ESET Endpoint Security is a platform that protects endpoints running Windows, Mac, Linux and Android. Its endpoint platform has a comprehensive feature set, but does not include Endpoint Detection and Response (EDR), which ESET offers as a separate product and prices separately. Read on to learn how ESET endpoint security solutions are structured and the key features they provide.
To learn how to move beyond EDR with Extended Detection and Response (XDR) solutions, click here.
ESET Endpoint Security Suite
ESET provides the Endpoint Security Platform, which includes the following security products:
| ESET Endpoint Security for Windows |
ESET Endpoint Security for Mac |
ESET Endpoint Security for Android |
| ESET Endpoint Antivirus for Windows |
ESET Endpoint Antivirus for Mac |
ESET NOD32 Antivirus Business Edition for Linux Desktop |
ESET Endpoint Security products include the following platform-level features:
- Performance – ESET claims that their endpoint security agent uses the lowest network bandwidth of all endpoint solutions on the market
- LiveGrid – a cloud-based malware protection network. Malicious files found on endpoints are sent to the LiveGrid system, detonated, and results are shared immediately with all endpoints.
- DNA detections – ESET identifies the “DNA” or behavior pattern of a malicious object, and looks for the same behavior in objects detected on an endpoint. This can be effective even if malware is modified or obfuscated by attackers.
- UEFI scanner – checks security of the preboot environment, and notifies about any change attempted to the device firmware.
In addition, ESET provides other products that can help secure and manage endpoints:
- ESET Enterprise Inspector – an Endpoint Detection and Response (EDR) solution
- ESET Security Management Center – a management console for endpoints
- ESET Endpoint Encryption
- Mobile Device Management (MDM) for Apple iOS
In this article we’ll focus on the Endpoint Security Platform and Enterprise Inspector. To learn about other products see the ESET product catalog.
ESET Endpoint Security and Antivirus for Windows/Mac/Linux: Key Features
ESET Endpoint Security is offered as a separate package for Windows, Mac and Linux devices. It offers the following security capabilities:
- Behavioral Detection – Host-based Intrusion Prevention System (HIPS) that uses pre-defined rules to recognize and stop suspicious system behavior.
- Ransomware Shield – evaluates all applications executed on the device by investigating behavior and reputation. Can detect and block processes if they resemble ransomware behavior, even if they don’t match a known threat signature.
- Network Attack Protection – detects both known and unknown vulnerabilities at the network level. Identifies anomalies and can block suspicious network behavior exploiting zero day vulnerabilities.
- Advanced memory scanner – monitors malicious processes and scans them once they decloak in memory, to prevent fileless attacks that do not have a persistent component.
- In-product sandbox – executes malicious code in a virtual environment, emulating different software and hardware to identify its true nature, even if malware attempts to obfuscate itself.
- Exploit Blocker – monitors applications vulnerable to exploits, such as browsers, PDF, Flash and other document readers, email clients, and Java. Broadly examines these apps to find exploitation techniques, not just specific vulnerabilities, and blocks them immediately on the device.
- Two-way firewall – prevents unauthorized access to the network, and also identifies and blocks data exfiltration. Allows admins to define trusted network and restrict all other connections by default.
- Botnet Protection – detects malicious communication that may originate from botnets, and offending processes that may be communicating with them. Blocks and reports any malicious communication.
- Malicious reputation cache – before inspecting a malicious object or process, the product checks a local cache to see if a similar scan has already taken place, improving performance.
- macOS Server support – the Mac version is designed not to interfere with the macOS Server system (version 10.9 and up) and commonly used applications.
ESET Endpoint Protection for Android: Key Features
ESET Endpoint Protection for Android protects corporate Android devices.
- Ransomware protection – evaluates apps on the device and blocks an app if its behavior resembles a ransomware attack.
- Data loss prevention – identifies suspicious data transfers from the device and applies extra protection to sensitive data.
- Application control and audit – allows administrators to define blacklists or whitelists for apps, monitor apps running on Android devices, prompt users to uninstall disallowed applications, track apps by sensitivity and functional categories.
