Integration
Block, reset password, move users between security groups as part of the remediation process.

Network Visibility
Log and view Network events such as sockets for each host, user, process and files.
Cynet’s EDR solution continuously monitors endpoint devices to automatically detect, prevent, and remediate threats. The EDR layer supplements EPP to uncover the stealthiest threats hiding on the endpoint. Cynet EDR goes beyond traditional endpoint systems by combining signals across endpoints, networks, and users, along with deception technology to improve visibility, accuracy and protection across the entire attack surface.
03
Cynet provides an additional layer of ransomware protection with extended visibility and protection across endpoints, networks, and users. This uniquely enables Cynet to immediately detect ransomware at the beginning of its attack cycle. With the ability to automatically respond across critical environment components, Cynet stops ransomware processes before files or drives are encrypted.

Windows Events Visibility
Insight (in the forensics screen) into Windows Events that are automatically collected by Cynet.

Full Environment Visibility
Detect even the stealthiest threats by automatically ingesting and analyzing native device, file, network, user, and deception telemetry feeds.

Automatic Remediation
Easily perform and automate remediation actions across the environment.

File & Process Events Monitoring & Logging
Record every file or process action making detailed forensics data available on demand.

Autonomous Detection and Response
Investigate and remediate 3rd party products like Firewalls or Active Directory.
04

Continuous Risk Scanning
Continuously monitor endpoints for both misconfiguration risks and unpatched binaries with known Common Vulnerabilities and Exposures (CVEs).

Risk Prioritization
Prioritize and categorize all identified risks with detailed context, including potential impact and relevant MITRE ATT&CK tactics and techniques.

Risk Reporting
Generate detailed reports on vulnerability risks across your organization, supporting informed decision-making, and demonstrating compliance with security standards.

Mitigation Guidance
Receive expert-led suggestions from CyOps on how to fix and mitigate each vulnerability identified, ensuring a proactive approach to security.
Cynet Endpoint Security Posture Management (ESPM) provides proactive risk management for your organization’s endpoints. By combining industry-leading threat detection with advanced risk mitigation capabilities, Cynet ESPM empowers organizations to quickly and easily identify and address endpoint vulnerabilities before they can be exploited.
See Cynet’s Security Solutions in Action
Experience how Cynet unifies, automates, and accelerates security.