- Remote management – enables security staff to remotely access and control the device to enforce security policies or respond to attacks.
- Mobile device management – automatically notifies users and admins if the device does not comply with security policies.
- Anti-phishing – identifies fake websites that attempt to acquire sensitive data from users and blocks them automatically.
- Anti-Theft – allows admins to remotely lock, wipe, activate a siren, or set specific lock screen messages, when a device is lost or stolen.
ESET Enterprise Inspector (EDR): Key Features
ESET Enterprise Inspector, an Endpoint Detection and Response (EDR) product, is sold separately and is not an integrated part of the Endpoint Protection Security Platform.
Read our articles about Kaspersky Endpoint Security, McAfee Endpoint Security and Symantec Endpoint Protection which do offer EDR built into their endpoint security offerings. Also check out Cynet 360, our holistic security solution which includes endpoint protection with built-in EDR, and additional security capabilities that go beyond endpoints.
The Enterprise Inspector EDR solution provides the following features:
- Threat hunting – helps analysts filter incident data by file popularity, reputation, signatures, behavior, and combine event data with contextual information, to identify APTs and targeted attacks.
- Investigation and remediation – provides built-in rules and lets analysts define custom rules to respond automatically to detected incidents.
- Root cause analysis – shows new security incidents and allows security analysts to instantly view what was affected and where the executable, script, or action was performed.
- Flexible deployment – can be deployed either in the cloud or on-premises depending on organizational and scalability needs
- Behavioral anomaly detection – uses the LiveGrid reputation system to assess whether executed processes are suspicious, and is able to compare users, departments or systems to a broader behavioral baseline to detect anomalous behavior.
- Company policy violation – automatically detects behavior on endpoints that violates company policies, such as cloud storage, Tor browsing, etc. and blocks it on the endpoint.
Endpoint Protection—Prevention, Detection and Protection with Cynet 360
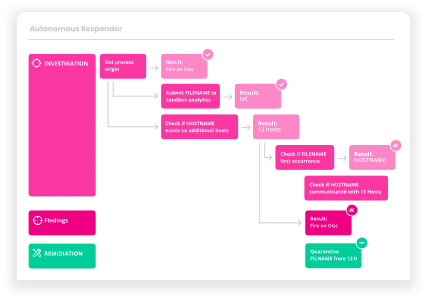
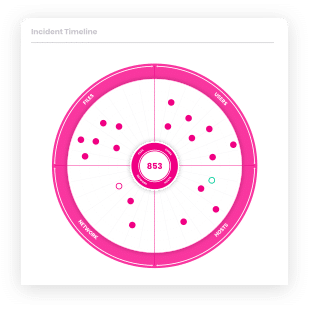
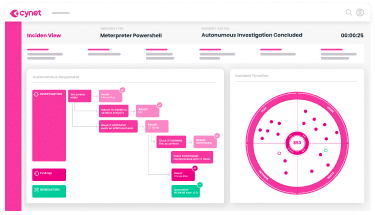
Cynet 360 is a security solution that includes a complete Endpoint Protection Platform (EPP), including Next-Generation Antivirus (NGAV), device firewall, advanced EDR security capabilities and automated incident response. The Cynet solution goes beyond endpoint protection, offering network analytics, UEBA and deception technology.
Cynet’s platform includes:
- NGAV—blocks malware, exploits, LOLBins, Macros, malicious scripts, and other known and unknown malicious payloads.
- Zero-day protection—uses User and Entity Behavior Analytics (UEBA) to detect suspicious activity and block unknown threats.
- Monitoring and control—asset management, endpoint vulnerability assessments and application control, with auditing, logging and monitoring.
- Response orchestration—automated playbooks and remote manual action for remediating endpoints, networks and user accounts affected by an attack.
- Deception technology—lures attackers to a supposedly vulnerable honeypot, mitigating damage and gathering useful intelligence about attack techniques.
- Network analytics—identifying lateral movement, suspicious connections and unusual logins.
Learn more about the Cynet 360 security platform.
How would you rate this article?